Amazon Sidewalk: Cutting Through the Hype
Later this week (tomorrow?), Amazon will enable its new Sidewalk feature. The feature has already gotten a lot of bad press. Much of this comes from the fact that existing devices are automatically used as Sidewalk Gateways, and users will have to opt out. New devices may require a specific opt-in during setup.
Let's first start with what Amazon Sidewalk is not: Amazon Sidewalk is not WiFi. It has WiFi components, but you cannot allow access to your WiFi network if you enable Amazon Sidewalk. Amazon Sidewalk allows for the exchange of specific messages to Amazon's "Sidewalk Network Server."
The use case for Amazon Sidewalk is sensors or IoT devices exchanging messages with applications. For example, a motion sensor may send a message whenever it detects motion, or a Tile tracker may update the network about its location.
Amazon Sidewalk consists of three components:
- Endpoint Device ("Device"): This is the device using Amazon Sidewalk to communicate (for example, location trackers, light switches, or motion sensors).
- Gateway: A gateway receives messages from devices and passes them to Amazon's infrastructure (SNS). Amazon Echo devices or Amazon Ring Cameras are examples of gateways. They are always-on devices that are connected to the internet.
- Amazon's Sidewalk Network Service (SNS): This is the infrastructure Amazon runs to send and receive messages.
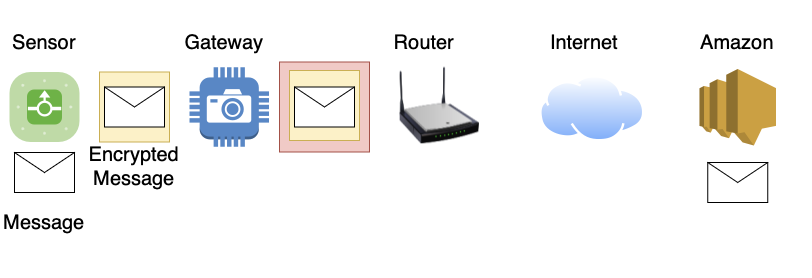
Several radio standards can be used by devices to send messages to gateways. For example, Amazon mentions Bluetooth LE, LoRa, and 900 Mhz Frequency Key Shifting ("Garage Door Openers"). Once a message hits a gateway, it will likely use Wifi to travel to an internet router and from there via the Internet to Amazon's SNS.
Initially, only Amazon devices and applications will be able to use Sidewalk. But Amazon specifically suggests that authorized 3rd parties will be able to participate in the future as well. As a result, you may see various IoT or home automation products that will connect to the Amazon sidewalk or act as a gateway.
To use Sidewalk capable devices, you will need a gateway. But you do not have to share the gateway with others. Your gateway will still work, and your own devices should still be able to use it. Typically you use a device-specific Application to connect to your device or gateway. Then, the same application will be used to configure the device and disable the sharing feature.
A Sidewalk capable device will arrive from the factory with a set of trusted certificate authorities pre-set. It will also include a unique public/private key pair with certificates that are signed by a trusted manufacturer signing certificate. This will be used to identify the device and authorize access to the network. Amazon may block devices that misbehave. Devices will regularly register with Amazon using these certificates and negotiate encryption keys.
Any messages sent by the device will be encrypted on the device and then again by the gateway (the gateway cannot decrypt the messages). The message can only be decrypted on Amazon's SNS as it has the keys for both the gateway and the device (gateways also register with Amazon). Amazon will remember which gateway sent a message from a particular device. To reply or send a message to a particular device, Amazon will send it to the gateway last used by the device.
There are a couple of things Amazon says it is doing to protect the network and the customers:
- The network will be "closed," with only approved developers and manufacturers using it. To use the network, a manufacturer needs a trusted signing certificate. We will see how well Amazon manages the process (like "Marketplace" ?)
- The total bandwidth used by a gateway will not exceed 80Kbps. This network is meant for small messages/status updates. Not for "Web Browsing."
- A gateway will limit itself to 500MB of total traffic. This isn't much but could be a problem on some expensive minimum data cap internet connections (cellular modems or some legacy satellite services)
- Privacy: Amazon says that the gateway will not see any device identifier, and the device will not see the gateway's identifier.
While the network isn't intended for "Internet Access," it will almost certainly be used as a messaging network. It should be trivial to open an approved device and replace the sensor with a device providing values to be sent over the sidewalk. This would retain the certificate infrastructure embedded into the device without having to extract them. As a next step, someone will figure out (or already has?) how to extract the certificates used to authenticate the device and completely re-build them in software.
A lot of the "magic" happens on Amazon's side, and it remains to be seen what Amazon will do with the data. Should you disable Sidewalk access sharing? For the most part: You are already connecting to Amazon's cloud and entrusting Amazon with your security camera's video footage and home automation sensor data just by using Amazon devices. Sidewalk does not appear to expose you to a substantial additional risk. However, there is a possibility that gateways will not implement the protocol correctly, and a malformed message will lead to code execution on the gateway. Give it a couple of weeks/months for people to play with this to see what happens. Notably, a lot of checking and access control is done by Amazon. The gateway will only validate the formatting of the message.
[1] https://www.amazon.com/Amazon-Sidewalk/b?ie=UTF8&node=21328123011
[2] https://developer.amazon.com/en-US/blogs/alexa/device-makers/2020/09/amazon-sidewalk-paves-the-way-for-more-connected-communities
[3] https://m.media-amazon.com/images/G/01/sidewalk/final_privacy_security_whitepaper.pdf
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments