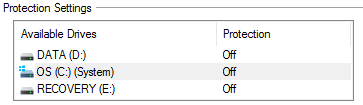
Windows 10 and System Protection for DATA Default is OFF
I had the unfortunate consequences of a main hard drive failure this week and I had to rebuild my laptop. However, after I restored Windows 7 and then upgraded to Windows 10 and started to patch my laptop, I ran into some issues and wanted to go back to a previous snapshot and found out that System Restore was empty. I figured this issue with Windows 10 had been fixed but that still isn't the case. Many of you have probably upgraded to Windows 10 and it would be a good idea to verify your settings to make sure System Protection is enabled.
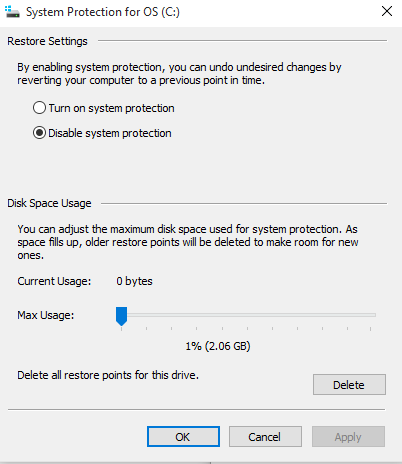
Here is how to check and if necessary, enable System Protection:
Select 
Select Turn on system protection to enable System Restore and some disk space (i.e. 10 GB)
Over the years, System Protection has been in many cases a useful tool especially when installing failed patches or applications to be able to go back to an earlier and stable version.
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
OpenSSL 1.0.2 Advisory and Update
On the 26 ISC handler Rob posted a onliner that a major flaw exposed TLS traffic (CVE-2016-0701) where an attacker could decrypt and obtain information on traffic that you would deem secure. "More recently (in version 1.0.2) support was provided for generating X9.42 style parameter files such as those required for RFC 5114 support." [2]
This serious vulnerability affects OpenSSL version 1.0.2 and should upgrade to version 1.0.2f. Version 1.0.1 is not affected because support for X9.42 style parameter has not been implemented. If you are upgrading from source code, the latest version can be downloaded here or check your Linux version for package update.
[1] https://isc.sans.edu/diary.html?date=2016-01-26
[2] https://www.openssl.org/news/secadv/20160128.txt
[3] https://www.openssl.org/source/
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments