Let's Encrypt!
As I have stated in the past, I am not a fan of all of the incomprehensible warning messages that average users are inundated with, and almost universally fail to understand, and the click-thru culture these dialogs are propagating.
Unfortunately this is not just confined to websites on the Internet. With the increased use of HTTPS for web based management, this issue is increasingly appearing on corporate networks. Even security appliances from established security companies have this issue.
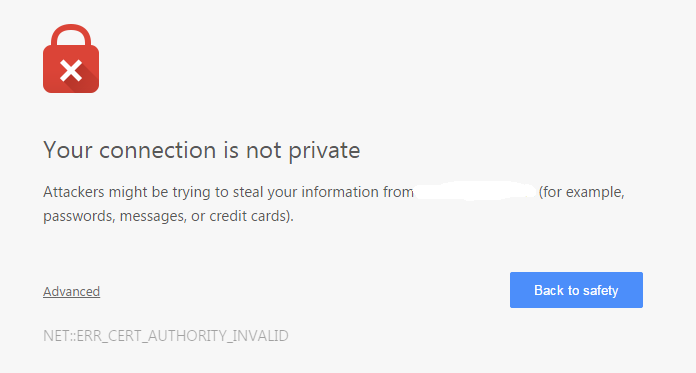
The issue in most cases is caused by what is called a self-signed certificate. Essentially a certificate not backed up by a recognized certificate authority. The fact is that recognized certificates are not cheap. For vendors to supply valid certificates for every device they sell would add significant cost to the product and would require the vendor to manage those certificates on all of their machines.
The Internet Security Research Group (ISRG) a public benefit corporation sponsored by the Electronic Frontier Foundation (EFF), Mozilla and other heavy hitters aims to help reduce this problem and cleanup the invalid certificate warning dialogs.
Their project, Let’s Encrypt, aims to provide certificates for free, and automate the deployment and expiry of certificates.
Essentially, a piece of software is installed on the server which will talk to the Let’s Encrypt certificate authority. From Let’s Encypt’s website:
“The Let’s Encrypt management software will:
- Automatically prove to the Let’s Encrypt CA that you control the website
- Obtain a browser-trusted certificate and set it up on your web server
- Keep track of when your certificate is going to expire, and automatically renew it
- Help you revoke the certificate if that ever becomes necessary.”
While there is still some complexity involved it should make it a lot easier, and cheaper, for vendors to deploy legitimate certificates into their products. I am interested to see how they will stop bad guys from using their certificates for Phishing sites, and what the process will be to report fraudulent use, but I am sure all of that will come.
Currently, it sounds like the Let’s Encrypt certificate authority will start issuing certificates in mid-2015.
-- Rick Wanner MSISE - rwanner at isc dot sans dot edu - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)


Comments
Anonymous
Feb 28th 2015
1 decade ago
Anonymous
Mar 1st 2015
1 decade ago
Seems that IdenTrust will be issuing the certs, they are listed as one of the partners and the SSL cert on https://letsencrypt.org/ is from them.
And since IdenTrust CA is recognised...
Anonymous
Mar 2nd 2015
1 decade ago
No such thing as a free lunch IMO. But I'm a little swayed by the fact it's supported by the EFF.
What do guys think?
Anonymous
Mar 2nd 2015
1 decade ago
Let's Encrypt is backed by Mozilla, so recognition from one of the big three browsers is pretty much a non-issue. Backing by Akami and Cisco gives them some pretty good leverage for getting accepted by the other two.
Anonymous
Mar 3rd 2015
1 decade ago
Even though Let’s Encrypt has no apparent business model, let’s suppose for a minute that it gets some market share. Over time, vendors might trust its longevity enough to build support into their routers, webcams, and other devices. When their end-user customers set up the device, it would automatically certificate-fetch from Let’s Encrypt. That’s the only world in which self-signed certificates might become a thing of the past.
Anonymous
Mar 7th 2015
1 decade ago