pseudoDarkleech Rig EK
Introduction
Since Monday 2016-10-03, the pseudoDarkleech campaign has been using Rig exploit kit (EK) to distribute Cerber ransomware. Prior to that, this campaign had been distributing CypMIC ransomware.
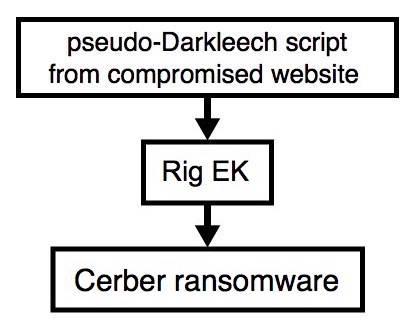
Shown above: An infection chain of events.
Let's take a look at an infection from the pseudoDarkleech campaign that I intercepted earlier today (Friday 2016-10-14).
Traffic
Below are screenshots of the traffic filtered in Wireshark.
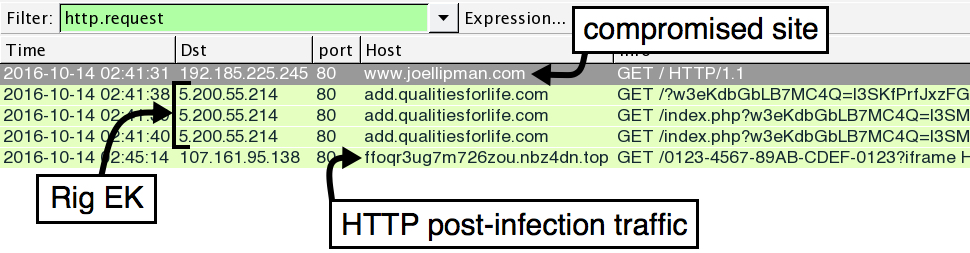
Shown above: HTTP traffic seen during this infection.
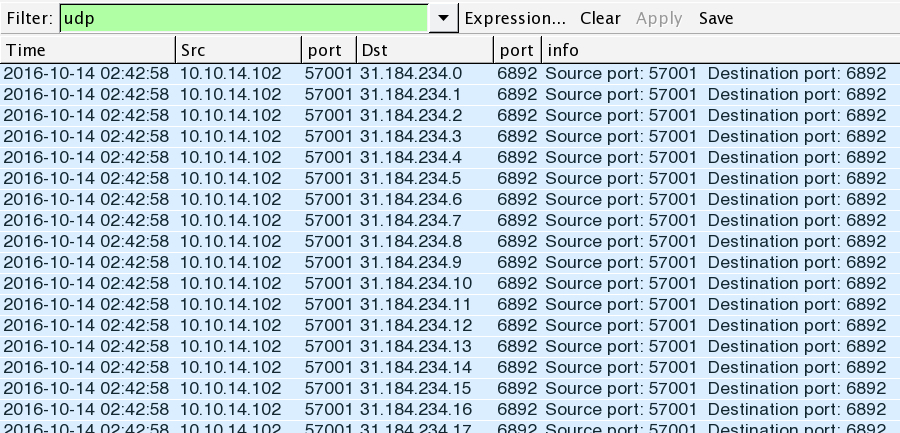
Shown above: UDP traffic seen during this infection.
Traffic caused by this infection chain of events:
- 5.200.55.214 port 80 - add.qualitiesforlife.com - Rig EK
- 31.184.234.0 through 31.184.235.255 (31.184.234.0/23) port 6892 - UDP traffic caused by Cerber
- 107.161.95.138 port 80 - ffoqr3ug7m726zou.nbz4dn.top - HTTP traffic caused by Cerber ransomware
Other domains from the Cerber ransomware decryption instructions:
- ffoqr3ug7m726zou.19jmfr.top
- ffoqr3ug7m726zou.5y6w0n.top
- ffoqr3ug7m726zou.onion.to
A variant of Rig Exploit Kit
Since 2016-09-26, I've noticed a new variant of Rig EK. I believe it's one that security researcher Kafeine has designated RIG-v (link). Kafeine describes RIG-v as a "VIP version" of Rig EK. RIG-v uses a slightly different obfuscation for its landing page. It also displays some Neutrino-style traits and uses RC4 encryption. Luis Rocha has a good write-up on this version of Rig EK in two parts (part 1, part 2).
The Flash exploits used by RIG-v are similar to what I saw from Neutrino EK before it nearly disappeared last month (something also discussed by Kafeine). I still see a trickle of detections for Neutrino EK, but that's dwarfed by the amount of Rig EK (both regular Rig EK and the newer RIG-v) I find on a daily basis.
RIG-v is currently used by the pseudoDarkleech campaign to distribute Cerber ransomware. It's also being used by the Afraidgate campaign to distribute Locky ransomware. The other EK-based campaign I regularly track is the EITest campaign, and it currently uses what I now call "regular Rig EK."
Below are some images of this infection traffic:
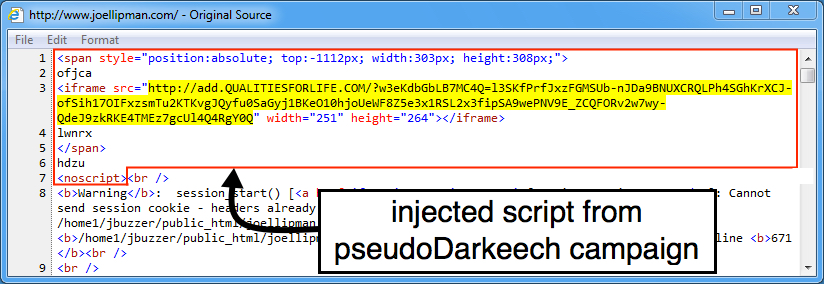
Shown above: Injected script in a page from the compromised site pointing to a Rig EK landing page.
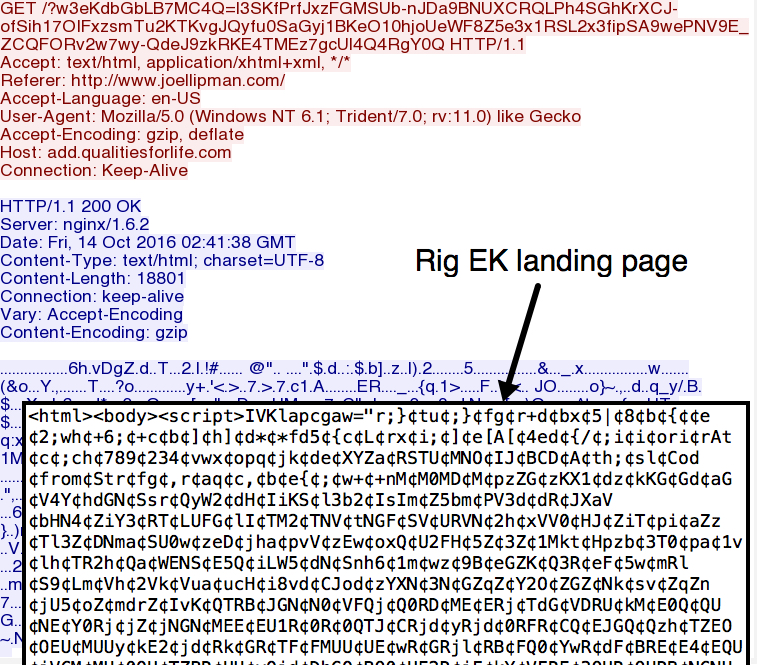
Shown above: The Rig EK (RIG-v) landing page.
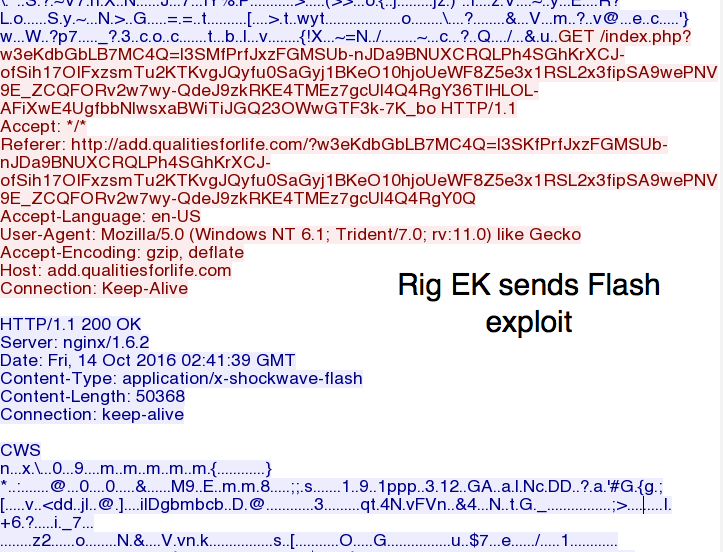
Shown above: RIG-v sends the Flash exploit.
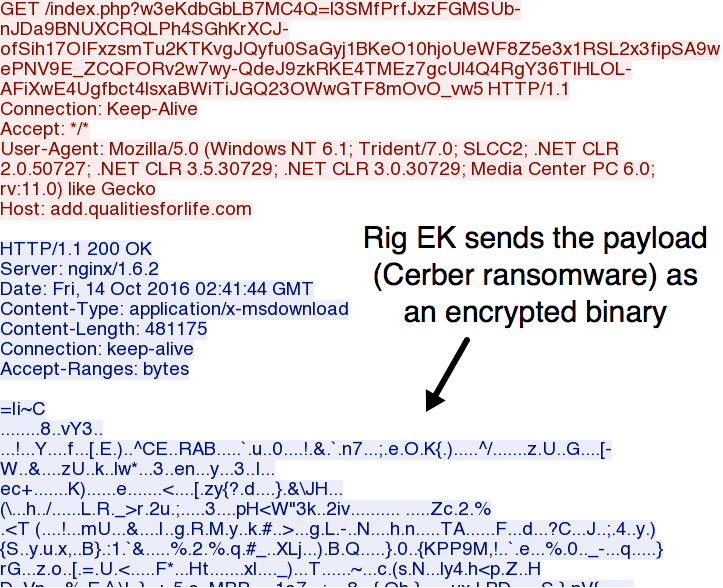
Shown above: RIG-v sends the payload (Cerber ransomware) as an encrypted binary.
Malware and artifacts
Flash exploit sent by RIG-v:
- File size: 50,368 bytes
- SHA256 hash: b95fa5beddf64653bf88456ed521a0b7226d4fb4f5e8983b85ca5d03d8621be5
- Location: C:\Users\[username]\AppData\Local\Microsoft\Windows\Temporary Internet Files\index[1].swf
Malware payload (Cerber ransomware):
- File size: 481,175 bytes
- SHA256 hash: a31a437f86ee5b5325b77d1956c19b3c144a8d1059b47a642992684ee68bbda0
- Location: C:\Users\[username]\AppData\Local\Temp\rad13FE2.tmp.exe
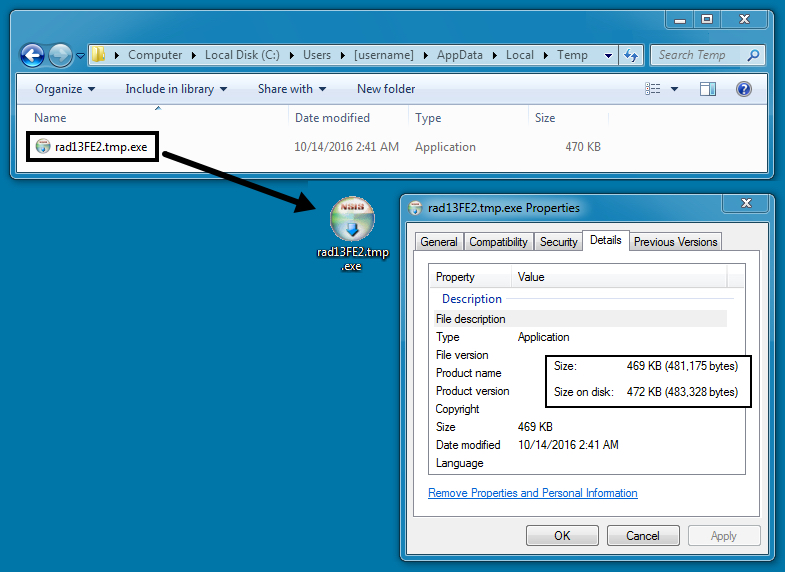
Shown above: The RIG-v payload as a decrypted binary (Cerber ransomware) on the infected host.
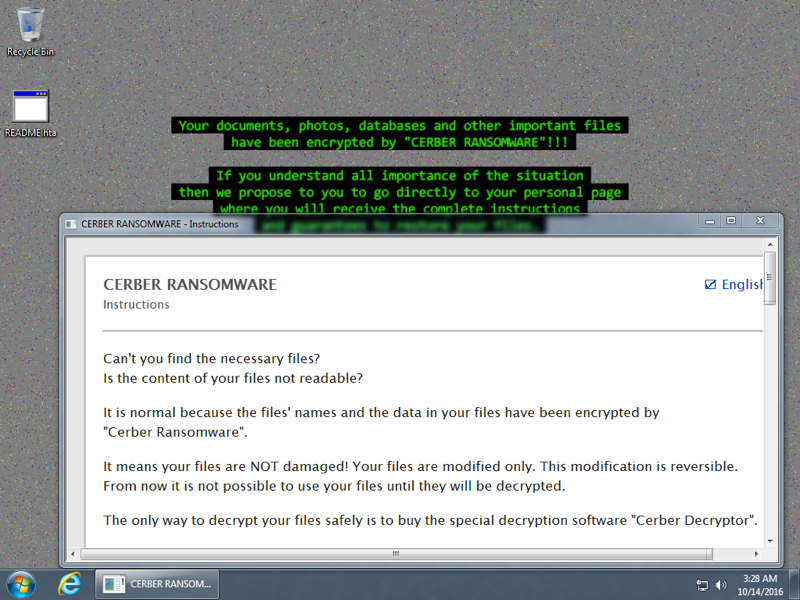
Shown above: Desktop of the infected Windows host after rebooting.
Getting to the ransom payment page
This Cerber ransomware is a newer version I hadn't noticed until recently. Previous versions of Cerber left more artifacts on the desktop with the decryption instructions (a text file, an html file, a VBS file to generate spoken instructions, and a shortcut). This most recent version of Cerber leaves only one file on the desktop, an .HTA file. HTA is a file extension for HTML Application files.

Shown above: The web page that appeared when I clicked on one of the links from the HTA file.
Using the window generated by the HTA file, you can get to the decryption instructions. However, this requires getting past a different type of CAPTCHA than before. This newer Cerber variant uses an image-based CAPTCHA that requires multiple clicks to get through. Turns out this new variant of Cerber with the updated CAPTCHA debuted back in August 2016 as noted by BleepingComputer.
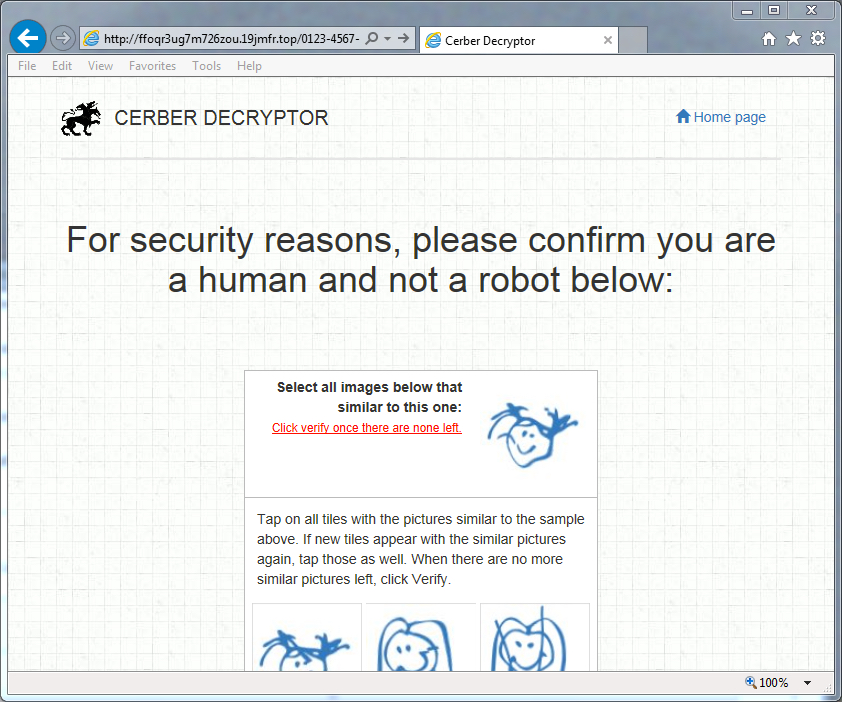
Shown above: An example of the CAPTCHA page you need to do before you can go any further.

Shown above: CAPTCHA images before you can pass.

Shown above: CAPTCHA images that will let you pass.
Notice the verify button is no longer shaded out.
This particular Cerber infection showed a ransom payment of 0.7238 bitcoin (460 US dollars) for the first 5 days, after which it will double to 1.4476 bitcoin (921 US dollars).
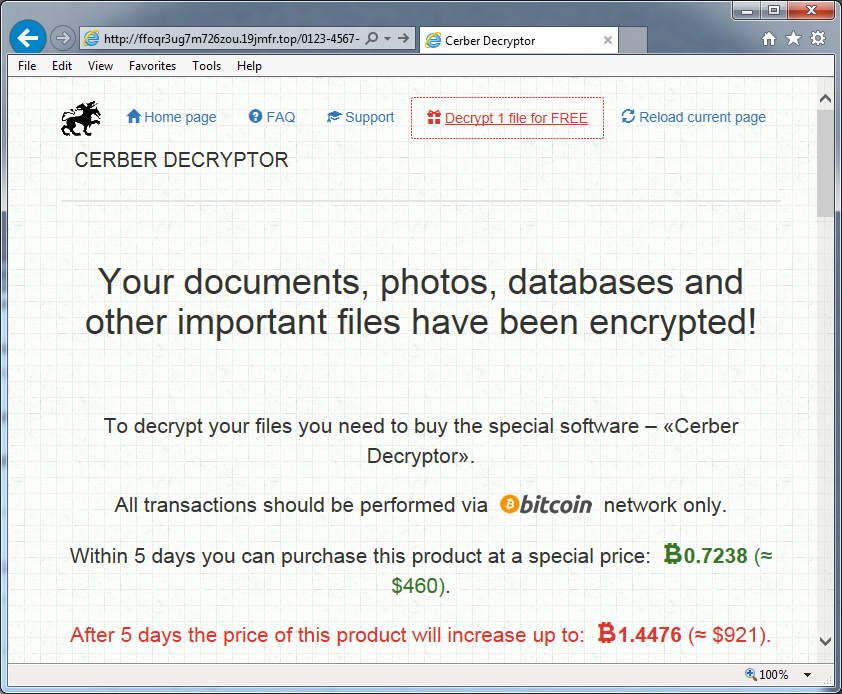
Shown above: The price to decrypt your files.
Final words
Like other ransomware, Cerber continues to be an evolving threat. I usually see Cerber distributed through EK traffic, but malicious spam (malspam) is another popular method for mass distribution of ransomware. However, these aren't the only vectors. Social media is another vector that's increasingly popular for more targeted attacks. One reader shared a story of being targeted with ransomware through a person contacting her on Skype (see comments from SaraTheEnthusiast at the end of this diary).
For EK traffic, properly-administered Windows hosts are not likely to be infected. As long as your Windows host is up-to-date and fully patched, your risk is minimal for ransomware delivered through an EK. If you're running Windows 10, you have little to worry about.
But enough people are running outdated versions of Windows that are un-patched or poorly-administered, so EK campaigns will continue. The pseudoDarkleech campaign has been using EKs to push ransomware, quite literally, for years now. And like other EK-based campaigns, it shows no signs of stopping.
Pcap and malware for this diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments