Basic Office maldoc analysis
Malicious Office documents come in all type of flavors, sometimes very simple: they contain just an embedded file (for example an EXE), without any script or exploit to automatically launch the embedded file. The user is persuaded through social engineering to extract and execute the embedded file.
Analyzing such files in a sandbox will often not reveal the malicious payload, as the sandbox engine needs to recognize and open the embedded file.
Static analysis is simple however. Let's take a docx file as example. With zipdump.py, we can see the content:
.png)
The name of file 6 is oleObject1.bin: this is an OLE file.This can be analyzed with oledump.py:
.png)
Stream A2 has an O indicator: this means that the stream contains an embedded object (OLE2). We can select the stream and query info:
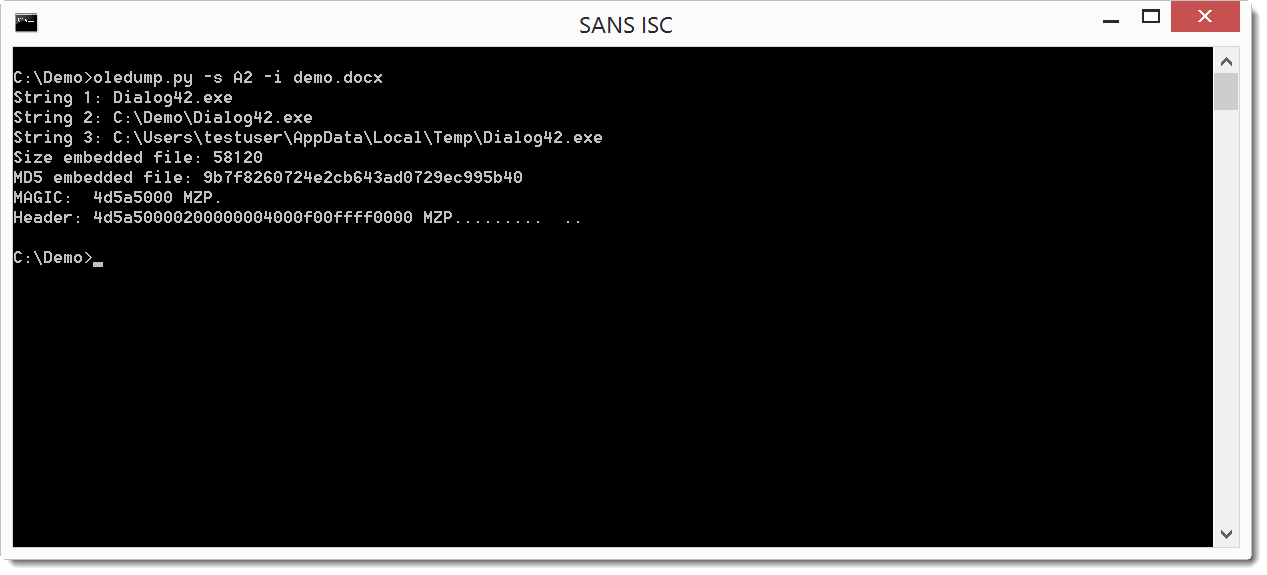
From the filename (Dialog42.exe) and the header (MZ / 4D5A), we can assume the embedded file is an executable.
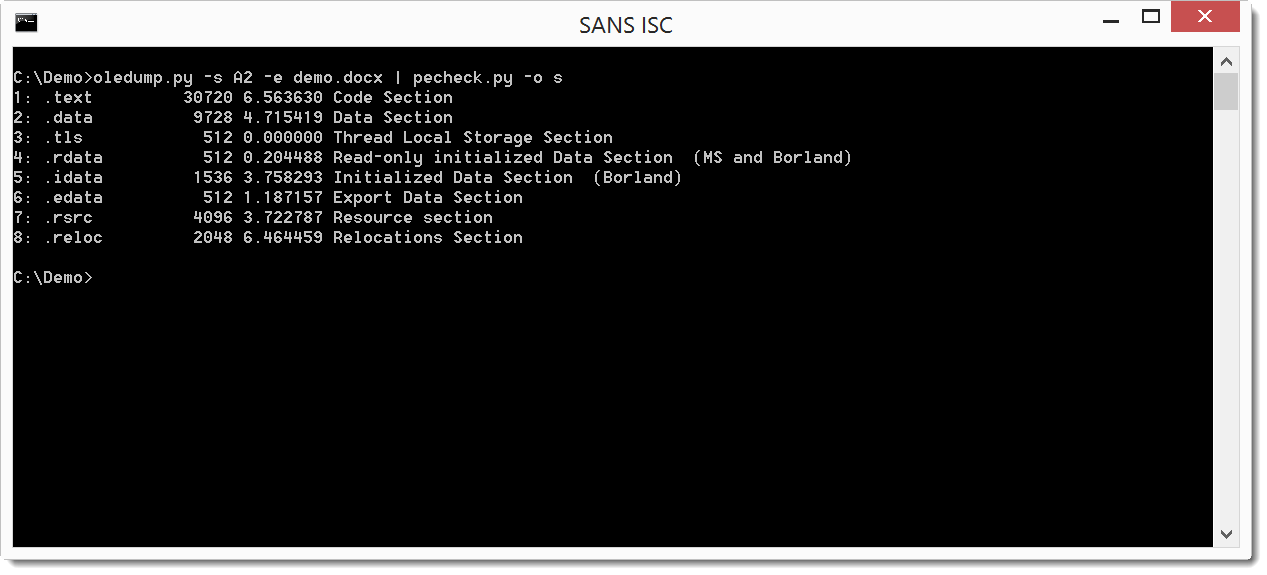
This is confirmed by piping the file through pecheck.py:
If you want to practice this type of analysis, it's easy to create your own samples: with Word, use command: Insert / Object / Object / Create from file ...
Inserting object like this can result in other types of documents, which I will cover in an upcoming diary.
Didier Stevens
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments