MITRE ATT&CK v11 - a small update that can help (not just) with detection engineering
MITRE ATT&CK has long been the de facto standard for sharing TTPs of different threat actors and for planning and executing various threat emulation exercises. However, especially in the last few years, I’ve seen more and more Security Operations Centers start using it as well, for mapping of their defensive capabilities, detection use cases and SIEM correlation rules.
On Monday, a new version of the framework was released[1], which (among other changes) extends its content a little in order to make its use more straightforward when it comes to mapping of existing detections and for implementation of new ones. In versions 9[2] and 10[3], the framework was extended by an updated list of “Data Sources” relevant to the detection of each technique and sub-technique, and the current version adds an explicit description of how information available in specific Data Sources may be used in order to detect these (sub-)techniques.

Overview of detections for sub-technique Boot or Logon Initialization Scripts: Startup Items (T1037.005) in MITRE ATT&CKv10
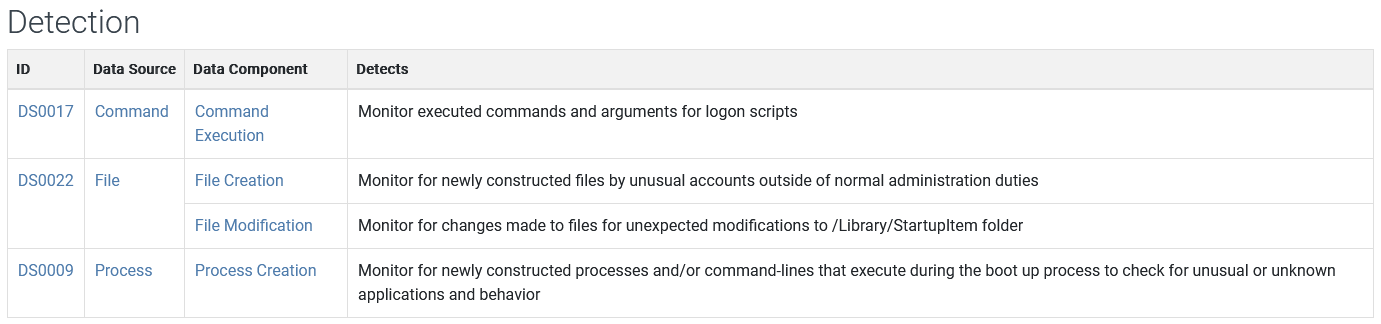
Overview of detections for sub-technique Boot or Logon Initialization Scripts: Startup Items (T1037.005) in MITRE ATT&CKv11
Although simple mapping of detection descriptions directly to specific Data Sources might not seem like much, it can certainly help when it comes to detection mapping and other defensive use cases, since the descriptions are now also available when one pivots to a view of a specific Data Source.
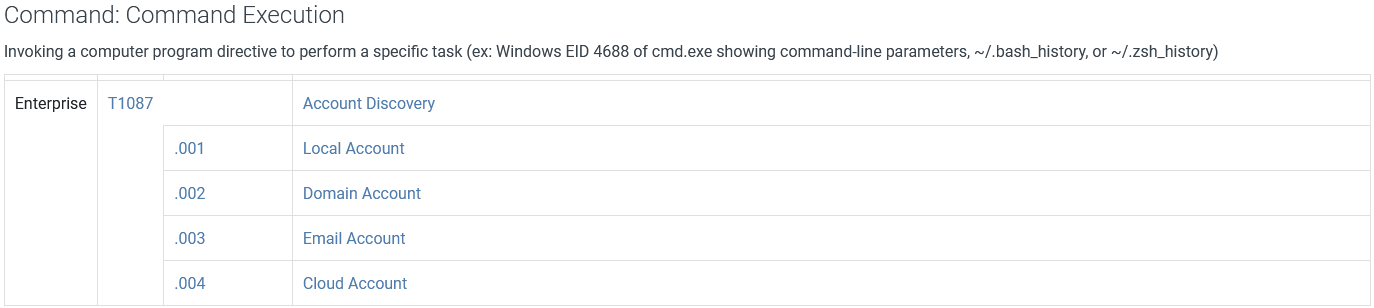
Overview of detections for technique Account Discovery (T1087) related to Command: Command Execution (DS0017) Data Source in MITRE ATT&CKv10

Overview of detections for technique Account Discovery (T1087) related to Command: Command Execution (DS0017) Data Source in MITRE ATT&CKv11
As you may see, the v11 update truly simplifies both mapping of existing detections to the ATT&CK framework, as well as certain aspects of detection engineering.
So, if your security operations/“blue” team doesn’t yet use MITRE ATT&CK in any way, perhaps now might be a good time to change that… After all, it won’t cost you anything and it can certainly help to achieve a formalized a view of (not just) what offensive techniques you can and can’t actually see with the detections you have in place.
[1] https://attack.mitre.org/resources/updates/updates-april-2022/index.html
[2] https://attack.mitre.org/resources/updates/updates-april-2021/index.html
[3] https://attack.mitre.org/resources/updates/updates-october-2021/index.html
-----------
Jan Kopriva
@jk0pr
Nettles Consulting


Comments