YARA XOR Strings: an Update
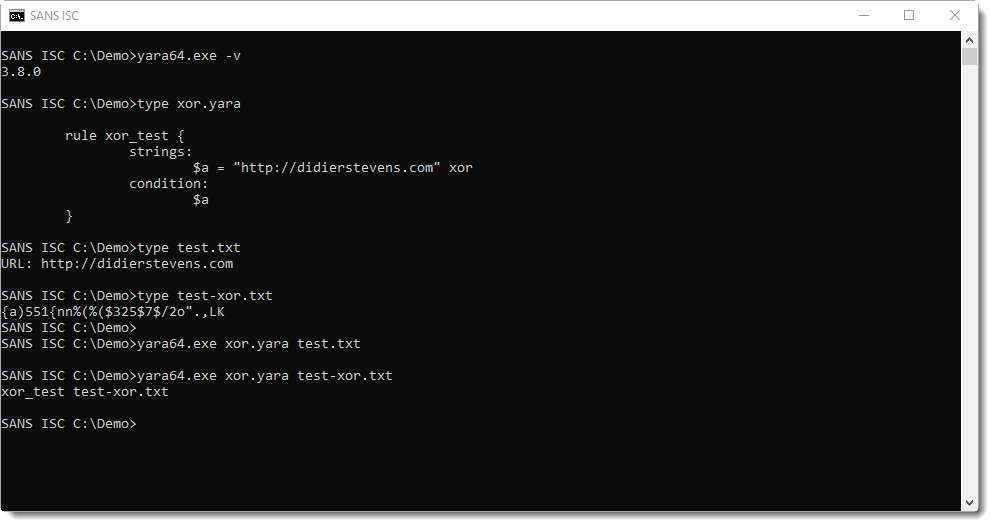
Almost a year ago, I reported on a new feature in YARA version 3.8.0: YARA XOR Strings. The new YARA xor keyword allows for the search of strings that are XOR-encoded with a one-byte key.
In that diary entry, I pointed out that using the xor modifier would result in not matching strings that are not xor-encoded (or encoded with key 0x00). Assuming this was the intended behavior, I did not report this as a bug.
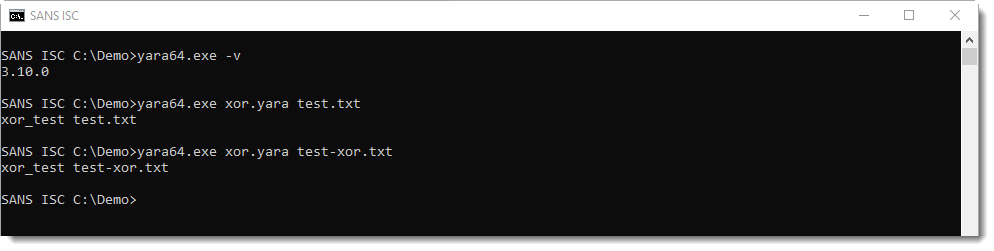
But for Victor, it was a bug. I missed this with the release of YARA 3.10.0 in may, but a bugfix was included for the xor modifier.
With version 3.8.0, XOR key 0x00 is not detected:
And with version 3.10.0, it is:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com
Video: Encrypted Sextortion PDFs
In this video, I show how to use my PDF tools together with QPDF and Poppler to deal with encrypted PDFs, like the sextortion PDFs that were submitted recently.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments