Local Malware Analysis with Malice
This project (Malice) provides the ability to have your own locally managed multi-engine malware scanning system. The framework allows the owner to analyze files for known malware. It can be used both as a command tool to analyze samples and review the results via a Kibana web interface. The Command-Line Interface (CLI) is used to scan a file or directory or can be setup to watch and scan new files when copied into a write only directory.
It is modular and is supported by "plugins". Each plugin (malware scanning engine) can be installed in separate Dockers. Beside AV engines, there are other "plugins" for querying Virustotal (register with a key), hash searches using the NSRL database and Team Cymru.
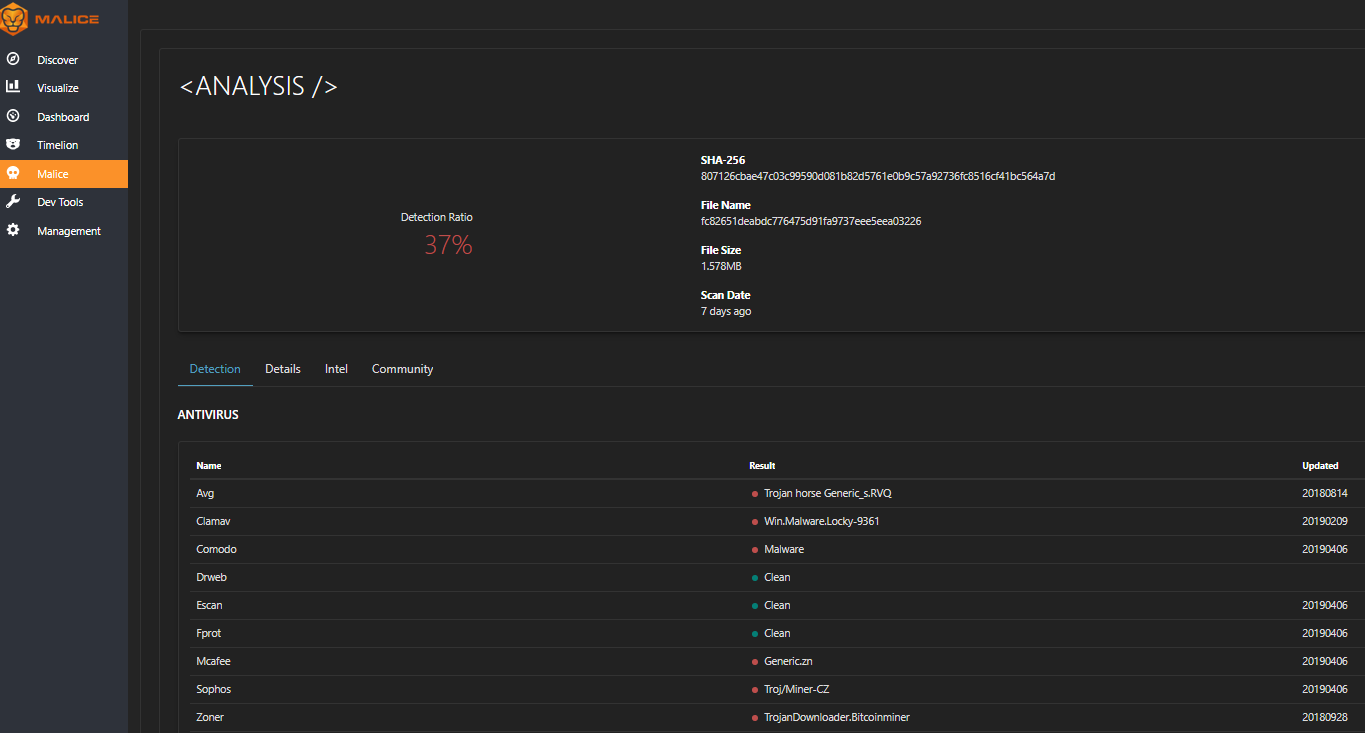
The web/API UI hasn't been added yet but you can setup a write only directory with "malice watch [dir]" option and copy the files to be scanned into it, the results of the scan can be reviewed using the Kibana UI. The documentation is here and the list of available plugins is here. Current support for OSX, Linux and Docker. This is the output viewed from the Kibana interface:
Listing the plugins: sudo malice plugin list --all --detail
Location of plugins: $HOME../.malice/plugins/plugins.toml
[1] https://github.com/maliceio/malice
[2] https://github.com/maliceio/malice/tree/master/docs
[3] https://github.com/maliceio/malice/blob/master/docs/plugins/plugins.md
[4] https://github.com/maliceio/malice/tree/master/docs/installation
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments