Investigation of BitTorrent Sync (v.2.0) as a P2P Cloud Service (Part 4 ? Windows Thumbnail Cache, Registry, Prefetch Files, and Link Files artefacts)
[This is fourth guest diary by Dr. Ali Dehghantanha. Previous diaries in the series are:
- Investigation of BitTorrent Sync (v.2.0) as a P2P Cloud (Part 1)
- Investigation of BitTorrent Sync (v.2.0) as a P2P Cloud Service (Part 2 ? Log Files artefacts)
- Investigation of BitTorrent Sync (v.2.0) as a P2P Cloud Service (Part 3 ? Physical Memory artefacts)
If you would like to propose a guest diary, please let us know]
Continuing earlier posts on investigation of BitTorrent Sync version 2.0, this post explains remaining artefacts of user activities from Thumbnail Cache, Registry, Prefetch Files, and Link Files.
Thumbnail cache
Analysis of the Windows thumbcache (stored under %AppData%\Local\Microsoft\Windows\Explorer) recovered copies of thumbnail images for the BitTorrent Sync client application and its download site (e.g., BitTorrent Sync logo and image icons), indicative of BitTorrent Sync usage. Examinations of the thumbnail cache from the file synchronisation only revealed copies of thumbnail images for the synced files from the Windows 8.1 and Mac OS VMs. We could discern the thumbnail cache from the ‘folder’ table field (of the ‘files’ table) which made reference to ‘BitTorrent Sync’ in the /private/var/folders[Random subfolder]/[Random subfolder]/C/com.apple.QuickLook.thumbcache/index.sqlite database on Mac OSX. The timestamp references recorded alongside the thumbnail cache would assist a practitioner to identify the last accessed or deletion (only on a Mac OSX; see Figure 1) date of a sync file or folder.
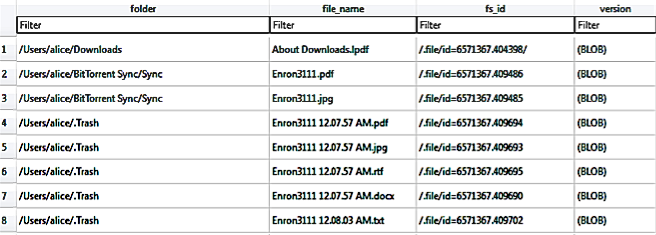
Figure 1: Thumbnail information recovered from the index.sqlite database of Mac OS’ thumbcache folder.
Windows Registry
Analysis of the HKLM hive determined that the BitTorrent Sync installation could be detected from the presence of the HKLM\SOFTWARE\BitTorrent\Sync key, and the installation path could be discerned from the ‘SyncPath’ subkey. In addition, the HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BitTorrent Sync key could provide supporting information for installation such as the display icon’s path, display name, BitTorrent Sync version installed, installation and uninstaller paths, and other entries of relevance. Similar to any other Windows application, when the BitTorrent Sync client application is started, there are full path reference for the BitTorrent Sync executable file in HKU\<SID>\Software\Classes\Local Settings\Software\Microsoft\Windows\Shell\MuiCache, indicative of recent BitTorrent Sync usage. Further evidence to indicate the client application usage could be ascertained from the occurrence of ‘BitTorrent Sync: ""%Program Files%\BitTorrent Sync\BitTorrent Sync.exe", “/MINIMIZED"’ entry alongside the last executed time in Software\Microsoft\Windows\CurrentVersion\Run. Another registry key of forensic interest is the Software\Microsoft\Windows\CurrentVersion\Explorer\ComDig32, which keeps track of a list of filename references (e.g., filenames for the executable and synced files) associated with the BitTorrent Sync client application as well as the timestamp information during the last usage. According to Carvey (2014), the ‘CIDSizeMRU’ (MRU is the abbreviation for Most-Recently-Used) subkey maintains a list of recently used applications, the ‘OpenSaveMRU’ registry subkey records list of files that have been opened or saved within a Windows shell dialog box, and the ‘LastVisitedMRU’ subkey is responsible for tracking specific executable files used by an application to open the files documented in the ‘OpenSaveMRU’ subkey. Other evidence indicating the BitTorrent Sync client application usage includes the presence of entries referencing the link file as well as the last executed time in Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist.
Prefetch files
Examination of the prefetch files located two prefetch files for BitTorrent Sync, namely ‘BITTORRENT_SYNC.EXE.pf’ and ‘BITTORRENT SYNC.exe.pf’. Amongst the information of forensic interest recoverable from these files include the executable path, the number of times the application has been loaded, as well as the last run time which are useful to supplement timeline analysis. However, no prefetch instance was located for the synced files in our experiments. The presence of the prefetch files after uninstallation implies that there will be BitTorrent Sync references remaining in the prefetch files to indicate its use on the client device.
Link files
Link (.lnk) files are shortcut metadata files used by Windows to maintain a list of linked paths relating to a file (commonly the paths where the original files are located), associated timestamps (created, written, and last accessed times), and file sizes (original and modified) which are useful to identify the origin of a file. An inspection of the directory listings located instances of link file for %Program Files (x86)%\BitTorrent Sync\BitTorrent Sync.exe at %Users%\Public\Desktop\BitTorrent Sync.lnk and %Program Data%\Microsoft\Windows\Start Menu\BitTorrent Sync.lnk, and its presence may be indicative of BitTorrent Sync installation.
--
Bojan
@bojanz


Comments