Python Malware - Part 1
Python is a powerful and flexible programming language. It is no surprise that it is also used to create malware.
But Windows, the biggest malware target, has no default Python interpreter. When malware.py is delivered to a Windows machine, it most likely will not execute because there is no Python interpreter installed. Python programs can be converted to binary executable files. A popular tool to do this (also popular with malware authors) is PyInstaller. PyInstaller packages a Python program with all its dependencies and a portable Python interpreter into a stand-alone executable (for Windows, but it also supports Linux and OSX).
When PyInstaller is instructed to package a Python program into a single PE file, the resulting .exe is at least 2.8 MB (or more if there are more dependencies). Reversing a 2.8 MB EXE if no small task. But there are appropriate methods that I will highlight in an upcoming diary entry.
Before you can use appropriate methods to reverse an EXE produced by PyInstaller, you need to identify it. There is a simple method if the default option was used to produce the EXE: it includes the logo of PyInstaller as an icon. I also developed a YARA rule:
import "pe"
rule PE_File_pyinstaller
{
meta:
author = "Didier Stevens (https://DidierStevens.com)"
description = "Detect PE file produced by pyinstaller"
strings:
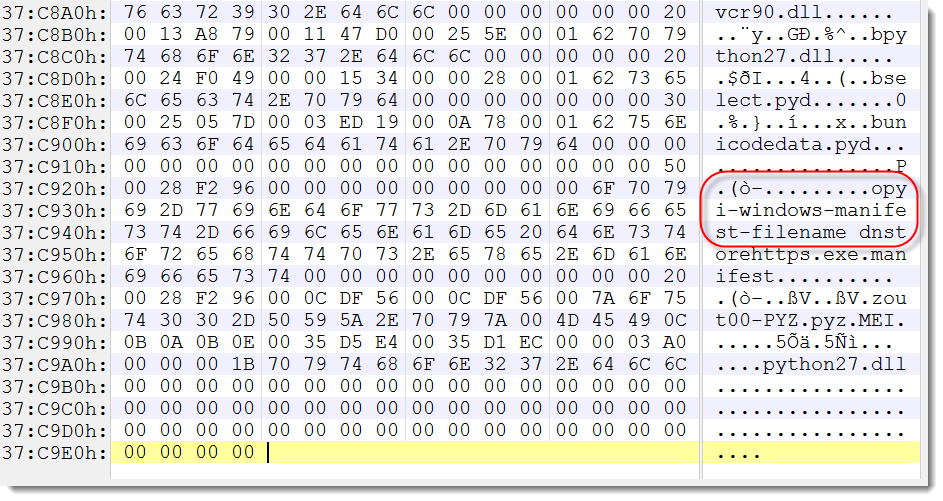
$a = "pyi-windows-manifest-filename"
condition:
pe.number_of_resources > 0 and $a
}
This YARA rule triggers on a PE file with at least one resource containing the string "pyi-windows-manifest-filename".
Or you can open the file with a hexeditor, go to the end of the file, and search for that string:
Didier Stevens
SANS ISC Handler
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
IT Security consultant at Contraste Europe.


Comments