7-Zip & MoW: "For Office files"
As I explained in my diary entry "7-Zip & MoW", the MoW on a ZIP file can be set to be propagated by 7-Zip to Office files only (propagation setting "For Office files").
My tests showed that this was based on the file extension of the Office file. As I received some questions about this, I took a look at the 7-Zip source code.
Here is the code that determines whether to write a Zone.Identifier ADS or not depending on the setting for Zone.Identifier propagation:
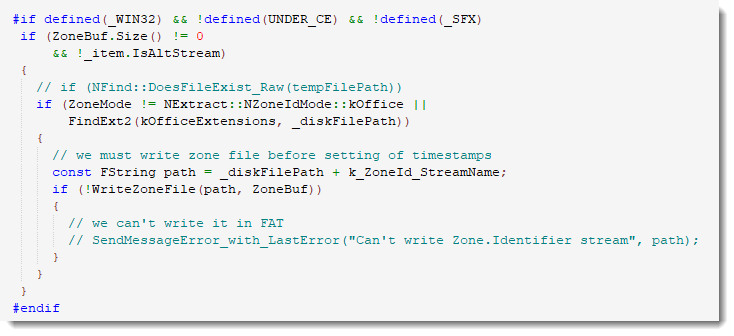
It uses function FindExt2 to check if the extension of the extracted file (_diskFilePath) matches a list of predefined extensions (kOfficeExtensions).
This is the predefined list kOfficeExtensions:
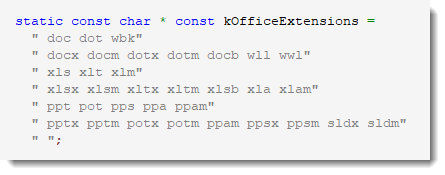
Notice that the extension RTF is not in this list.
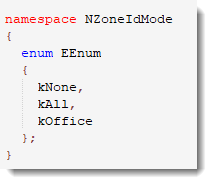
And while I was browsing the source code, I also took a look at the possible registry values for this setting:
7-Zip deletes registry values if they are not used (-1).
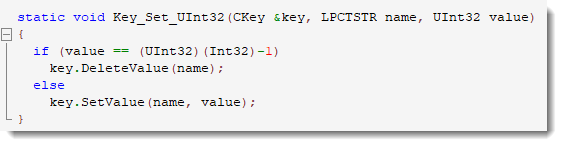
That is why you will find values 1 (all files) and 2 (Office files only) only in the registry.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments