New IE 0-day in the wild
Qihoo 360 Technology, a Chinese internet security company, published a report for a new Internet Explorer zero-day exploit it has seen exploited in the wild by an (unmentioned) APT group. Qihoo 360 has reported this to Microsoft on 4/19/2018. We have no news from Microsoft.
The report can be found here (Standard Chinese).
Although the report does not contain much technical details, there is a diagram of the kill chain that we have translated here:
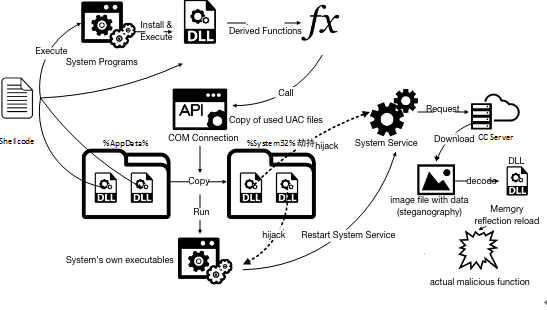
It seems that the initial attack, detected by Qihoo 360, used a Microsoft Office document containing a web page. The vulnerability seems to be in the Internet Explorer engine, and could thus be exploited via any application that uses the IE engine.
We will post more news as it becomes available.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com


Comments