May 2015 Microsoft Patch Tuesday Summary
Overview of the May 2015 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS15-043 | Cumulative Security Update for Internet Explorer (Replaces MS15-032 ) |
|||||
| CVE-2015-1658, CVE-2015-1684, CVE-2015-1685, CVE-2015-1686, CVE-2015-1688, CVE-2015-1689, CVE-2015-1691, CVE-2015-1692, CVE-2015-1694, CVE-2015-1703, CVE-2015-1704, CVE-2015-1705, CVE-2015-1706, CVE-2015-1708, CVE-2015-1709, CVE-2015-1710, CVE-2015-1711, CVE-2015-1712, CVE-2015-1713, CVE-2015-1714, CVE-2015-1717, CVE-2015-1718 | KB 3049563 | . | Severity:Critical Exploitability: 1 |
Critical | Critical | |
| MS15-044 | Vulnerabilities in Microsoft Font Drivers Could Allow Remote Code Execution (ReplacesMS13-034 MS13-082 MS15-023 ) |
|||||
| CVE-2015-1670 CVE-2015-1671 | KB 3057110 | . | Severity:Critical Exploitability: 1 |
Critical | Critical | |
| MS15-045 | Vulnerability in Windows Journal Could Allow Remote Code Execution (Replaces MS14-038 ) |
|||||
| CVE-2015-1675 CVE-2015-1695 CVE-2015-1696 CVE-2015-1697 CVE-2015-1698 CVE-2015-1699 |
KB 3046002 | . | Severity:Critical Exploitability: 2 |
Critical | Critical | |
| MS15-046 | Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (ReplacesMS13-085 MS15-012 MS15-022 MS15-033 ) |
|||||
CVE-2015-1682 CVE-2015-1683 |
KB 3057181 | . | Severity:Important Exploitability: 1 |
Critical | Important | |
| MS15-047 | Vulnerabilities in Microsoft SharePoint Server Could Allow Remote Code Execution (Replaces MS12-066 MS15-022 ) |
|||||
CVE-2015-1700 |
KB 3058083 | . | Severity:Important Exploitability: 2 |
Important | Critical | |
| MS15-048 | Vulnerabilities in .NET Framework Could Allow Elevation of Privilege (Replaces MS12-038 MS13-015 MS13-040 MS13-082 MS14-009 ) |
|||||
CVE-2015-1672 CVE-2015-1673 |
KB 3057134 | . | Severity:Important Exploitability: 3 |
Important | Important | |
| MS15-049 | Vulnerability in Silverlight Could Allow Elevation of Privilege (Replaces MS14-014 ) |
|||||
CVE-2015-1715 |
KB 3058985 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-050 | Vulnerability in Service Control Manager Could Allow Elevation of Privilege | |||||
CVE-2015-1702 |
KB 3055642 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-051 | Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (ReplacesMS15-023 ) |
|||||
CVE-2015-1676 CVE-2015-1677 CVE-2015-1678 CVE-2015-1679 CVE-2015-1680 CVE-2015-1701 |
KB 3057191 | vuln. public. | Severity:Important Exploitability: 0 |
Important | Important | |
| MS15-052 | Vulnerability in Windows Kernel Could Allow Security Feature Bypass (Replaces MS15-010 ) |
|||||
| CVE-2015-1674 | KB 3050514 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-053 | Vulnerabilities in JScript and VBScript Scripting Engines Could Allow Security Feature Bypass (ReplacesMS11-031 MS12-056 ) |
|||||
CVE-2015-1684 CVE-2015-1686 |
KB 3057263 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-054 | Vulnerability in Microsoft Management Console File Format Could Allow Denial of Service | |||||
CVE-2015-1681 |
KB 3051768 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-055 | Vulnerability in Schannel Could Allow Information Disclosure (ReplacesMS15-031 ) |
|||||
| CVE-2015-1716 | KB 3061518 | . | Severity:Important Exploitability: 1 |
Important | Important | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urt practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threatatches.
Angler exploit kit pushes new variant of ransomware
Introduction
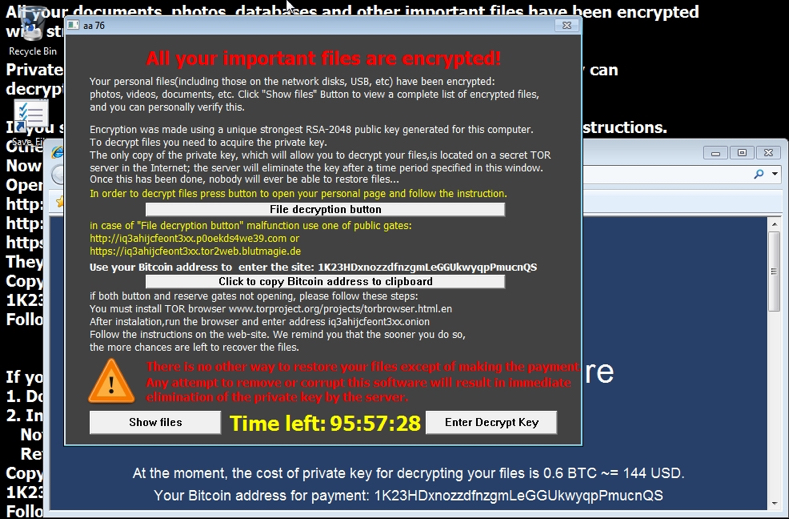
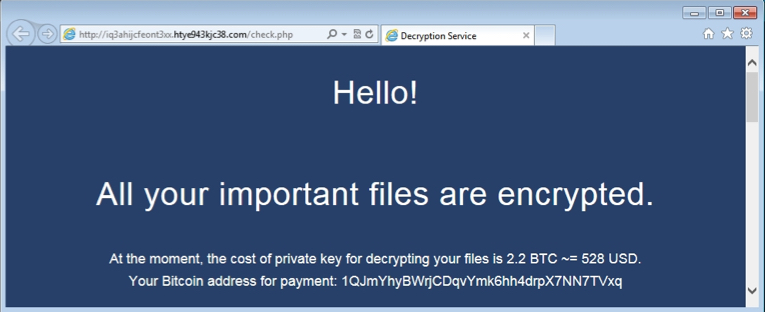
The Angler exploit kit (EK) is being used to push a new variant of TeslaCrypt/AlphaCrypt ransomware. I've been documenting cases of Angler EK pushing AlphaCrypt in recent weeks [1][2][3]. Last week on 2015-05-07, I started seeing a new variant [4]. This new variant has a popup window that uses CTB-Locker-style instructions.
As seen below, this variant doesn't provide a name for itself in the decrypt instructions.
The same malware sample used a different bitcoin address for each host it infected.
Traffic Characteristics of this New Ransomware Variant
The traffic appears identical to what we've seen with previous infections from TeslaCrypt and AlphaCrypt. A few hours ago I infected a host from a site using Angler EK and received similar alerts from the network traffic.

Shown above: Alerts from monitoring the infection with Security Onion.

Shown above: HTTP traffic from the infection. Click on the image to see it full-size.
A sample of the ransomware can be found at:
https://malwr.com/analysis/MjE3ODRlYzc1MmQ2NGUyNDkyYWNkNWM0OWZiOGVjYzE/
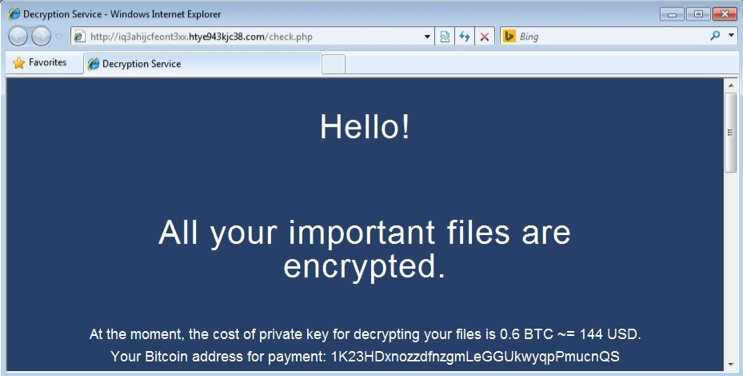
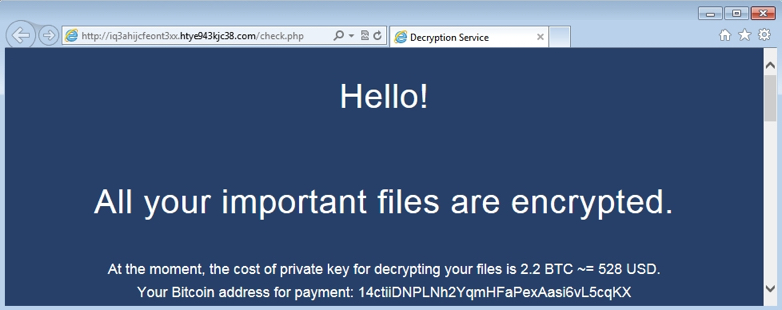
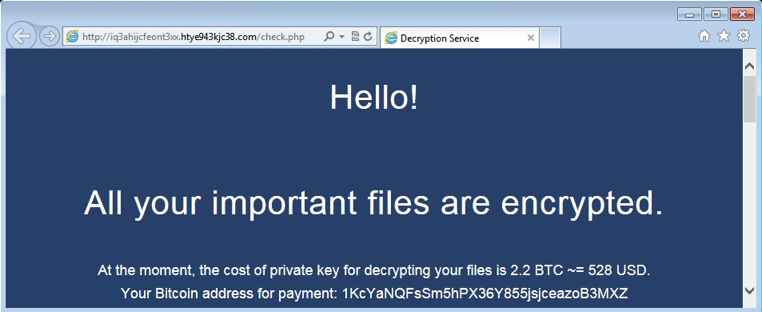
I infected 4 different hosts with Angler EK in a 5-hour timeframe and received the same ransomware. It was the same file with the same hash each time. However, the bitcoin address for the ransom payment was different for each infected host. Shown below are decrypt pages from the other 3 hosts:
Here are the bitcoin addresses from these infected hosts:
- 14ctiiDNPLNh2YqmHFaPexAasi6vL5cqKX
- 1K23HDxnozzdfnzgmLeGGUkwyqpPmucnQS
- 1KcYaNQFsSm5hPX36Y855jsjceazoB3MXZ
- 1QJmYhyBWrjCDqvYmk6hh4drpX7NN7TVxq
Pcap files of the infection traffic (Angler EK and the post-infection) are available at:
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-01.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-02.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-03.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-04.pcap
Final Words
From what I can tell, TeslaCrypt and AlphaCrypt are very similar to CryptoLocker. This new, unnamed variant appears to be another evolution from this family of ransomware.
I've been seeing a lot of Angler EK lately. In recent weeks, more often than not, it's been pushing ransomware. Since 2015-05-07, I've only seen this new variant.
---
Brad Duncan, Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://malware-traffic-analysis.net/2015/04/30/index.html
[2] http://malware-traffic-analysis.net/2015/05/06/index.html
[3] http://malware-traffic-analysis.net/2015/05/07/index.html
[4] http://malware-traffic-analysis.net/2015/05/07/index2.html


Comments