Odd Vanishing Signatures in OS X XProtect
With OS X Snow Leopard, Apple for the first time introduced its own anti malware technology, XProtect. Ever since then, Apple has been pushing new signatures, and XProtect itself has undergone some subtle changes allowing it to pull signature updates more frequently. The list of signatures is still rather small, but unlike other OS X anti virus software, which covers Windows malware as well as OS X malware, XProtect only covers OS X malware. At this point, two larger "families" of OS X malware emerged: The fake anti virus software MacDefender and the malicious "flash updater" Flashback.
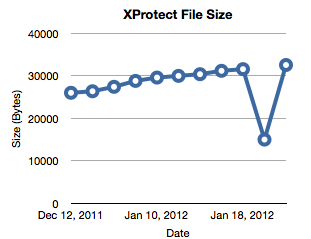
Ever since late last year, I am running a cron job on one of my Macs to watch for XProtect updates. The updates are delivered "silently", but the cron job keeps monitoring the definition file and keeps a copy of each version.
Ever since late last year, I am running a cron job on one of my Macs to watch for XProtect updates. The updates are delivered "silently", but the cron job keeps monitoring the definition file and keeps a copy of each version.
When reviewing the files yesterday, I found an odd behavior: On February 4th, the file "shrunk" by almost half. Instead of 15 signatures, the file contained only 6. On February 7th, the file went back to its old size. Has anybody else seen this? You can find the file in /System/Library/CoreServices/CoreTypes.bundle /Contents/Resources/XProtect.plist . It is a readable XML file. The current size of my file is 32516 Bytes.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter


Comments