USB cleaning device for the masses
For so long, USB keys have been a nice out-of-band infection vector. People like goodies and people like to plug those small pieces of plastic into their computers. Even if good solutions exists (like BitLocker - the standard solution provided by Microsoft), a lot of infrastructure are not protected against the use of rogue USB keys for many good or obscure reasons.
There are also multiple reasons to receive USB keys: from partners, customers, contractors, vendors, etc. The best practice should be to scan any suspicious device against malicious documents but how to achieve this in a safe AND not boring way. If you propose a tool that is easy to use, you will increase your chances to have it adopted by more people!
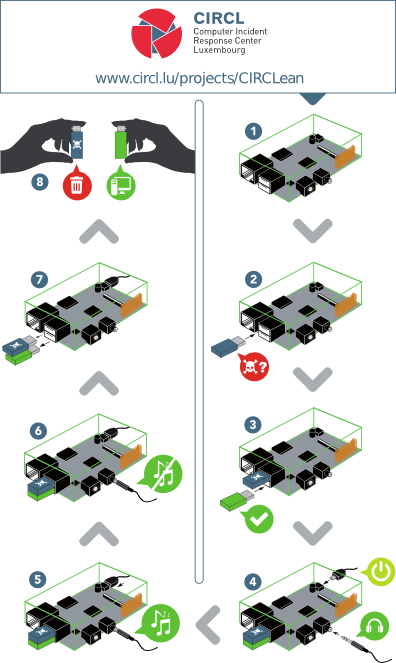
The CIRCL (Computer Incident Response Center Luxembourg) is coming from a very small country but they are very active and renowned. They developed a tool to sanitize USB keys. It's so easy that even non-tech people can use it! The project is called "CIRCLean". It's a piece of software that you install on an inexpensive Raspberry computer. You connect the suspicious device in the USB port A, a clean USB device in port B, power the box and wait for the process to be completed (depending on the amount of data to analyze). One picture is worth a thousand words:
What does it do? Multiple operations are performed on files, based on their MIME type. Example: Word files are converted to PDF then to HTML. Other files are renamed and prepended with a "DANGEROUS_" prefix. Once sanitized (or non dangerous), files are copied to the destination USB key. The code is available on their github repository.
Xavier Mertens
ISC Handler - Freelance Security Consultant
PGP Key


Comments