Ongoing Ykcol (Locky) campaign
Today I noticed a high amount of e-mails on my honeypots with similar subject, body and attachment. It caught my attention . After inspecting the attachments and doing some analysis, it was not difficult to realize that those supposed “Status Invoice” messages were, indeed, part of an ongoing campaign pushing a Locky ransomware variant that is being called Ykcol (or Locky in reverse) due to the encrypted file extension (“.ykcol”).
In today’s phishing messages, I noticed an additional subject line “Your Payment” and “.rar” attachments instead of the “zip” ones seen two days ago based on a post from Bleeping Computer[1].
The threat flow of today’s campaign is very simple and can be seen in Figure 1.
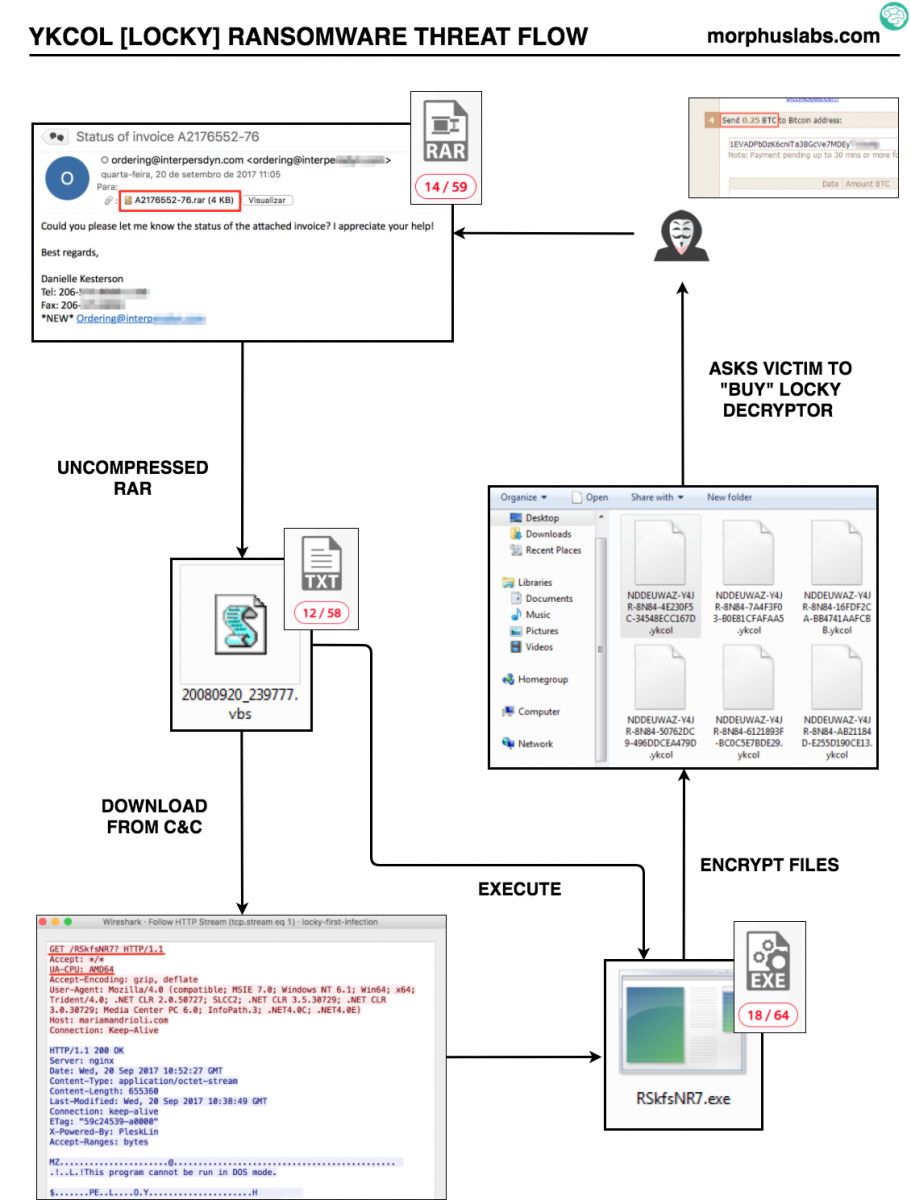
Figure 1 – YKCOL Threat Flow
Indicators of compromise (IOCs)
From the samples I received, it was possible to identify 4 (four) different VBS samples, from which the following IOCs were extracted:
Files:
MD5 (20080920_239777.vbs) = a93845a2e5e4660fb673d949a1f69bc6
MD5 (20080920_387690.vbs) = 2a067fb838be5af230df6a51aa25ea08
MD5 (20080920_441014.vbs) = 638d0a50bf8a166ffed382b7f9935c4e
MD5 (20080920_860397.vbs) = 77482e00daafbb3cec934c98510f0e19
MD5 (RSkfsNR7*) = 83be007cb41eec07e5ae8270cf98a7a6
* Although I tried to manipulate the HTTP POST request changing the parameter “UA-CPU: AMD64” to other architectures, the binary offered by the server in response was the same.
Network:
hxxp://wilvreeburg.nl/RSkfsNR7?
hxxp://ryterorrephat.info/af/RSkfsNR7
hxxp://68.171.49.151/RSkfsNR7?
hxxp://mariamandrioli.com/RSkfsNR7?
hxxp://hard-grooves.com/RSkfsNR7?
hxxp://digiviews.co.uk/RSkfsNR7?
hxxp://pyefittedfurniture.co.uk/RSkfsNR7?
hxxp://hellonwheelsthemovie.com/RSkfsNR7?
E-mails:
All e-mails were sent by “ordering” @ some domain, like: ordering@interpersdyn.com or ordering@calcblog.com with a message like the following one:
Hello,
Could you please let me know the status of the attached invoice? I
appreciate your help!
Best regards,
Final words
Something that caught my attention during YKCOL VBS analysis was that the scripts were not obfuscated and contained lots of code unrelated to malicious activities or C&C communication. As seen in Figure 2, we can see a random function called Anim2UniBall that is not called by the script:
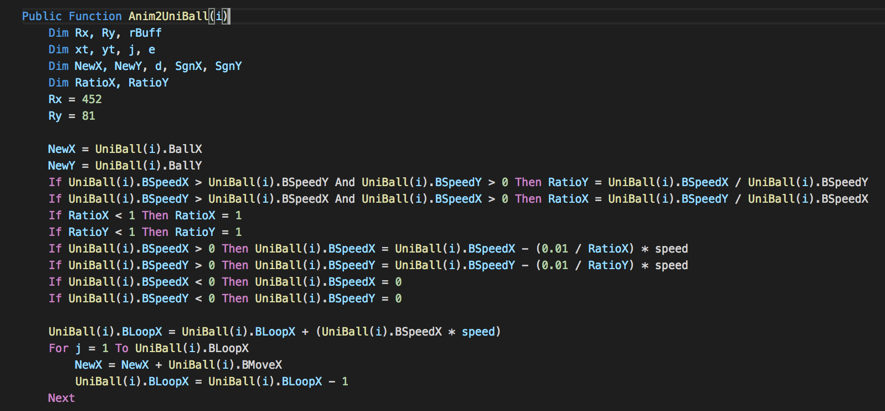 Figure 2 – Random code snippet
Figure 2 – Random code snippet
Searching for this code snippet, I could find many similarities with a gaming framework called OpenARC [2], a clone of a 20 years old game called “Attack, Retrieve, Capture”.
Games apart, not obfuscating and including random code would be a strategy to evade anti-malware euristics? Or maybe trying to trick someone that do not carefully read the code to execute it?
References
[1] https://www.bleepingcomputer.com/news/security/locky-ransomware-switches-to-the-ykcol-extension-for-encrypted-files/
[2] http://openarc.sourceforge.net/index.php?page=about
--
Renato Marinho
Morphus Labs| LinkedIn|Twitter


Comments