Shadow IT Makes People More Vulnerable to Phishing
Shadow IT is a real problem in many organizations. Behind this term, we speak about pieces of hardware or software that are installed by users without the approval of the IT department. In many cases, shadow IT is used because internal IT teams are not able to provide tools in time. Think about a user who needs to safely exchange files with partners and no tool is available. A change request will be created to deploy one but, with the lack of (time|money|resources), the project will take time. Unfortunately, the user needs the tool now, so an alternative path will be used like a cloud file sharing service.
I spotted an interesting phishing email that uses this shadow IT stuff. When you visit the page, you get a nice page that mimics an online drive:
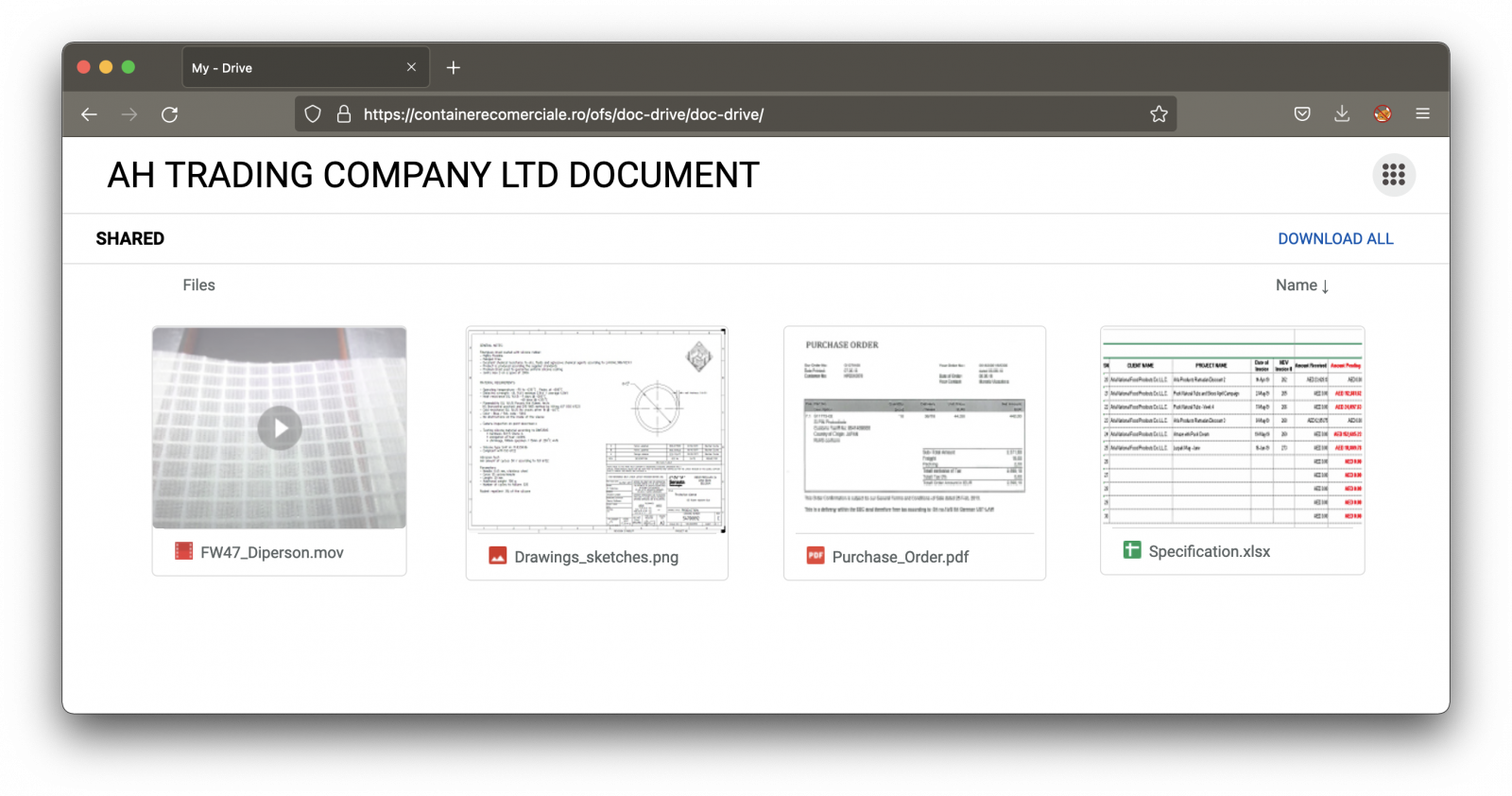
The page is nicely designed and looks legit, except that it's delivered through a suspicious domain name. All the links and document snapshots just redirect to a Javascript popup window that will try to collect the victim's credentials.
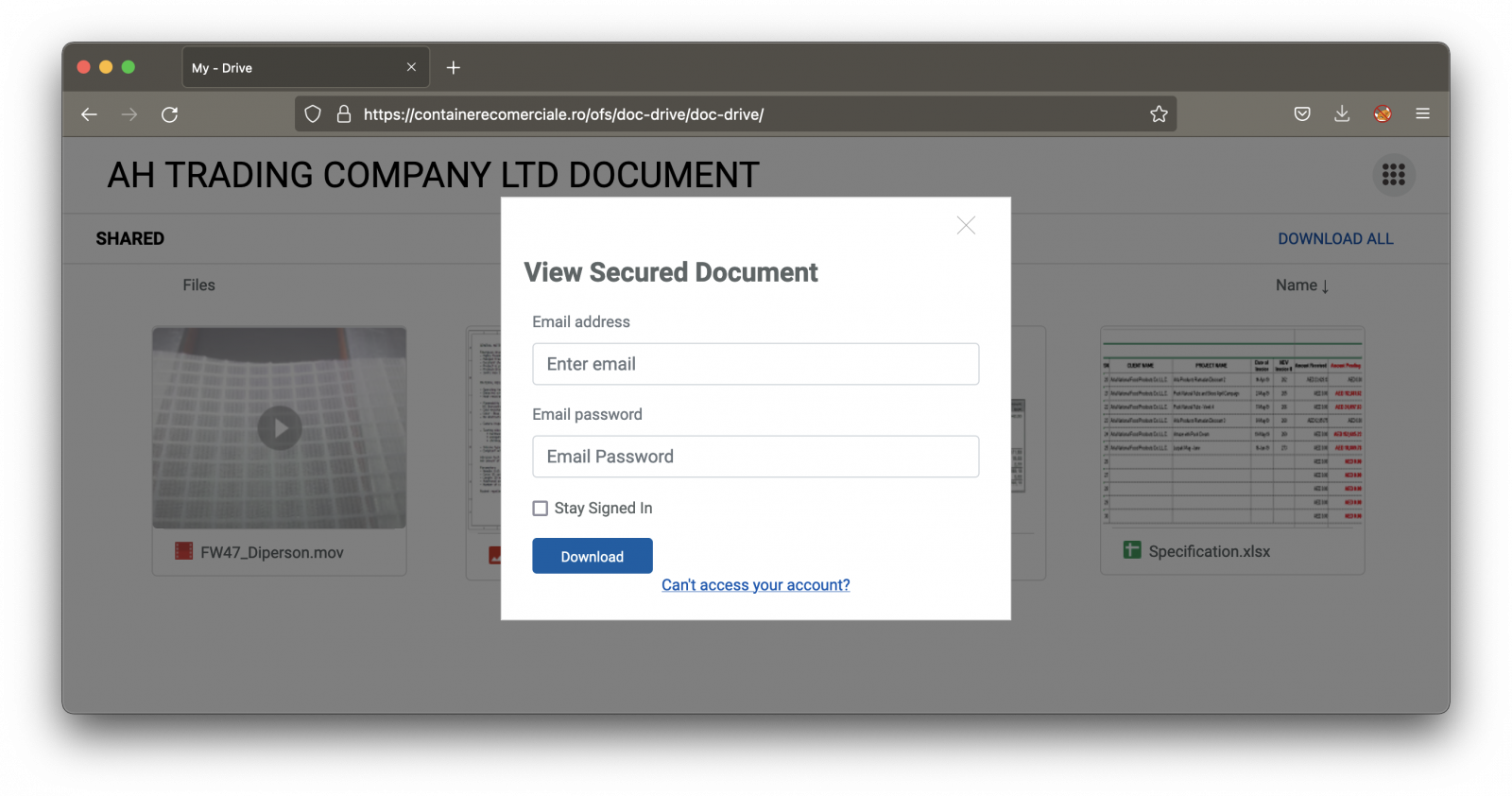
Note that the form verifies if the provided password is long enough :-)
<input type="password" name="pass" class="form-control" id=""
placeholder="Email Password" pattern=".{5,}"
required title="5 characters minimum"
oninvalid="this.setCustomValidity('Enter your correct email password')"
oninput="this.setCustomValidity('')"
>
If you use public cloud services to exchange files with your partners, you make them potentially more vulnerable to phishing attacks. Keep this in mind!
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments