Unpatched Vulnerability in Firefox used to Attack Tor Browser
Update: Mozilla now released Firefox 50.0.2 to fix this issue, and the tor project released the corresponding tor browser 6.0.7.
"Tor Browser," an easy to use package of Firefox and Tor is currently being attacked using a so far unpatched vulnerability. The Javascript-based exploit was first described on the Tor mailing list [1]. With the exploit being public now, it is likely only a matter of time to see this exploit used against Firefox outside of Tor.
Mozilla is working on a patch. And Tor Browser 6.0.7 which will hopefully be released later today is scheduled to include the fix.
Until then: Best not to use Firefox if you can help it. The current version of Firefox, 50.0.1, which was released on Monday, is still vulnerable. While the exploit hasn't been spotted yet outside of Tor, expect it to show up by the time you read this.
An analysis of the shell code used in the exploit by "Wack0" concluded that the code is very similar to an exploit used by law enforcement in 2013 against an older version of Firefox/Tor Browser. [2]
[1] https://lists.torproject.org/pipermail/tor-talk/2016-November/042639.html
[2] https://gist.github.com/Wack0/0fedb57beb90aae7f526ac6235ba85ef
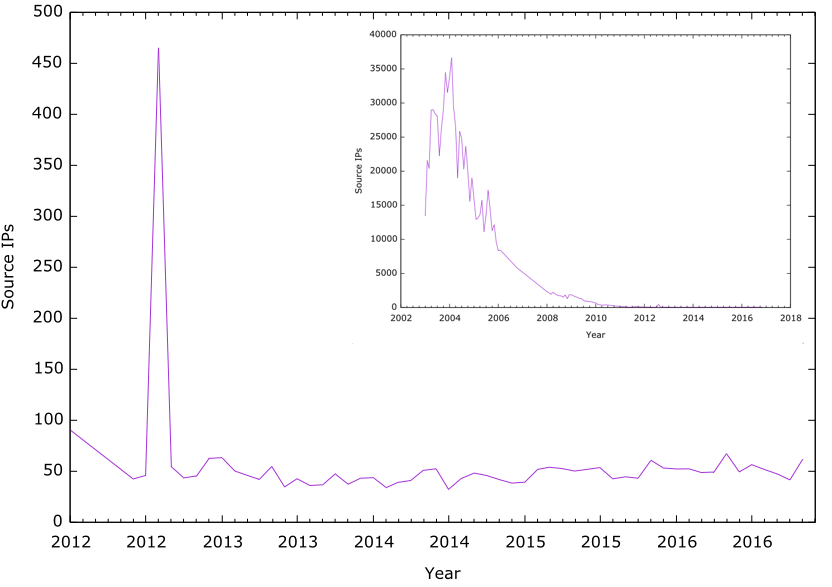
Take Back Wednesday? SQL Slammer... still alive but barely kicking
Got a couple of reports recently about an increase in port 1434 scanning for the infamous "Slammer" (aka "Saphire") MS-SQL Server vulnerability. Sad to say: It looks like it never went away... There appears to be still a "background" of about 50 source IPs/day that scan for port 1434. Now this is way down from the numbers we had in 2003/2004 (20-30,000 sources per day). But to put it in perspective: This was still about an order of magnitude lower than what we see for Mirai now. So let's look at this again in 13 years, and see how many DVRs are still sending Mirai style scans. Just like with Slammer, all it takes is a couple of them to survive to immediately infect new systems as they come online.
If you want a list of yesterday's sources, check here: https://isc.sans.edu/dailysources.html?mintargetport=1434&maxtargetport=1434
After removing some of the research scanners (Shodan, Shadowserver, Quadmetrics), I am left with this list:
ASN | IP Address | CT | Network Name 278 | 132.248.168.13 | MX | Universidad Nacional Autonoma de Mexico, MX 3462 | 218.161.5.128 | TW | HINET Data Communication Business Group, TW 3786 | 211.171.255.209 | KR | LGDACOM LG DACOM Corporation, KR 4134 | 123.149.204.221 | CN | CHINANET-BACKBONE No.31,Jin-rong Street, CN 4816 | 113.108.10.31 | CN | CHINANET-IDC-GD China Telecom (Group), CN 4837 | 61.180.150.241 | CN | CHINA169-BACKBONE CNCGROUP China169 Backbone, CN 5650 | 71.254.156.157 | US | FRONTIER-FRTR - Frontier Communications of America, Inc., US 6739 | 217.217.53.185 | ES | ONO-AS Cableuropa - ONO, ES 7018 | 12.197.61.82 | US | ATT-INTERNET4 - AT&T Services, Inc., US 7029 | 66.251.67.77 | US | WINDSTREAM - Windstream Communications Inc, US 7162 | 200.98.136.66 | BR | Universo Online S.A., BR 7418 | 200.54.147.125 | CL | TELEFÓNICA CHILE S.A., CL 7470 | 61.90.140.83 | TH | TRUEINTERNET-AS-AP TRUE INTERNET Co.,Ltd., TH 7643 | 203.162.174.119 | VN | VNPT-AS-VN Vietnam Posts and Telecommunications (VNPT), VN 7922 | 50.241.98.181 | US | COMCAST-7922 - Comcast Cable Communications, LLC, US 8342 | 81.176.67.100 | RU | RTCOMM-AS , RU 8560 | 74.208.99.70 | US | ONEANDONE-AS Brauerstrasse 48, DE 9808 | 120.193.156.74 | CN | CMNET-GD Guangdong Mobile Communication Co.Ltd., CN 11014 | 190.111.250.62 | AR | CPS, AR 11650 | 64.250.212.157 | US | PLDI - Pioneer Long Distance Inc., US 15311 | 200.42.174.194 | CL | Telefonica Empresas, CL 16276 | 94.23.191.55 | FR | OVH , FR 16509 | 54.238.213.183 | US | AMAZON-02 - Amazon.com, Inc., US 17676 | 61.206.152.38 | JP | GIGAINFRA Softbank BB Corp., JP 19108 | 173.81.219.56 | US | SUDDENLINK-COMMUNICATIONS - Suddenlink Communications, US 27892 | 150.185.222.111 | VE | Universidad del Zulia, VE 29073 | 89.248.167.131 | NL | QUASINETWORKS , NL 60781 | 81.171.7.169 | NL | LEASEWEB-NL Netherlands, NL
No idea if these are actually infected systems, or if these systems are just scanning for various "research projects" as well. Right now, none of the systems appears up.


Comments