Strange goings on with port 37
Similar to Yee Ching's diary on Thursday, I noticed an oddity in the Dshield data last weekend (which I had hoped to discuss in a diary on Wednesday, but life got in the way) and thought it was worth asking around to see if anyone knows what is going on. As soon as I saw it, I reconfigured my honeypots to try to capture the traffic, but wasn't able to. I'm always very interested when I see some of the legacy ports and protocols pop up. In this case, port 37 is the time protocol which operates on both TCP and UDP and is one of the many services that frequently ran on the low ports of Unix machines I administered back in the 1980s and 1990s. In recent years, most operating systems have disabled these services since they only seemed to be used for DDoS purposes. On Thursday, I took another look at the graph.
%20Attack%20Activity%20-%20Brave.png) By default, we normally only show the Targets/Day and Sources/Day, but I've added in the Reports/Day and TCP Ratio for this analysis. The first thing that I noticed was the huge spike in reports. Our baseline was in the 200-500 reports/day range, but on 26 May, this jumped to around 46,000. So someone, was very actively looking, the other oddity to me was, that prior to the spike, nearly all of the probes were TCP, but from 25 May - 2 Jun, nearly all the attack traffic was UDP (the gold line on the graph above, ranges from 0 = all UDP to 100 = all TCP), which then seemed to disappear and return to the mostly TCP probes on 3 Jun when I took this snapshot. Since I was unable to capture any of the packets, I don't know if there was some strange data there that might have shed some light on the purpose of this activity. The total number of sources was still pretty small ranging from a low of 69 on 25 May to 176 on 2 Jun. Meanwhile the number of targets ranged from 156 on 25 May to almost 700 on 27 May, which is right in the range of targets we've seen for the past 10 months (there was a flurry of activity on the port last June and July that spiked regularly around 2400-2500 targets, not shown in the graph above).
By default, we normally only show the Targets/Day and Sources/Day, but I've added in the Reports/Day and TCP Ratio for this analysis. The first thing that I noticed was the huge spike in reports. Our baseline was in the 200-500 reports/day range, but on 26 May, this jumped to around 46,000. So someone, was very actively looking, the other oddity to me was, that prior to the spike, nearly all of the probes were TCP, but from 25 May - 2 Jun, nearly all the attack traffic was UDP (the gold line on the graph above, ranges from 0 = all UDP to 100 = all TCP), which then seemed to disappear and return to the mostly TCP probes on 3 Jun when I took this snapshot. Since I was unable to capture any of the packets, I don't know if there was some strange data there that might have shed some light on the purpose of this activity. The total number of sources was still pretty small ranging from a low of 69 on 25 May to 176 on 2 Jun. Meanwhile the number of targets ranged from 156 on 25 May to almost 700 on 27 May, which is right in the range of targets we've seen for the past 10 months (there was a flurry of activity on the port last June and July that spiked regularly around 2400-2500 targets, not shown in the graph above).
So, I'm not sure what to make of it, especially without any packets. If any of you managed to capture any of this traffic last weekend and early this past week and care to share, we'd love to have a look. Otherwise, if you have any insight into what was going on, please share below or via our contact form. I'm always very curious about these traffic oddities.
---------------
Jim Clausing, GIAC GSE #26
jclausing --at-- isc [dot] sans (dot) edu
DShield Data Analysis: Taking a Look at Port 45740 Activity
At the SANS Internet Storm Center (ISC), handlers frequently analyze data submitted from DShield participants to determine activity trends and potential attacks. A few days ago on May 31st, I observed a small anomaly for port 45740 and decided to monitor it for the next 3 days or so. There was a huge spike in number of sources/day and reports/day recorded on May 31st as shown in Figure 1.
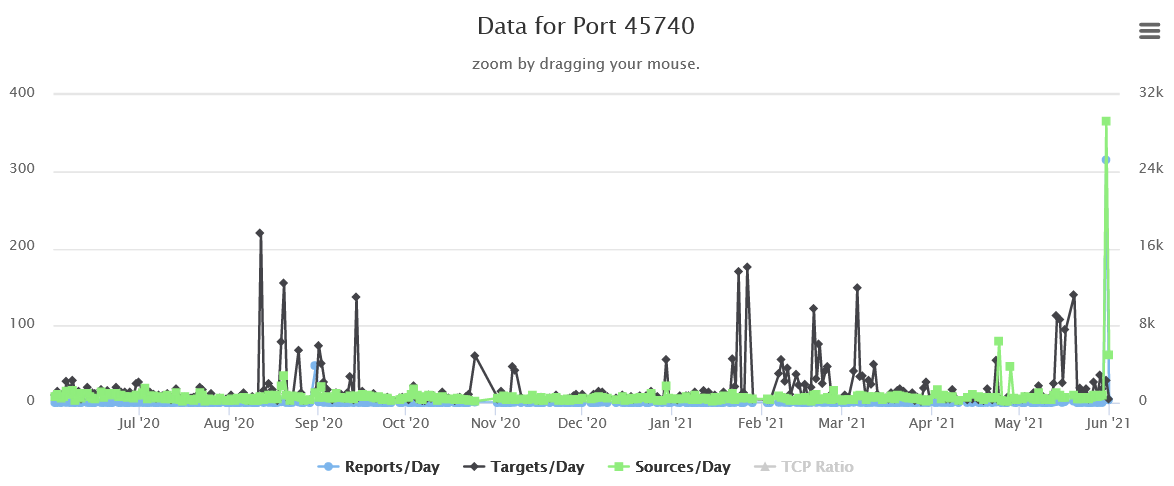
Figure 1: Port 45740 Activity (Taken June 1, 2021)
I did not receive any probes on this port on my sensors, but after digging into the DShield data, it was observed that the reported traffic to port 45740 were sent via UDP.
Over the next few days (till June 3, 2021), the number of sources/day and reports/day have dropped drastically as compared to May 31 (with reference to Figure 2). A check on Censys and Shodan did not yield any interesting findings, although there were some mentions of Distributed Hash Table (DHT) along with some IP addresses and port 45740 as a pair.
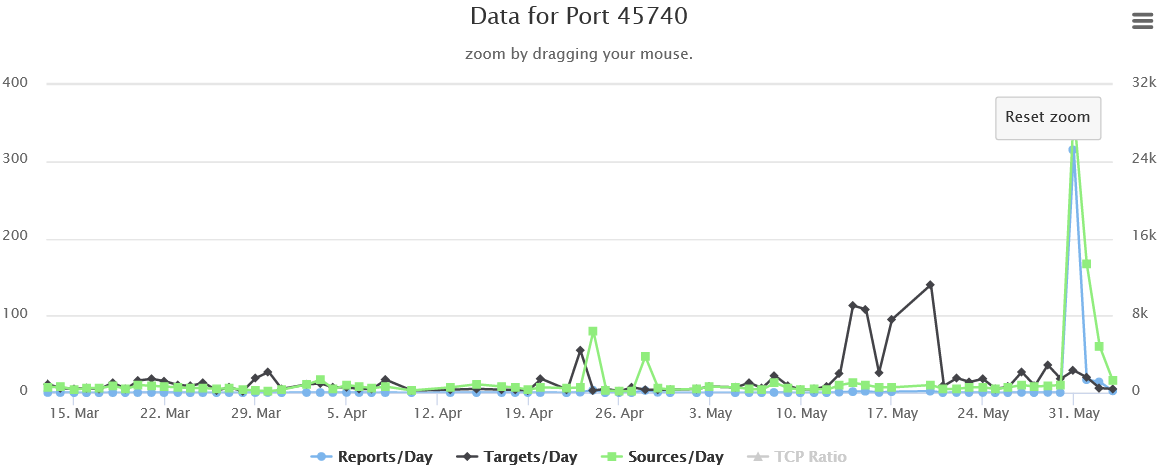
Figure 2: Port 45740 Activity (Taken June 3, 2021)
If anyone has any insights or information that could help shed light on this phenomenon, please comment down below, contact us via our contact page or e-mail us.
-----------
Yee Ching Tok, ISC Handler
Personal Site
Twitter


Comments