Investigating Security Incidents with Passive DNS
Sometimes when you need to investigate a security incident or to check for suspicious activity, you become frustrated because the online resource that you’re trying to reach has already been cleaned. We cannot blame system administrators and webmasters who are just doing their job. If some servers or websites remains compromised for weeks, others are very quickly restored/patched/cleaned to get rid of the malicious content. It’s the same for domain names. Domains registered only for malicious purposes can be suspended to prevent further attacks. If the domain is not suspended, the offending DNS record is simply removed.
During the weekend, Brett, one of our readers, reported a malicious website that tried to push a malicious Javascript to the victim’s browsers. There is nothing really new behind this attack. You visit a regular website and you get a new tab/windows with malicious content. But I’m always having a look at the page just to be sure that new techniques are not used or to find something more interesting on the compromized server. When Brett reported the malicious page to the ISC, he just sent a screenshot that revealed only a part of the URL:
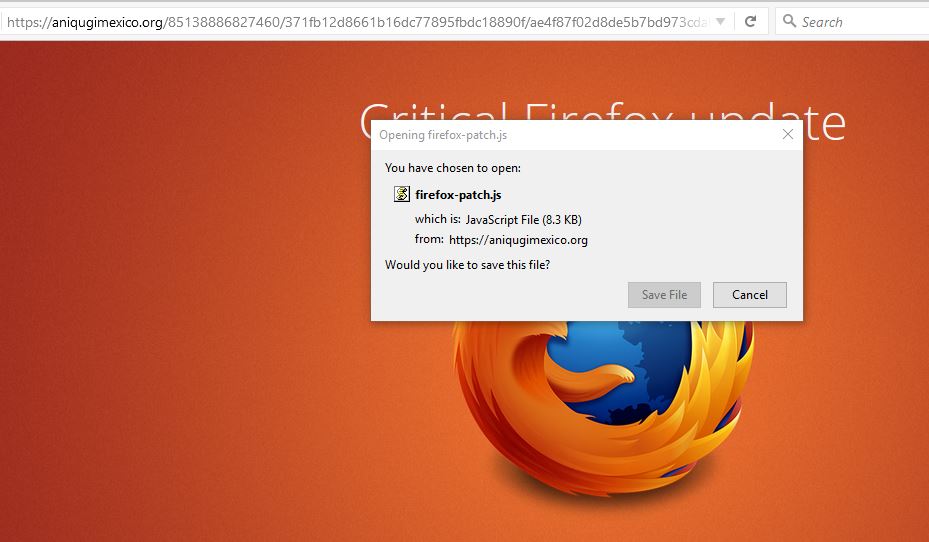
That’s not easy to start an investigation so I asked him more details. He replied with the complete details how he landed on this page but, in the meantime, the offending content was removed and the DNS record removed:
$ host www.aniqugimexico.org Host www.aniqugimexico.org not found: 3(NXDOMAIN)
When you’re investigating, the good reflex is to collect all the data and log them! (See my previous diary about full packet capture[1]). You can find back the IP address of the offending website:
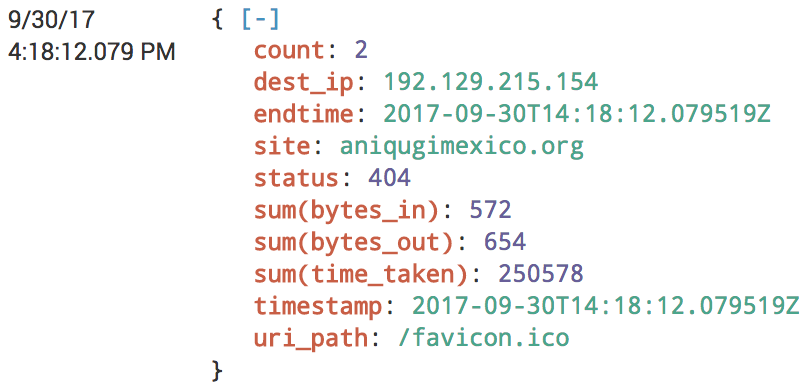
Just change your local /etc/hosts file in your analysis environment and you're good to go! If you're lucky, the website is still delivering the malicious content. Another very good source of information is to use Passive DNS services like virustotal.com[2], dnsdumpster.com[3] or passive total.com. If the traffic generated by the victim was captured, you can try to extract the suspicious code from the PCAP files or from any proxy solution.
They are plenty of passive DNS services and checking all of them can be time-consuming and boring. Hopefully, we can automate the lookups using a Ruby gem available on GitHub: passivedns-client[4]. You can also build your own passive DNS database with the tool passivedns[5] which will collect DNS traffic from an interface (live sniffing) or by reading PCAP files. Other NSM solutions like Bro[6] also collect all the DNS traffic.
[1] https://isc.sans.edu/forums/diary/The+easy+way+to+analyze+huge+amounts+of+PCAP+data/22876/
[2] https://www.virustotal.com/#/domain/aniqugimexico.org
[3] https://dnsdumpster.com/
[4] https://github.com/chrislee35/passivedns-client
[5] https://github.com/gamelinux/passivedns
[6] https://www.bro.org/
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments