LogMeIn Captain! A "Not so Phishy" Phishing Campaign
Today's story is on another (sort of) phishing campaign - the twist on this one is that the targets are .. us, again, sort of. This one caught my eye because I've never had a logmein account - no reflection on the product, I've just always had licenses on other comparable products.
The email discusses a real situation, where a breach at one site can result in those credentials being used on a different site, because of the wide practice of folks using "the same password for everything".
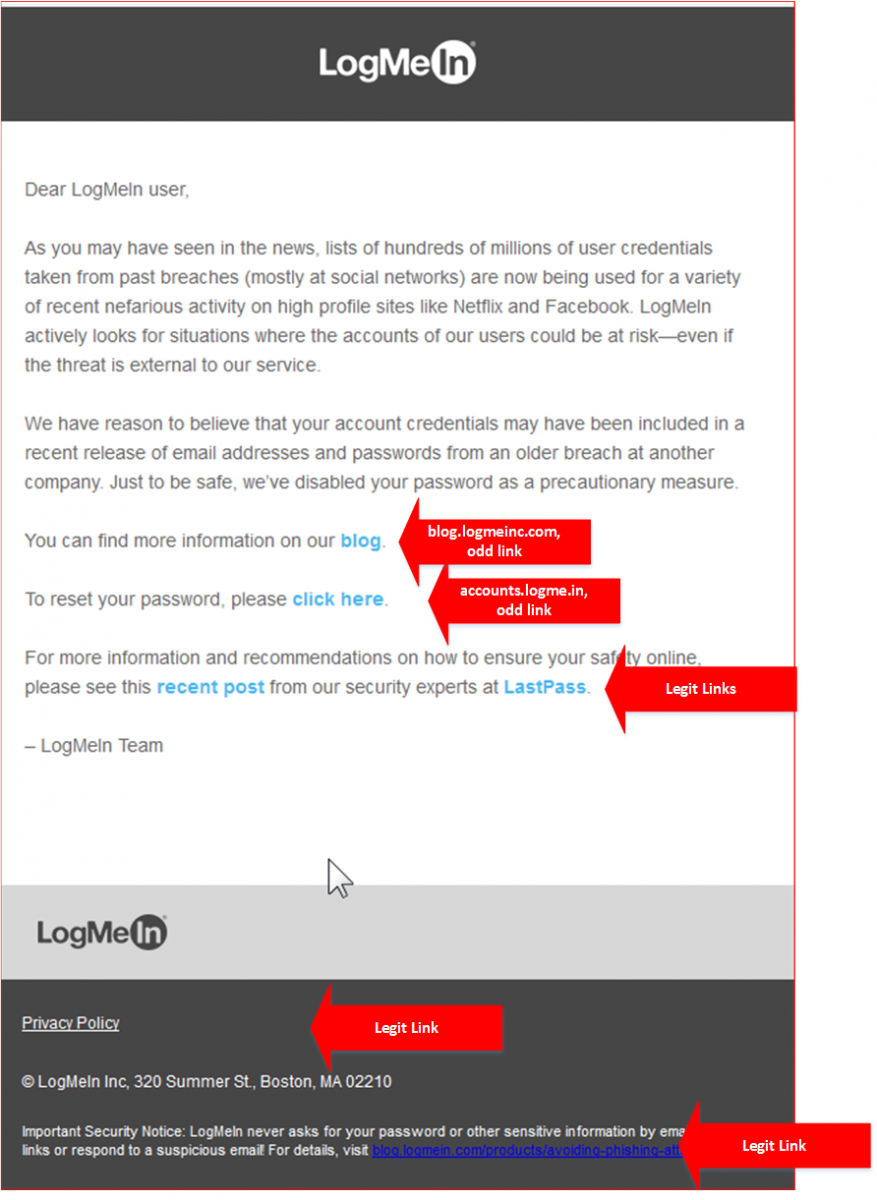
The note then continues on with two "click here" links, which point to the two different websites, neither of which is "logmein.com".
The blog entry in the email points blog.logmeininc.com is different than the blog on logmein's home page, which is at blog.logmein.com. And accounts.logme.in is a domain that truly looks like it was set up to steal credentials.
The use of "lookalike sites" like this, where the dns name is "close but no cigar" and the content is scraped from the real site is a very widespread and successful approach - if a person is faked into clicking the first link, they almost always continue on by giving up their password or installing the malware that's hosted on the site. This password change form looks precisely like that.
The truly ironic links in this note is that the one to the Privacy Policy and the "here's a logmein blog that explains why you should never click on links in random emails" - both of these point to logmein.com links that look "for real"
The final verdict? This note is absolutely legitimate, they really are asking folks to reset their passwords. Unfortunately, the way the note is constructed it should be setting off alarm bells for anyone in the security business.
This really is too bad, because the message is a good one - as Worf (STNG reference) is fond of saying, "it's always a good day to change your password"!
===============
Rob VandenBrink
Compugen


Comments
They have about 12 different blogs, so even going to logmein.com manually and looking at the blog linked there does not get you any info related to the stated issue (that's on a sub-blog of LogMeIn Pro / logmeininc.com)
(I didn't even know I had a LogMeIn account, until some wiki'ing reminded me that I used Hamachi for pseudo-LAN-parties about a decade or two ago, and they have been bought by LogMeIn Inc)
Anonymous
Jun 21st 2016
9 years ago
https://community.gotomypc.com/gotomypc/topics/gotomypc-password-issue
One of our users got an email from Citrix about this situation that could, at first glance, be misconstrued as phishing.
Anonymous
Jun 21st 2016
9 years ago