Windows Defender's Sandbox
Microsoft's Windows Defender on Windows 10 supports sandboxing now.
The Windows Defender engine runs with high privileges, and contains a lot of code (for example to parse many different file formats, e.g. parsing untrusted input). A lot of code means many potential bugs. Exploitable bugs in a process running with high privileges is a high risk.
To mitigate this risk, Microsoft implemented a sandbox: parts of Windows defender can now run inside a process with restricted privileges. If a vulnerability in Windows Defender is exploited inside the sandbox, the exploit code is contained inside the sandbox and can not access the operating system's resources (unless, of course, a distinct sandbox escape vulnerability is discovered and used).
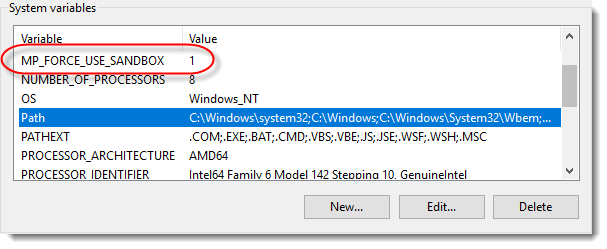
If you use Windows 10 1703 or later you can enable Windows Defender's sandbox by setting system environment variable MP_FORCE_USE_SANDBOX to 1 (and to 0 to disable it again).
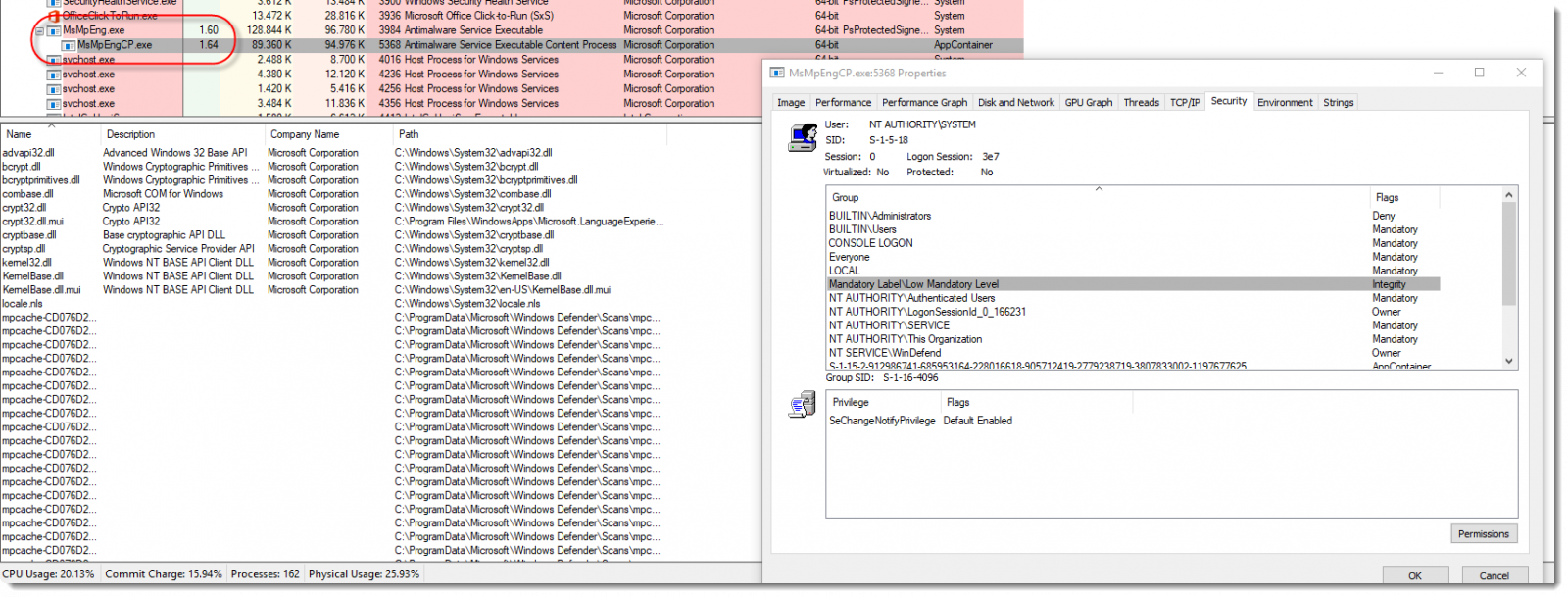
An OS restart is required to have Windows Defender take into account the setting. The activation of the sandbox can be asserted, with Process Explorer for example, by checking that process MsMpEng.exe has a child process named MsMpEngCP.exe (i.e. the sandbox).
I encountered an issue to activate the sandbox: after creating the system environment variable, I shutdown my machine and then powered it on. This did not enable the sandbox. I had to perform a restart (Start Menu / Power / Restart) for the sandbox to be activated. The same thing happened when I tried to deactivate the sandbox: make sure you perform a restart (literally). This issue was reported to Microsoft, and should be fixed in an upcoming release.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
Anonymous
Nov 1st 2018
7 years ago
Anonymous
Nov 1st 2018
7 years ago
It doesn't happen when I disable Fast Startup and then shutdown.
Anonymous
Nov 1st 2018
7 years ago
Anonymous
Nov 3rd 2018
7 years ago