Happy new year!
We wish you and your families a very happy 2013 full of peace and prosperity. We greatly appreciate your contributions and we want to thank you because we would not exist without you. We will continue with you next year reporting you the state of the Internet and helping you with the incident response of new emerging threats.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org
How to determine which NAC solutions fits best to your needs
Network Access Control (NAC) is a powerful control used to regulate access to corporate network resources. Some of the goals of a NAC implementation are:
- Mitigation of zero-day attacks: Devices without antivirus, Host IPS, patches, security baseline or specific software installed considered malicious or against security policies should not gain connection to the corporate network.
- Policy enforcement: As NAC use 802.1X technology, it can be used to enforce a specific VLAN for the user and then the network firewall can further enforce access controls inside the corporate network.
- Identity and access management: When used with strong authentication, it can enforce that only allowed computers and allowed users from specific computers can enter the corporate network and its resources.
I decided to implement this control inside my corporate network as it solves many of the risks that are affecting or can affect my company. I will tell you in this diary my experience with the implementation and how to determine which NAC solution fits best to your needs. To start, I designed the following test plan to ensure the NAC solution fits into my information security model:
| Managed | Authentication | 802.1X | MAC | Health | Result | |||||
| Yes | no | User | Host | Yes | no | OK | Bad | VLAN | Network Access Zone (NAZ) | |
| x | Quarantine | |||||||||
| x | x | x | x | Assigned VLAN to user | ||||||
| x | x | x | x | Guest VLAN | ||||||
| x | x | x | x | Guest VLAN | ||||||
| x | x | x | x | x | Pre - Admission VLAN | |||||
| x | x | x | x | x | VLAN redirection according to the registration. If MAC is not registered, access is denied. | |||||
| x | x | x | x | Quarantine | ||||||
Let's talk about some definitions about the last table:
- Managed: Means if the device is managed by the corporation. Examples are Windows Domain or devices managed by a mobile device management software.
- Authentication: NAC authentication can be performed both for user and computer using 802.1X. If 802.1X is not available, MAC addresss is used.
- Health: Set of predefined policies to enforce by checking the compliance of the device being authenticated to the network. Health is OK when the device is compliant with the defined policies and it's bad when one or more policies are not met.
NAC solution handles two portals:
- Guest portal: Used to authenticate devices that are not managed but authorized to enter the network and external users owning or using those devices.
- Remediation portal: When the device does not met the required policies, it's redirected to the remediation portal as a measure to achieve the non-compliant configurations or parameters inside the device.
Both of the portals implicates that any device authenticating to the network by them is always done manually and no servers or critical devices must authenticate this way.
My experience with NAC implementation goes with the purchase made by My company using Mcafee N-550 boxes. So far, we have had the following problems:
- IP Phones must authenticate using 802.1X and voice VLAN must be set and different from the data VLAN. Link Layer Discovery Protocol (LLDP) must be enabled.Check http://www.cisco.com/en/US/docs/switches/lan/catalyst3750x_3560x/software/release/15.0_1_se/configuration/guide/swvoip.html for more information con such configuration in Catalyst 3750 switches and http://www.h3c.com/portal/Technical_Support___Documents/Technical_Documents/WLAN/Access_Controller/H3C_WX3000_Series_Unified_Switches/Configuration/Operation_Manual/H3C_WX3000_CG-6W103/201007/685276_1285_0.htm for H3C devices. Also, please keep in mind that the phone must support the configuration of voice VLAN and data VLAN for the computer device attached to it. Check your IP Phone documentation.
- Guest portal does not work in Internet Explorer 8 and 9. It was solved by a patch released by de Mcafee NAC Developer Team.
- Out-of-Band redundant configuration duplicates registers of authenticated devices when the redundant nodes activates. First answer we got from Mcafee was that the description of the redundant operation is expected and the only workaround was to place filters under the Threat Analyzer Console. I must admit I was suprised by that answer, because I cannot understand how Mcafee is officialy recommending a manual display filter to the logs loosing the real-time report capabilities to the security event correlator and therefore degrading my incident-response capabilities. I rejected that answer and as of today I am still waiting for a solution.
- Authenticated devices with initial bad health state that get fixed won't get new ip address of the VLAN assigned to user because the Radius Change of Authorization (COA) somehow is not correctly working with the NAC solution. Still waiting for an official response for this issue.
So, how can you determine which NAC solution fits best to your needs?
- Smooth network integration is SO important. Ensure that your test plan works within your network, that 802.1X operation works smoothly between your radius, switch, device and user. Don't forget to test RADIUS COA and ensure that VoIP devices support 802.1X and specifically voice and data dynamic VLAN configuration. Make sure to have support from your vendor because usually NAC troubleshooting is really low-level and the technical abilities of the support people must be really advanced.
- Define your Network Security Policy and test if your NAC tool is able to validate each setting you need for your devices. If you have strange devices that cannot fit into a Windows Domain, ensure 100% that they support at least 802.1X. Otherwise, you will be in trouble by allowing exceptions that might be the start point of your future information security incidents. MAC authentication should not be an option as it can easily be faked.
- Make sure the entire NAC process flows and no issues arises like no DHCP negotiation after changing health state from bad to OK.
What is the NAC solution you have found most valuable? Have you had smooth NAC implementations? Let us know!
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org
3 Comments
Targeted zero day attack being used against Internet Explorer 6, 7, and 8
Microsoft have published a security advisory for a zero day attack being used against a "targeted audience" using Internet Explorer 6, 7, and 8. This atypically means corporate or business users still locked in to using these older browsers.
Join Ashley Deuble for MGT 414: SANS® +S™ Training Program for the CISSP® Certification Exam in Brisbane, Australia
1 Comments
It's 3pm 2 days after Christmas, do you know where your unmanaged SSH keys are?
An article that may have gone overlooked since it was published on Christmas by the Washington Times highlights the risks of SSH (or really any public key encryption) when you don't manage the keys and permissions those keys get you. The article interviews Tatu Ylonen who invented SSH in 1995. In essence, the problem isn't the technology but the management of the technology where those who deploy keys simply don't manage them. The private keys are both in predictable locations and easily recognizable (i.e. begins with "-----BEGIN RSA PRIVATE KEY-----") if you have the correct permissions on the machine.
The risk comes in that after keys are no longer used, they generally sit on the machine and still have access to whatever servers they were originally granted access for. In the Linux world, combine this with .history files (for instance) and you can very quickly traverse an entire infrastructure. Unlike digital certificates, there is no expiration date on an SSH key.
The example given in the article is essentially a data-destroying piece of malware automatically deleting data on a machine as it traverses in an intelligent way through an environment with SSH keys. The problem is particularly acute when using keys that do not have passphrases (which is the norm). As there is no way to know if a passphrase is required on the private key, there isn't a good policy-based way to require a passphrase-based key for access as well.
Some mitigations are requiring users to use passphrases on their private keys (and if you have the means to scan them, so much the better), regularly scanning your environment for the presence of SSH keys (grep is your friend) and limiting the locations where the private key is stored. Of course, this only takes you so far.
If it were an easy problem to solve, (or more accurately, a solution that is not labor-intensive) it would be fixed by now.
What do you do to manage your SSH keys (or do you not manage them)?
--
John Bambenek
bambenek \at\ gmail /dot/ com
Bambenek Consulting
4 Comments
Santa's Gift... The Twelve Days of Cyber Christmas
Merry Christmas
Richard Porter
--- ISC Handler on Duty
1 Comments
Merry Christmas!
We wish all our readers Merry Christmas and hope you enjoy a lot with your families tonight. We will continue meanwhile watching what happens on the Internet ;)
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org
0 Comments
Google blocks silent Chrome extension installation
According to chromium blog, Google Chrome 25 won't allow anymore silent extensions installs. This is good, because attacks like the Chrome malicious extension injecting ads to wikimedia pages in may won't happen without the user's consent. This is similar to Internet Explorer Protected Mode, which does not allow extension installations and Firefox add-on control since Firefox 8.
This kind of controls enforce the security settings described in the corresponding security templates of web browsers. So far, the only browser that posess the most scalable security baseline is still Internet Explorer, as there are specific Global Policy Objects (GPO) to apply for Internet Explorer that has been tested and deployed worldwide. Google Chrome also have security templates with the corresponding documentation, but you need to build your own GPO to deploy to a Windows Domain. For Firefox, FirefoxADM is able to generate Security GPO to manage security parameters.
Have you suffered lately any attacks regarding malicious extensions for Chrome? For Firefox or Internet Explorer? Let us know!
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org
0 Comments
Microsoft re-releases MS12-078
Just another quick update informational message for you.
Microsoft has re-released MS12-078 (This is the Open Type and True Type Font vulnerability) here: http://technet.microsoft.com/en-us/security/bulletin/ms12-078
If you are running an affected Windows OS, you may want to take a look.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments
VMWare posts some updates
Just in the case the world doesn't come to a grinding halt today (end of Mayan calendar and all that)....
.... VMWare has posted some updates that you might want to pay attention to over at: http://www.vmware.com/security/advisories/VMSA-2012-0018.html
There are as many as 13 different CVEs covered in this update, so make sure, if you are affected, to patch!
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
1 Comments
A Consumer's Guide to Spotting "Fake" Charities
Earlier in the week we've mentioned that people should be on the lookout for "fake" charities trying to exploit the Sandy Hook tragedy. About 150 or so domains have been registered that are "suspect" and about a dozen I can safely say are fraudulent. Some basic steps we already know about how to deal with this:
- Only deal with charities that are already known to you (i.e. the Red Cross) or that you have a personal relationship (your church or church-related organization, local civic group, etc).
- Don't donate to charities simply by clicking on an e-mail; affirmatively go to website to donate directly.
- Always be sure to check for real contact information, if you don't see anything, don't donate.
That said, let's say you find a website and you want to "verify" whether it is suspect or not. There are several things you can do. Advance warning, this is US-centric mostly because I don't know "charity" laws in other countries, if someone would like to clue me in how to do similar in other countries, feel free to contact me directly.
- Check the domain registration using WHOIS. On online WHOIS tool is here. If it is a "private registration", it is suspect and move along.
- Check with the IRS whether the organization is, in fact, tax exempt. Their lookup tool is here. If the website doesn't have an organization name, it's suspect. If they are talking to you, try to get their tax ID (or FEIN) number. Ask for a copy of their IRS Form 990 (which they are required to disclose). Many states also require charities to register themselves and you can search those filings online as well.
- Check with Guidestar which is sort of a Consumer Reports / Better Business Bureau for charities.
A couple of quick case studies. First, let's use an example where you have information about the "charity" in question. I haven't found anything this detailed for Sandy Hook, but here is one that came up a little while ago during an unrelated matter. The organization purports to help veterans, one of their newsletters is here. Quite helpfully it lists the address, Tax ID number and California business number. Plugging in either Veterans for Change or the Tax ID number at the IRS Website and the State of California Attorney General has some interesting records. Apparently, they tried to get registration information from the person running the charity and they simply ignored the State and were fined.
In this case, you have someone who is purporting some things which are obviously not true, so we'd label this one suspect and move on. Perhaps filing a complaint or two with the appropriate authorities.
Now let's try one of the various domains registered after Sandy Hook. One such domain is hopefornewtown.com. There is no identifying information on the website except an email: hopefornewtown@gmail.com. WHOIS shows the domain has a private registration and the PayPal donate button lists the name as Hope for Newtown. The time it takes to get tax exemption from the IRS is many months so there is no way it's registered, but just in case, the IRS doesn't show such a registration either. File this one under suspect and move on.
If you see any such organizations, you can report to your local state attorney general (which in general is the one who regulates charities, though this may vary), IC3.gov, and you can feel free to send suspicious emails and websites to us using the contact form.
--
John Bambenek
bambenek \at\ gmail /dot/ com
Bambenek Consulting
2 Comments
White House strategy on security information sharing and safeguarding
Today, the White House published its new national strategy for information sharing and safeguarding. See http://www.whitehouse.gov/sites/default/files/docs/2012sharingstrategy_1.pdf for the full PDF (15 pages).
The document touches a key point that has in the past often stymied cooperation and information sharing between the government and the private sector. In my experience, the gov organizations were always very open to receive and soak up information shared with them by private enterprise, but were far less forthcoming with returning the favor. Very rarely did I ever receive intel from government contacts that wasn't either mostly public knowledge, or that I hadn't received already anyway from peers in the industry.
Almost ironically, it is a security problem and security trade-off decision in itself to determine how much realtime security intel can be shared, and with whom, to maximize the benefit without incurring undue additional risk by the intel leaking to the attackers' side. We are - as security professionals - supposed to be good at this kind of judgment call, but our ingrained paranoia often gets into our way. The result is that we tend to be over-cautious with sharing intel, which in turn hurts our peers and ourselves, and helps the bad guys.
As such, I was positively surprised to read in the new national strategy that "collecting intel" seems to slowly but steadily be supplanted by "collecting intel and making timely use of it", which is definitely an improvement for everyone. But the "Top Five" priorities on the summary page 14 seem to me to rather reflect the approach of old again, where "guidelines were developed" and "frameworks were established", but nothing really changed in the real world outside of the Beltway. Which was a bit of a letdown after reading the front portion of the document... but in general, I still find it quite refreshing that the trade-off between sharing and safeguarding is officially recognized, and that there is also a hint of self-reflection in the document that suggests to me that not all is lost :)
If you have any comments on the content of the White House paper, or on security intel information sharing in general, please let us know via our contact form, or use the comments field below.
1 Comments
Challenges of Anti-Phishing Advice, the Google Docs Edition
Coming up with meaningful anti-phishing advice is hard, in part because even the most pragmatic tips cannot be practical in all situations. Scams where the attacker's data-collection form resides at a Google Docs (now Google Drive) are especially difficult to warn users about. After all, the malicious webpage resides at the trusted google.com domain. The effect is especially severe for organizations using Google Apps as a collaboration platform.
Using Google Docs for hosting phishing forms isn't new. F-Secure published several examples of such scams in May 2011; GFI shared additional screenshots in June 2011; Sophos outlined some examples in May 2012.
To understand why such scams aren't going away any time soon, consider the example that came to our attention this month. The malicious email arrived with the subject "Message From I.T Service Helpdesk" and alerted the user, "Your mailbox is almost full."
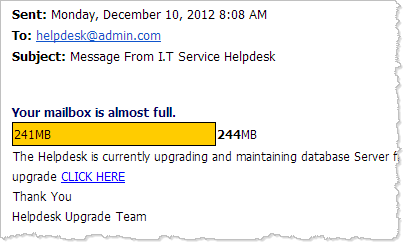
Recipientswho clicked the "CLICK HERE" link were directed to the following "IT HELPDESK SERVICE" page, which prompted for logon credentials that the attacker wanted to capture.
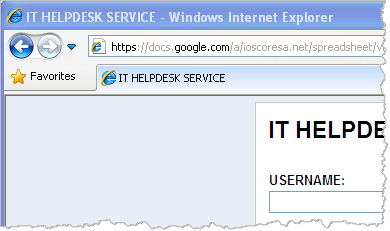
Although the landing page had a very basic look to it, it resided at the domain that most people trust: google.com. The attacker was likely using a compromised Google Apps account of another organization to create a Google Docs spreadsheet and expose its data entry form in the manner shown above.
The use of the Google domain is what lends credence to the phishing scams that make use of Google Docs. The targeted individuals can no longer rely on the advice we often give: Examine the URL bar to confirm that you are at a trustworthy site. This problem is especially severe for individuals whose organizations use Google Aps for email, calendaring and file management needs. In such cases, administrative communications are expected to come through or reside at the google.com domain.
What anti-phishing advice could we offer to potential Google Docs phishing scam victims? There's the more general suggestion of being vigilant and looking out for anomalies, be they an unusual signature line in the email message or an unexpected look-and-feel of the web page. A more specific recommendation might be: Avoid clicking on email links when you need to take important actions that require logging in. Relying on a previously-saved bookmark is safer.
Is that practical advice? Not for all situations. This is what makes anti-phishing advice so challenging to provide.
-- Lenny Zeltser
Lenny Zeltser focuses on safeguarding customers' IT operations at NCR Corp. He also teaches how to analyze malware at SANS Institute. Lenny is active on Twitter and Google+. He also writes a security blog.
8 Comments
Mitigating the impact of organizational change: a risk assessment
0 Comments
All I Want for Christmas is to Not Get Hacked !
With the holidays coming up, you might think it's time to stop thinking about security, malware and generally anything to do with work. Unfortunately, in the area of security, the holidays are not the time to let your guard down. It's always fun to see the up-tick in malware over significant holidays, because the malware authors plan for the time windows when their targets (that's you and yours) and the AV vendors are at reduced staff levels
So, what should Corporate IT folks be thinking about?
Before your users go home for the holidays, ensure that everyone has their Antivirus set up to auto-update over the web. In some corporate setups, AV clients update from a corporate server. If your user community is all offsite over the holidays, they won't get their updates when they need them the most. Which means that some of your users will come back in January infected, and (likely) with their AV turned off by the malware they've picked up.
Similarly on the OS Side - if your users are using WSUS or some other central update service, you likely want them to either update over the internet, or force them to VPN in to get updates. There's nothing like a zero day loose on your corporate network to make for an exciting January!
If you are on the security team, keep track of your system logs. In particular, keep track of backup logs and IPS logs. Even little stuff missed over the holidays does nothing but get worse over the two weeks we have off!
Think about spam. We're all expecting a flood of e-cards in our mailboxes from friends, family, customers, vendors, and other people we do business with. Mixed in with these expect to find some malware, and maybe even some new, ingenious malware. It's a good idea to send a note to your users to let them know to look out for spam that might get past the filters. Remind them that if a website or an email attachment tells them that "they might be infected", they should close that window or maybe even instruct them to reboot to kill it (you'd be surprised how many folks will press "OK" to close a window).
Think about new devices. Off-brand picture frames have come with malware in the past, but you could just as easily see malware on cameras or those keychain picture frames. Really, anything with a USB port that might be infected, even stuff you might not think about like USB powered remote control helicopters and cars - - yes, some of your users will plug these into their corporate laptops to charge, even if there's a charger in the box.
Your users will absolutely come to back to work with new tablets, mp3 players and phones - all of which "must" have a network connection. If you don't already have a plan (and a written policy) for dealing with these, you may have an uphill battle ahead of you (or maybe it's a battle you might have already lost)
Whatever it is, if you're in IT, expect an evil present or two from your users in January.
What should you be thinking about if you're at home, and you're NOT in IT?
Well, all the same stuff. Be sure that all the computers at your house are updated, and have up-to-date AV protection. Think about e-cards and other holiday spam and malware when you open mail. Think about USB and network attached devices after it gets unwrapped and eveyone wants to start plugging cables in.
And think about your extended family who might be calling you after "everything got really slow on our computer after Christmas, right after we uploaded our pictures to that new picture frame".
Because we all know that even if we're not in the IT department at work, we're certainly an "IT department of one" after we get home !
Have a good, safe holiday everyone !
===============
Rob VandenBrink
Metafore
0 Comments
Reminder: Java 6 end-of-live February 2013
Reader Josh reports that while downloading the latest version of Java 6 (version 37) from Oracle's website he received a reminder from Oracle that Java 6 will reach end of life in February 2013. After February 2013 security updates will only be available to customer who purchase extended support contracts. If you haven't already done so, now is a good time to mark your calendars for this upgrade. More details are available here:
http://www.oracle.com/technetwork/java/javase/eol-135779.html
Mark Baggett
8 Comments
Watch for Newtown Connecticut scam sites
Following the tragic events in Newtown Connecticut last week several new domain names related to those events have been registered. I have little doubt that many of these site are owned by charitable and caring individuals or organizations who want to assist families in their time of need. Other sites may belong to political organizations who will attempt to further their side of an argument as a result of this tragedy. Still other sites will undoubtedly belong to scammers who will capitalize on peoples desire to help by establishing fake charities. I spent a few hours going through many of the newly registered domains. So far most of the sites are still under construction with very little to look at. I expect that will change over the next few days. If any readers receive spam related to the tragedy please let us know.
Thanks,
Mark Baggett
0 Comments
SSH Brute Force on Non-Standard Ports
One of the Handlers here at the ISC reports seeing an increase in SSH attacks on non-standard ports. The traffic that is being seen is a brute force SSH attempt, and is more than just a connect, it is providing credentials in attempt to gain access. If anybody is seeing similar SSH attempts on non-standard ports, we'd love to take a look at any logs or packet captures related to this activity. These logs and packets can be reached at the "Contact Us" page.
tony d0t carothers --gmail
0 Comments
ISC Feature of the Week: Webhoneypot: Web Server Log Project
Overview
We recenlty updated the webhoneypot pages at https://isc.sans.edu/webhoneypot/index.html and added some API functions at https://isc.sans.edu/api/. The Webhoneypot project is a collection of logs submitted by users from various honeypots.
Features
The right column navigation is always present and has links to:
- Webhoneypot home page
- RFI Attacks - List of URLs matching RFI regular expressions
- Filter Reports - search our reports for matches to particular header properties
- Reports List - Explained in detail below
Web Application Logs - https://isc.sans.edu/webhoneypot/index.html#logs
- Explains how to sign up and participate as well as requirements to submit logs.
- Link to ISC/DShield API where we have added functions for the webhoneypot
Results - https://isc.sans.edu/webhoneypot/index.html#results
-
Reports - https://isc.sans.edu/webhoneypot/index.html#reports
- Links to available reporting at https://isc.sans.edu/webhoneypot/reports.html
- Overall Report Volume - Total reports, submitters and average per submitter sorted by date
- Attacks By Type - Regular expressions determine the types of attacks. Page lists two tables. One lists the top 30 attacks for the last month, the other table the top attacks for the last 24 hrs.
- Top Unclassified - List of URLs no recognized by regular expressions.
- Unique URLs - Distinct URLs per day with date selection form.
- Headers - Unique headers per day with link to details page. Also has date selection form.
-
Report Volume - https://isc.sans.edu/webhoneypot/index.html#volume
- summarized the report volume received over the last 10 days.
-
Top Attacks - https://isc.sans.edu/webhoneypot/index.html#attacks
- We try to classify attacks based on regular expression matches. This system was created by SANS Technology Institute (STI) Master of Science graduate Eric Conrad as part of his software security requirement. Not all "hits" to a honeypot can easily be identified as "attacks", and some may actually just be benign.
-
Top Attack Groups - https://isc.sans.edu/webhoneypot/index.html#groups
- Grouped top attacks found by regular expressions for the current day
Please consider running a honeypot yourself expect to see more about this project and additional APIs in the future!
Post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center https://isc.sans.edu
0 Comments
What if Tomorrow Was the Day?
[guest diary submitted by Russell Eubanks]
If you knew your network was going to be attacked tomorrow, what specific actions would you take today? Treat yourself to lunch at your desk as you consider the following suggestions.
Look for opportunities to improve your detection capabilities. In your security lab, try changing operating system and application configurations to see if your current policies are able to detect and alert on these actions. If not, create new alerts that are labeled with the action you used to generate these events. This a great foundation to actively seek the activity that you are currently missing.
Update the contact information for everyone on your Incident Response Team. Be certain that everyone you have listed knows they are a part of the team and understands their role when an incident occurs. When was the last time you held an exercise to make sure that everyone listed on the team can be reached in an acceptable amount of time? Schedule an update for the team today. Consider providing them with lunch or an another appropriate token of your appreciation for serving on the team.
Leverage data from the Top 100 Source IP addresses as seen by the SANS Internet Storm Center at http://isc.sans.edu/ipsascii.html. Consider a daily report that shows the traffic between your hosts and those found on this list. Traffic to and from these hosts may not indicate an attack, but may very well prove worthy of your investigative efforts.
Create new alerts based on information found in your logs. These alerts can be scheduled to run every few minutes and configured to notify you if more than zero occur. Pay particular attention to trends that stand out over time. Can you determine the normal usage patterns over a given time period? How would you know if something outside of this baseline started to occur or stopped occurring? How quickly would you know if a critical system stopped sending logs to you?
Schedule and perform regular security architecture reviews. Start with a copy of your network diagram and assume the role of your attacker. Determine how its current defensive and monitoring capabilities could be defeated. Make sure you can detect this type of attack going forward. Implement changes based on that review session today to prevent that type of attack from succeeding. As a final step in this exercise, update your network diagram to reflect any changes you made.
Become familiar with the 20 Security Controls http://www.sans.org/critical-security-controls as a means to implement or enhance your continuous monitoring capabilities. Spend some time on the website to learn about the controls and how they can be applied in your network. Focus specifically on the Quick Wins section on each control to get a better sense of the intent behind each objective. If starting fresh, Controls 1 and 2 could very well be a good place to start.
Finally, use the following suggestions as a means to be intentional about network security monitoring. Conduct recurring IRT peer reviews to solicit their suggestions for improvements. Publish regular reports to the IRT, noting specific items that would be useful to the team. Invite the IRT to subscribe to the SANS Internet Storm Center Daily Podcast at https://itunes.apple.com/us/podcast/sans-internet-storm-center/id304863991. Make a recurring calendar appointment to do this activity with your IRT over and over again.
What additional suggestions do you have that support intentionally monitoring the security of your network?
3 Comments
Microsoft December 2012 Black Tuesday Update - Overview
Overview of the December 2012 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS12-077 |
Internet Explorer Cumulative Patch (Replaces MS12-063 MS12-071 ) |
|||||
|
Internet Explorer 9/10 CVE-2012-4781 CVE-2012-4782 CVE-2012-4787 |
KB 2761465 | No. |
Severity:Critical Exploitability: 1 |
Critical | Critical | |
| MS12-078 |
Windows Kernel Mode Drivers Remote Execution (Replaces MS12-032 MS12-075 ) |
|||||
|
Kernel mode drivers CVE-2012-2556 CVE-2012-4786 |
KB 2783534 | No. |
Severity:Critical Exploitability: 1 |
Critical | Important | |
| MS12-079 |
Microsoft Word RTF Data Remote Code Execution (Replaces MS12-064 ) |
|||||
|
Word CVE-2012-2539 |
KB 2780642 | No. |
Severity:Critical Exploitability: 1 |
Critical | N/A | |
| MS12-080 |
Windows Exchange Server Remote Code Execution (Replaces MS12-058 ) |
|||||
|
Exchange Server |
KB 2784126 | Yes. |
Severity:Critical Exploitability: 1 |
N/A | Critical | |
| MS12-081 |
Windows File Handling Remote Code Execution (Replaces MS07-035 MS11-063 ) |
|||||
|
Windows CVE-2012-4774 |
KB 2758857 | No. |
Severity:Critical Exploitability: 1 |
Critical | Critical | |
| MS12-082 | DirectPlay Remote Code Execution | |||||
|
DirectPlay CVE-2012-1537 |
KB 2770660 | No. |
Severity:Important Exploitability: 1 |
Critical | Important | |
| MS12-083 | IP-HTTPS Security Feature Bypass | |||||
|
Direct Access
|
KB 2765809 | No. |
Severity:Important Exploitability: 1 |
Important | Important | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
-
We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
(**): The exploitability rating we show is the worst of them all due to the too large number of ratings Microsoft assigns to some of the patches.
------
Post suggestions or comments in the section below or send us any questions or comments in the contact form
--
John Bambenek
bambenek /at/ gmail.com
Bambenek Consulting
6 Comments
Joomla (and WordPress) Bulk Exploit Going on
We've gotten some reports and discussion around many Joomla (and some WordPress) sites exploited and hosting IFRAMES pointing to bad places. We'll get to the downloaded in a second, but the interesting thing to note is that it doesn't seem to be a scanner exploiting one vulnerability but some tool that's basically firing a bunch of Joomla and Wordpress exploits at a given server and hoping something hits. We'd like PCAPs or weblogs if you're seeing something similar in your environment. Right now it seems the biggest pain is around Joomla users, particularly with extensions which greatly increase the vulnerability footprint and the one thing helping WordPress is the really nice feature of 1-button upgrades (and upgrades which don't tend to break your website).
The IFRAMES seem to have rapidly changing FQDN's that it is using but the common element is /nightend.cgi?8. Two of the bad IPs that seem to be frequent offenders are 78.157.192.72 and 108.174.52.38. Ultimately it pulls FakeAV software to do it's badness.
Mediation is your typical advice, make sure all your software is up-to-date and kept that way on a regular basis.
If you have weblogs (particularly verbose ones), I would be interested in seeing them. The tool being used is of interest to me.
--
John Bambenek
bambenek \at\ gmail /dot/ com
Bambenek Consulting
9 Comments
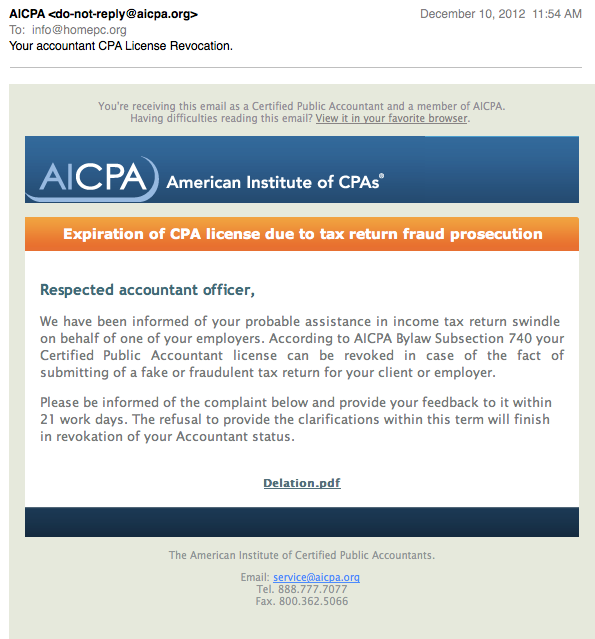
Your CPA License has not been revoked
I have been seeing some e-mails hitting my spam traps today, warning me of my revoked CPA license. No, I am not a CPA. But the e-mails are reasonably well done, so I do think some CPAs may fall for them. At least they got the graphics nice and pretty, but the text could be better worded.
The only clickable link is the "Delation.pdf" (maye that should be deletion?). Upon clicking the link, we are send on the usual malware redirect loop:
The first stop is
httx://tesorogroup. com/components/com_ag_google_analytics2/taxfraudalert.html
It includes javascript and meta tag redirects to
httx://eaglepointecondo. co/ detects /denouncement-reports.php
which will test our browser for vulnerable plugins and try to run a java applet. Looks all very "standard". You may want to check your DNS server logs for anybody resolving tesorogroup.com or eaglepointecondo.co . The two host currently resolve to 64.15.152.49 and 59.57.247.185 respectively.
Wepawet does a nice job analysing the obfuscated javascript:
http://wepawet.iseclab.org/view.php?hash=c390cd570069882395e24b7a30abbe64&t=1355160668&type=js
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
6 Comments
ISC Feature of the Week: Glossary Additions
Overview
A little while ago we announced the Infosec Glossary at https://isc.sans.edu/diary/ISC+Feature+of+the+Week+Glossary/14188. In this feature, we update the layout and add Suggest Edit and Suggest Addition features! The new layout has a much more compact look so you don't have to scroll the page so much.
Features
Overview - https://isc.sans.edu/glossary.html#overview
- Mostly unchanged except for the link to Suggest an Addition described below.
List of Terms - https://isc.sans.edu/glossary.html#terms
- This is a much more responsive, compact list and still has the search box to limit list to matching terms.
- Mouse over a term in the list to view definition and options.
- "suggest edit" option displays definition box for you to change then optionally enter a name and click the check button to submit.
Suggest an Addition - https://isc.sans.edu/glossary.html#add
- Enter a Term not in the list above
- Enter a definition for the term
- Optionally enter your name
- Click the check button to submit
Post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center https://isc.sans.edu
0 Comments
Reports of Strange TCP Port 443 Behavior
A reader posted that they are observing strange TCP 443 behavior that looks like a fast flux [1] style pattern. They have a large snort sensor install base. Is anyone else seeing behavior like this? If so.... Got packets?
If you are seeing this behavior and are allowed pleaes report it!
[1] http://www.honeynet.org/papers/ff/
Richard Porter
--- ISC Handler on Duty
0 Comments
Rich Quick Make Money!
Based on reader reports (thanks Fred!) it looks like some carefully crafted spam is making its way past filters at the moment. The spams have content like
To all of my friends who didn't have the a moment to watch me on the channel-20 news last Tuesday talking about my blog, and financial accomplishments. I'm forwarding you the News Article, so you can read the whole story on how I became financially independent and wealthy. hxxp://r,turn,com/r/formclick/id/Ln5c6GsFyTbGgAsAbQABAA/url/%68%74%74%70%3a%2f\%6a%2e%6d%70/TSQHMO?djyna
I'm using hxxp and , instead of . to keep the domains from becoming clickable .. and to hopefully keep your spam/virus filter from panicking belatedly over this ISC diary instead of over the real spam earlier :)
We first expected some sort of Fake AV malware campaign, but it looks like the site "only" pushes the latest work-at-home-get-rich-quick scam. At least for the moment. Looking at the URL closely, here's what's going down: r,turn,com has an open redirect. The bad guys use this as a trampoline to bounce whoever clicks on the link to the next stage.
"%68%74%74%70%3a%2f\%6a%2e%6d%70" is really only hexadecimally encoded ASCII, and translates to "hxxp:/\j,mp", so the next stage is hxxp://j,mp/TSQHMO?djyna.
There, we get a redirect to hxxp://wallyplanet,info/fizo.htm?33722, where we get a file that contains window.location = "hxxp://bit,ly/Vn3lWj". Which redirects to hxxp://picklecook,us/fizo2.htm, where we get a file that contains window.location = "hxxp://CNBC-20NEWS,NET/momstory294b.htm", where we finally get the sob story and the get-rich-quick scam.
I doubt the spam filters follow this mess all the way, hence the URL reputation score in the spam filters apparently got tricked, and let the email through.
2 Comments
Comodo DNS hiccup on usertrust.com
We received a report from a reader (thanks Marco!) that earlier today, "usertrust.com", a domain used by Comodo CA, apparently was pointing elsewhere for a while. From information captured by passive DNS sensors, it indeed looks like the NS records were changed to "ns1.pendingrenewaldeletion.com" and the A records were changed to point to 208.91.197.132, both indicative of a domain that has been "parked" by Network Solutions. Two hours later, the DNS records were updated again, and pointed back to Comodo. Given that the registration record on Network Solutions' WHOIS shows a renewal date of December 5 for the usertrust.com domain, it is probably fair to assume that "something" went wrong in the renewal.
2 Comments
Fake tech support calls - revisited
Back when this scam started to become "popular", the caller usually claimed to be from Microsoft or any other large well known techie company, and tried to talk the person answering into running some commands or programs on the PC "in order to fix a critical problem". But the latest twist of this scam seems to get more targeted: We have had two reports of fake tech support calls where the caller claimed to be representing the firm to which the called company had in fact outsourced its IT Support.
This isn't really rocket science on the attackers' part - some basic internet searches will give them lots of press releases and marketing blah where service providers tout their success in winning over a big support contract for company XYZ. I tried a search on my own based on one of the samples, and even found job postings where the service provider was explicitly looking for techies to work on the XYZ account. Next, I went on a LinkedIn search to find techies working for the service provider, and filtered to discover if any were connected to anyone at company XYZ. Not surprisingly, there were quite a few. Stuff like this is a gold mine for phishers, social engineering, and fake tech support scammers.
There is little point though in trying to keep the Internet free from such information. Company XYZ might have been able to control what the marketing people of the service provider write about their "reference customer", but they can't really control who is connected to whom on social networks.
In terms of countermeasures, as a service provider, make sure you have an established way how your staff identifies itself to your customer. As a company with outsourced services, make sure there is a well defined conduit how the service provider interacts with your employees, that your employees are aware of this, and that there is a defined mechanism (known call back number, etc) in place to verify a call if your employees have any doubt.
Please report fake tech support calls on https://isc.sans.edu/reportfakecall.html
2 Comments
How to identify if you are behind a "Transparent Proxy"
Traveling a lot? You may still be one of the unlucky few who not only connects to hotel networks regulary, but doesn't have easy access to a VPN to bypass all the nastyness they introduce. In addition, even some "normal" ISPs do introduce a feature called "transparent proxy" to manage traffic. Transparent proxies are nice in that they are easy to setup up and invisible ("transparent") to the user. However, the browser isn't aware of them, and as a result the transparent proxy even if configured non-malicious can still cause confusion bout the same origin policy browser depend on to isolate web sites from each other.
A transperent proxy works in conjunction with a firewall. The firewall will route traffic to the proxy, but changing the desitination IP address of the packet to the proxy's IP address. The proxy now relies on the "Host" header to identify the target site. As a result, the relationship between IP address and host name that the client established is lost.
There is a pretty simple test to figure out if you are behind a simple transparent proxy: Telnet to a "random" IP address (e.g. 192.0.2.1) on port 80. Then, copy/past a simple HTTP request, that includes the host header (the part you type is shown in bold font:
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
6 Comments
Security Patch released for BIND 9.9.2
A security patch was released for BIND 9.9.2. The patch addresses 26 different bugs and/or security issues. Update your bind DNS server to version 9.9.2-P1.
Updates can be downloaded here: http://www.isc.org/downloads/all
More information is available here: https://kb.isc.org/article/AA-00829
0 Comments
Where do your backup tapes go to die?
The trade press is filled with stories about companies getting into big regulatory trouble over lost backup tapes [1][2]. The tricky part is that usually, one reason companies use backup tapes is the ability to archive backup tapes offsite for extended periods of time. Terabytes by Terabytes, rotating cheap SATA disks usually is cheaper and faster, but hard drives don't have the offline persistence of backup tapes.
But with offsite storage comes loss of physical control. You hire a reputable, but not too expensive, records company to pickup the tapes, and store them at what you hope to be a secure facility. So I was a bit surprised to find a drum full of backup tapes dumped into an alley close to my house. The drum was filled with LTO data tapes commonly used in backups. The tapes looked in good shape, but a bit wet due to being exposed to rain. I don't have a sacrificial reader to try them out (given that they are wet, I don't want to put them in a "good" reader that is still in use). There are no markings showing the owner of the tapes either on the drum or the tapes themselves, but a couple have pencil markings (like a letter and a number) indicating that they may be used.
At this point I can only speculate what the tapes contain. There are a number of hospitals in the immediate area (couple miles), and I have found medical supplies and lost/discarded patients before. But so far no records. The same pile of trash also includes a similar drum with an address label, and I have yet to be able to contact that company.

So do you audit whoever stores, and discards, your tapes? Would it make sense to identify the owner in case they are found? Or is this just increasing the risk? Do you encrypt backup tapes before sending them offsite?
[1] http://www.southcoasttoday.com/apps/pbcs.dll/article?AID=/20121110/NEWS/211100330
[2] http://www.darkreading.com/database-security/167901020/security/news/240142846/10-top-government-data-breaches-of-2012.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
13 Comments
Recent SSH vulnerabilities
Exploit code for two different implementations of SSH were made public yesterday. Tectia SSH (www.ssh.com) a commercial solution and freeSSH/freeFTP. I currently do not see any public announcements from the vendor, nor any CVEs for tracking.
More to come on this.
0 Comments
John McAfee Exposes His Location in Photo About His Being on Run
Generally speaking, if you're on the run from the authorities over a homicide, you're probably best laying low and not making too much noise. Sure, there is a case for trolling "the man", but it usually comes back to haunt you.
Take the case of John McAfee who is currently on the run. A journalist for a shady website involving narcotics is apparently spending some time with him while he's on the run. It put up a post with a picture with John and the Editor-in-chief of said publication. (You can find it without too much effort, but it's NSFW).
Well, if you download the picture and use any of the standard tools to get metadata (I use exiftool), it happily reports not only the make and model of the camera, but the GPS coordinates of where the picture was taken (today). We can say that, yes, John McAfee is apparently no longer in Belize. ;)
A humorous post to point out something many of us don't realize, our smartphones and devices are increasingly location-aware and that information makes it into the media that those devices create.
See earlier SANS ISC posts on EXIF/location information:
Twitpic, EXIF and GPS: I Know Where You Did it Last Summer
Snipping Leaks
--
John Bambenek
bambenek \at\ gmail /dot/ com
Bambenek Consulting
2 Comments
Mobile Malware: Request for Field Reports
At my last two speaking engagements, I asked a simple question: "'Have you, or anyone you know been infected with malware on you smartphone?" So far, no one has raised their hand.
I'd like to ask the same question here, since there's a much wider audience of people who have the skills/instinct to notice such an infection.
If you, or someone you know (no friend of a friend reports, please) have witnessed a mobile malware infection in the wild please leave a comment below or send in a report via our contact page.
9 Comments
Collecting Logs from Security Devices at Home
You have probably considered logging the data from your home security devices and often the most difficult question is, where do I start? I included a list of loggers that can be used to collect security data from home devices. One that I have always found interesting is the gateway ISP router because it collects various types of logs including firewall logs (i.e. iptables).
Some of these loggers require more work to setup (i.e. Linux rsyslog) while other are much simpler (i.e. Windows Syslog Server) and start collecting logs right away from your network. For example, the Syslog Server from Sourceforge is a free Windows syslog server that can setup in minutes and can easily collects the logs from a home based router. It has a few features where you can view the events by host, severity (as per picture) and facility and can send an email when a threshold value has been reached. Here is a screenshot of this software collecting Linksys router iptables logs.
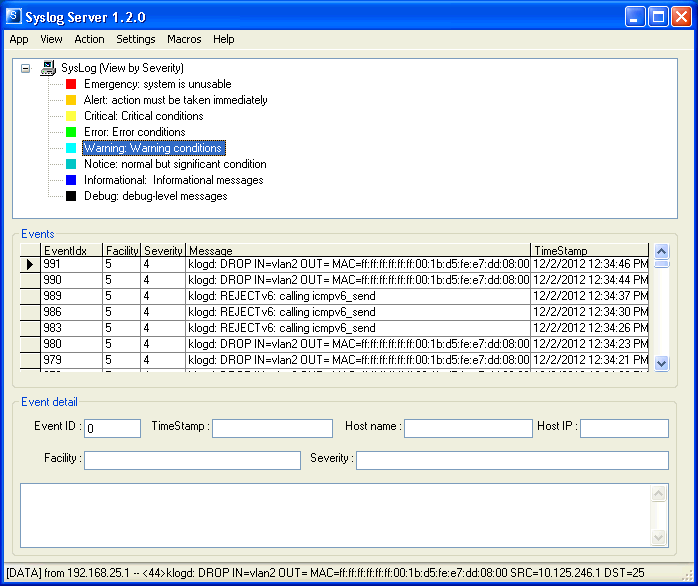
If you are using a logger that works well for you and would like to share your experience with other, either add it as a comment or send your description of your favorite logger via our contact form and I will update the list later.
Freeware
Rsyslogd and MySql (Linux only)
http://www.rsyslog.com/doc/rsyslog_mysql.html
Syslog Server (Windows only)
http://sourceforge.net/projects/syslog-server/
Free download but require registration
ArcSight Logger (Log up to 750 MB per day and 10:1 compression. Linux only)
http://www.hpenterprisesecurity.com/products/hp-arcsight-security-intelligence/hp-arcsight-logger/
Splunk (Log up to 500 MB per day. Support multiple OS)
http://www.splunk.com/download
What's Up Gold Syslog Server Free Tool
http://community.whatsupgold.com/freetools/syslog
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
7 Comments
Zero Day MySQL Buffer Overflow
A new stack-based buffer overflow vulnerability was released on Full Disclosure yesterday for MySQL. Depending of the user privileges, the flaw can cause MySQL to enumerate users, crash or possibly execute arbitrary code with the privileges of the user running MySQL.
The following CVEs have been assigned to track this MySQL vulnerability:
CVE-2012-5611 MySQL (Linux) Stack based buffer overrun PoC Zeroday
CVE-2012-5612 MySQL (Linux) Heap Based Overrun PoC Zeroday
CVE-2012-5613 MySQL (Linux) Database Privilege Elevation Zeroday Exploit
CVE-2012-5614 MySQL Denial of Service Zeroday PoC
CVE-2012-5615 MySQL Remote Preauth User Enumeration Zeroday
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
2 Comments





1 Comments