Emails threatening DDoS allegedly from Phantom Squad
Introduction
As a follow-up to one of our June 2017 diaries asking people to forward us any DDoS threats, we received yet another example:
Date: Tuesday 2017-09-19 at 18:04 UTC
Subject: DDoS Warning
From: <uid101080@web.websupport.sk.>
Message-Id: <1505844251.007448.31360.nullmailer@me>
Hello, [removed]
FORWARD THIS MAIL TO WHOEVER IS IMPORTANT IN YOUR COMPANY AND CAN MAKE DECISION!
We are Phantom Squad
Your network will be DDoS-ed starting Sept 30st 2017 if you don't pay protection fee - 0.2 Bitcoin @ [removed].
If you don't pay by Sept 30st 2017, attack will start, yours service going down permanently price to stop will increase to 20 BTC and will go up 10 BTC for every day of attack.
This is not a joke.
Details
Since 2017-09-19, at least 4 people have tweeted about the same type of emails, supposedly from Phantom Squad:
- https://twitter.com/TProphet/status/910199852524478464
- https://twitter.com/willfull/status/910504944729559040
- https://twitter.com/drowningbynums/status/910774194803224581
- https://twitter.com/trbrink/status/910211259655704577
This feels like a scam using the notariety of Phantom Squad's name, because the group has gotten some fairly high-profile press coverage in recent years. In December 2015, Phantom Squad claimed responsibility for a DDoS attack against Xbox Live. A year later in December 2016, Phantom Squad was apparently involved in a DDoS attack against Steam. However, I haven't found any evidence yet this group is involved in small business extortion.
Wheter or not this email is legitimate or fake, they all use notariety of the group's name to make the threat sound plausible.
In our June 2017 diary about fake DDoS extortion emails, Johannes Ullrich provides some guidance for people that receive these types of messages. Tips include:
- Verify your DDoS plan: Do you have an agreement with an anti-DDoS provider? A contact at your ISP? If so, make sure everything is set up and working right.
- Attackers often run short tests before launching a DDoS attack. Can you find any evidence of that? Has there been a brief, unexplained traffic spike? If so, take a closer look. The threat is more serious if you detect an actual test, because the purpose of a test is often to assess the firepower needed to DDoS your network.
Final words
Thanks to everyone who already forwarded examples to us. As Johannes previously asked in June 2017, please continue to forward us any similar emails. We can always use the additional data.
A santized copy of our most current example can be found here. It's in a password-protected zip archive. If you don't know the password, look here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net
Email attachment using CVE-2017-8759 exploit targets Argentina
Introduction
On 2017-09-12, FireEye published a blog post about a zero-day exploit utilizing CVE-2017-8759. The vulnerability was fixed that same day with Microsoft's September 2017 Security Updates.
In FireEye's blog post, this exploit was used against Russian speakers to distribute FINSPY malware. By 2017-09-19, I ran across another email spoofing an Argentina government agency using a CVE-2017-8759 exploit to distribute Betabot malware.
Today's diary reviews the email, malware, and traffic associated with this most recent exploit for CVE-2017-8759.
The email and attachment
The email pretends to be from the Administracion Federal de Ingresos Publicos (AFIP) a Argentina government agency responsible for tax collection and administration. The message actually came from a commercial mail server on an IP address assigned to Gualberto Larrauri, an Argentina-based Internet service provider (ISP).
The message describes the attachment as a manual for the AFIP purchasing portal. The attachment is a zip archive, and that archive contains a Rich Text Format (RTF) file with .doc as the file extension. True to its word, the RTF file contains an annex to the official AFIP document covering the subject. It also contains an exploit for CVE-2017-8759. Merely opening the file using Microsoft Word will infect a vulnerable Windows computer.
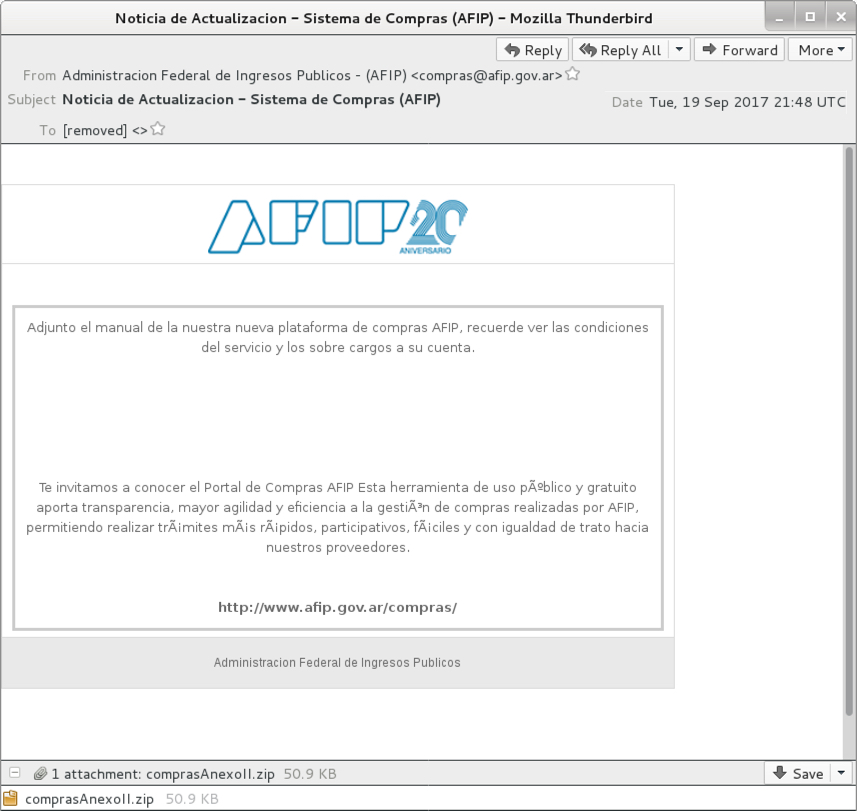
Shown above: Screenshot of the email.
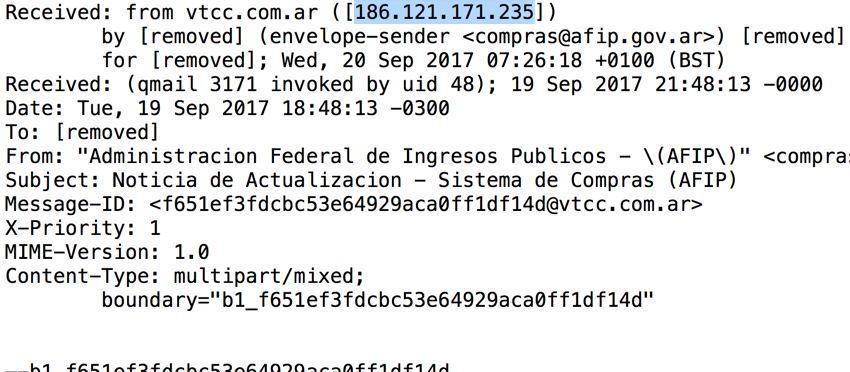
Shown above: Email headers indicate where the email actually came from.
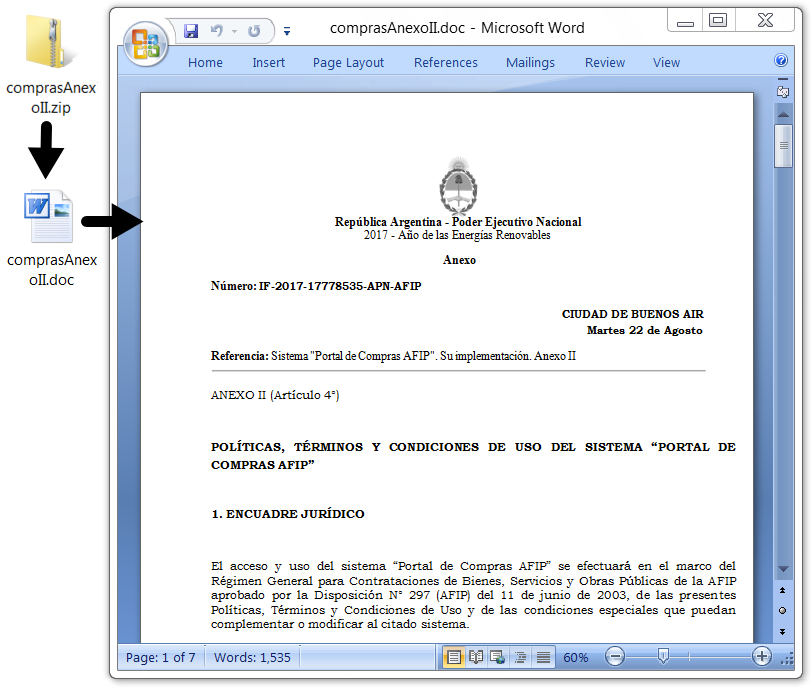
Shown above: The email attachment and extracted RTF document.
Follow-up malware
Opening the RTF document generated Powershell activity that retrieved a Windows executable. This follow-up executable triggered EmergingThreats alerts for Neurevt.A/Betabot when I infected a host in my lab. The malware was made persistent through a Windows registry update.
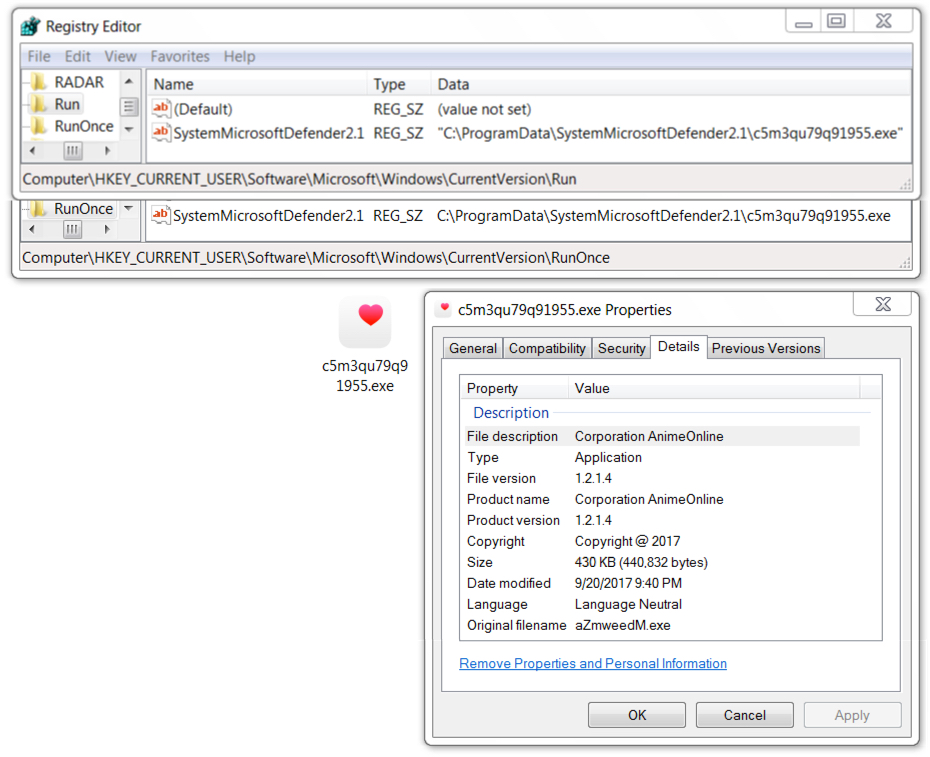
Shown above: Follow-up malware (Betabot) made persistent on the infected Windows host.
Network traffic
Infection traffic included HTTP requests for SOAP code injection, JavaScript, Powershell script, and a Windows executable over TCP port 8007. Post-infection activity consisted of HTTP POST requests over TCP port 80.
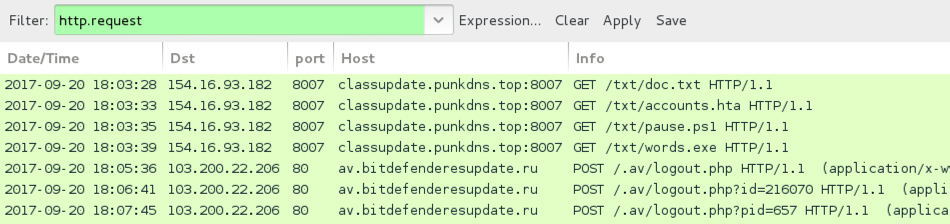
Shown above: Network traffic for this infection filtered in Wireshark.
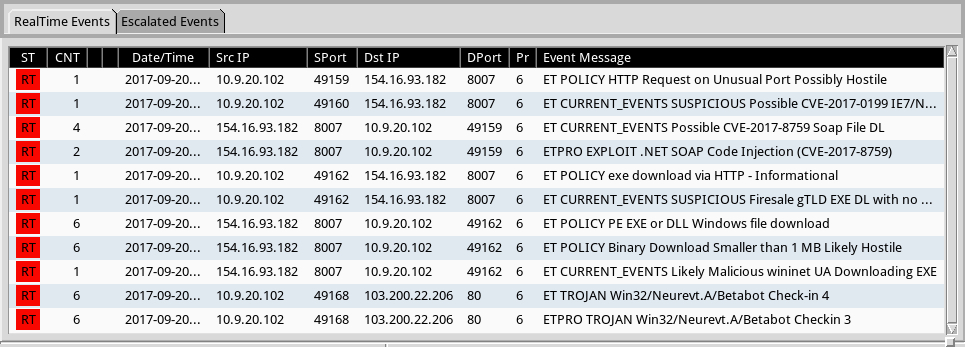
Shown above: Alerts from Sguil in Security Onion using Suricata with the EmergingThreats Pro ruleset.
Indicators of Compromise (IOCs)
Headers from the email:
- Received: from vtcc.com.ar ([186.121.171.235])
- Envelope-sender: <compras@afip.gov.ar>
- Message-ID: <f651ef3fdcbc53e64929aca0ff1df14d@vtcc.com.ar>
- Date: Tuesday, 2017-09-19 at 21:48 UTC
- From: "Administracion Federal de Ingresos Publicos - (AFIP)" <compras@afip.gov.ar>
- Subject: Noticia de Actualizacion - Sistema de Compras (AFIP)
File hashes:
SHA256 hash: 7bd46284dabf1f400102aa35e123eb2ffe2838560fbc016ba4f2cd376742004c
- File size: 52,132 bytes
- File type: Zip archive
- File name: comprasAnexoII.zip
- File description: Email attachment
SHA256 hash: 4a07c6f26ac9feadbd78624d4e063dfed54e972772e5ee34c481bdb86c975166
- File size: 286,981 bytes
- File type: Rich Text Format (RTF) file
- File name: comprasAnexoII.doc
- File description: RTF file with CVE-2017-8759 exploit
SHA256 hash: 610e6611b3b2e3bd85173cba76bf069fb7134b86f533141f79811fcc29d62b33
- File size: 440,832
- File type: PE32 executable
- File location: hxxp://classupdate.punkdns.top:8007/txt/words.exe
- File location: C:\ProgramData\SystemMicrosoftDefender2.1\[random characters].exe
- File description: Follow-up malware, Neurevt.A (Betabot)
Infection traffic:
- 154.16.93.182 port 8007 - classupdate.punkdns.top:8007 - GET /txt/doc.txt
- 154.16.93.182 port 8007 - classupdate.punkdns.top:8007 - GET /txt/accounts.hta
- 154.16.93.182 port 8007 - classupdate.punkdns.top:8007 - GET /txt/pause.ps1
- 154.16.93.182 port 8007 - classupdate.punkdns.top:8007 - GET /txt/words.exe
Post-infection traffic:
- 103.200.22.206 port 80 - av.bitdefenderesupdate.ru - POST /.av/logout.php
- 103.200.22.206 port 80 - av.bitdefenderesupdate.ru - POST /.av/logout.php?id=[various numbers]
Final words
As I write this, nine days have passed since Microsoft released its update to address CVE-2017-8759. The associated exploit is no longer a zero-day. If your organization follows best security practices, you should be fine.
However, many organizations are notoriously slow to apply these updates. Be aware this exploit is active in the wild. I'm sure it will eventually find its way to wide-scale distribution through malicious spam.
A copy of the email, taffic, and associated malware for today's diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments